As we have seen in the first part of AWS Penetration Testing Series the Basics of AWS S3 Bucket Penetration Testing in which we explained about what is Amazon S3 bucket and for the different purposes it can be used, in the second part Hands-on AWS S3 Bucket Vulnerabilities we learned about vulnerabilities in AWS S3 Bucket and in this part we will see how an attacker can claim AWS S3 buckets by exploiting account takeover vulnerability.
While performing reconnaissance and information gathering of any target application if you find a page that is displaying 404 Not Found on the web page. Observe the error displayed on that page in the browser.
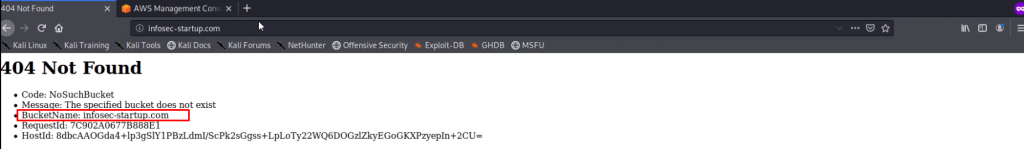
The above error shows the S3 BucketName: infosec-startup.com in which the entire data of the application had been hosted. If the developer deleted the entire data and S3 bucket i.e here (infosec-startup.com) from AWS console which was bound to that particular domain name but the CNAME records from the ROUTE53 are still pending to be removed in this case an attacker can claim this unclaimed S3 bucket name by using any other AWS account. This can lead an attacker to exploit S3 bucket account takeover vulnerability
Requirements to Takeover the AWS S3 Bucket:
Once an attacker has the following details:
- Unclaimed S3 bucket name:
- The region used by that bucket:
- To claim the S3 bucket an attacker must know that, which region was used by the victim to create this bucket.
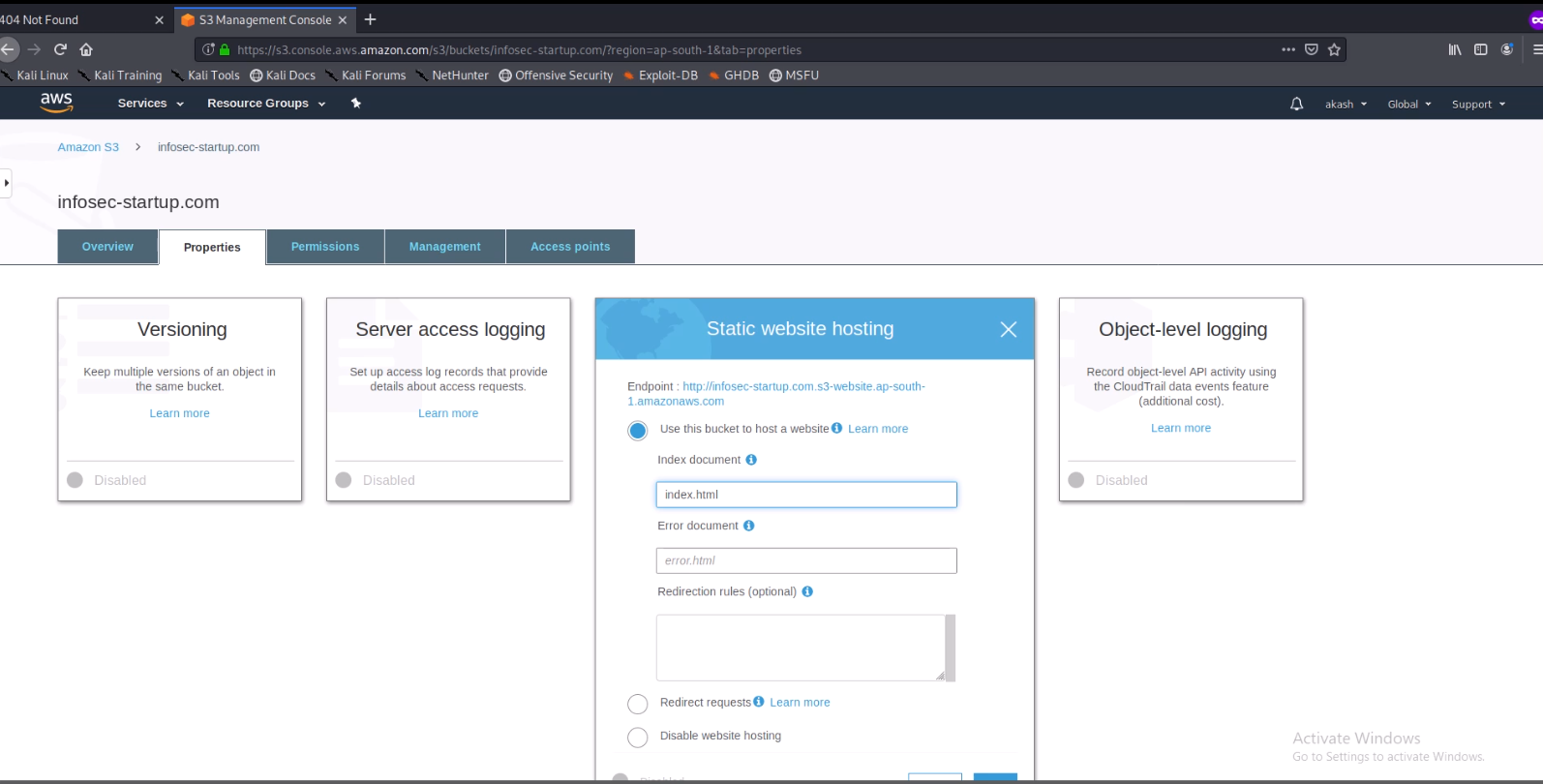
- To find the region of the bucket you can use CNAME lookup services
- Visit https://mxtoolbox.com/CNAMELookup.aspx and enter your bucket name here.
Ready to takeover over the S3 bucket !!
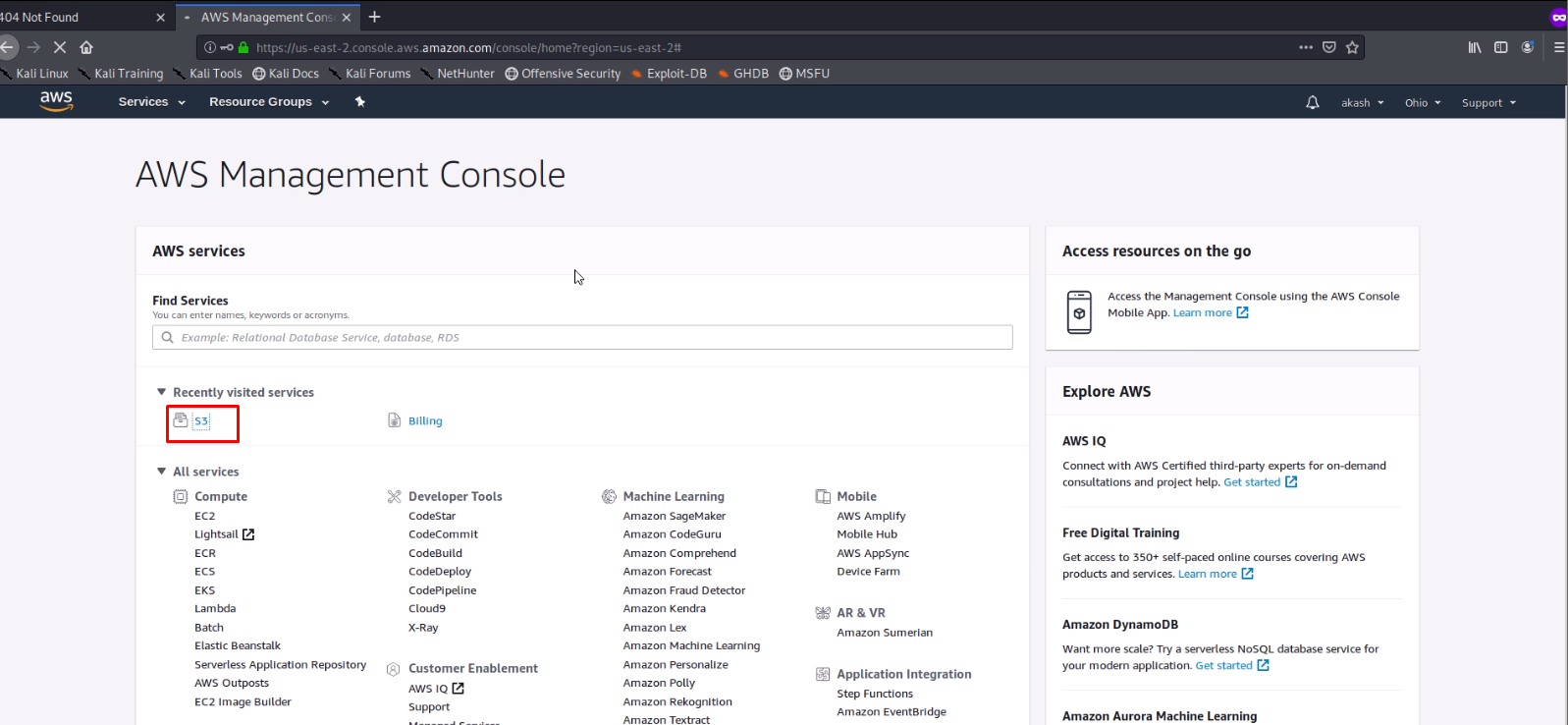
1. Login into your AWS Management Console and Click on S3
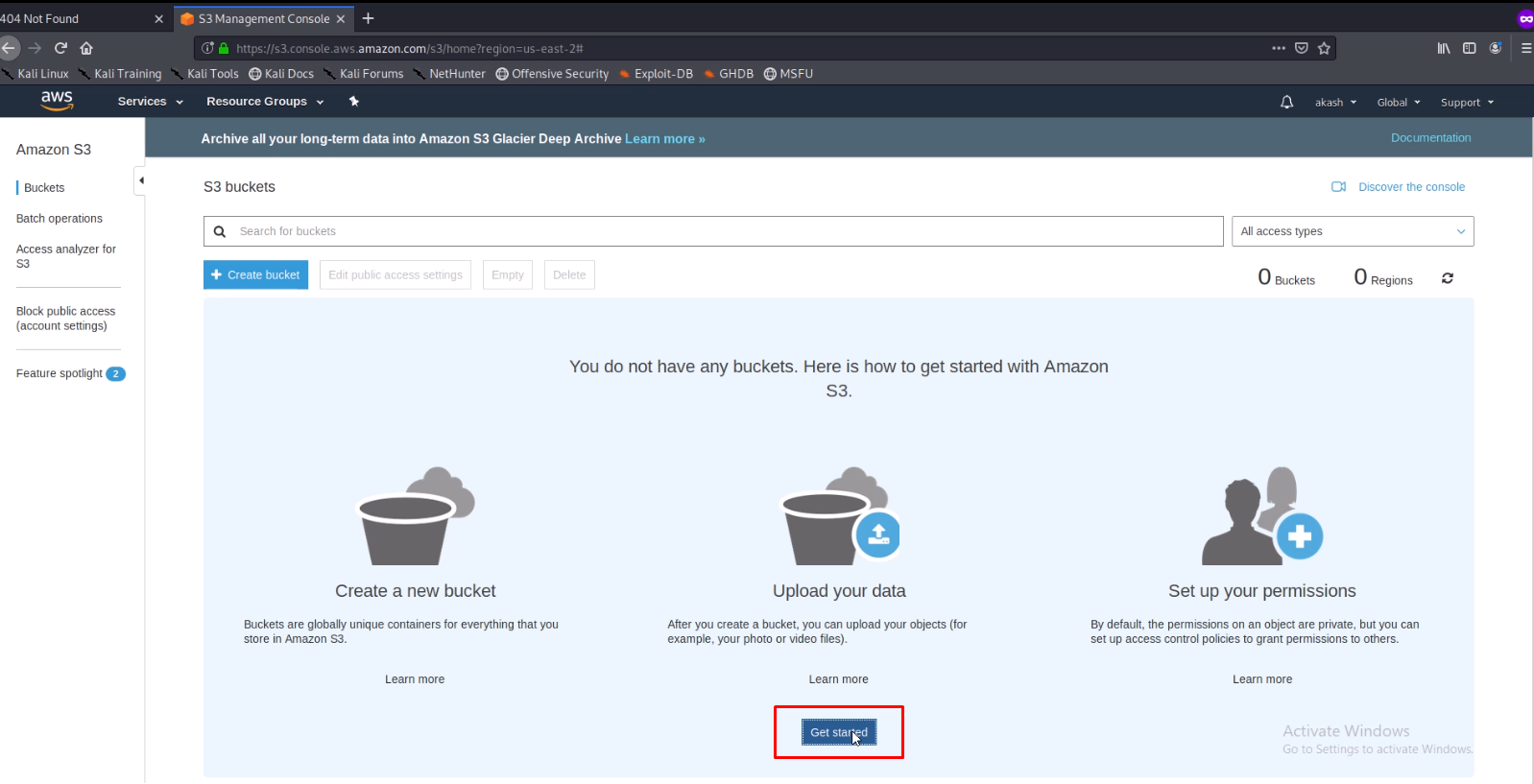
2. Click on Get started
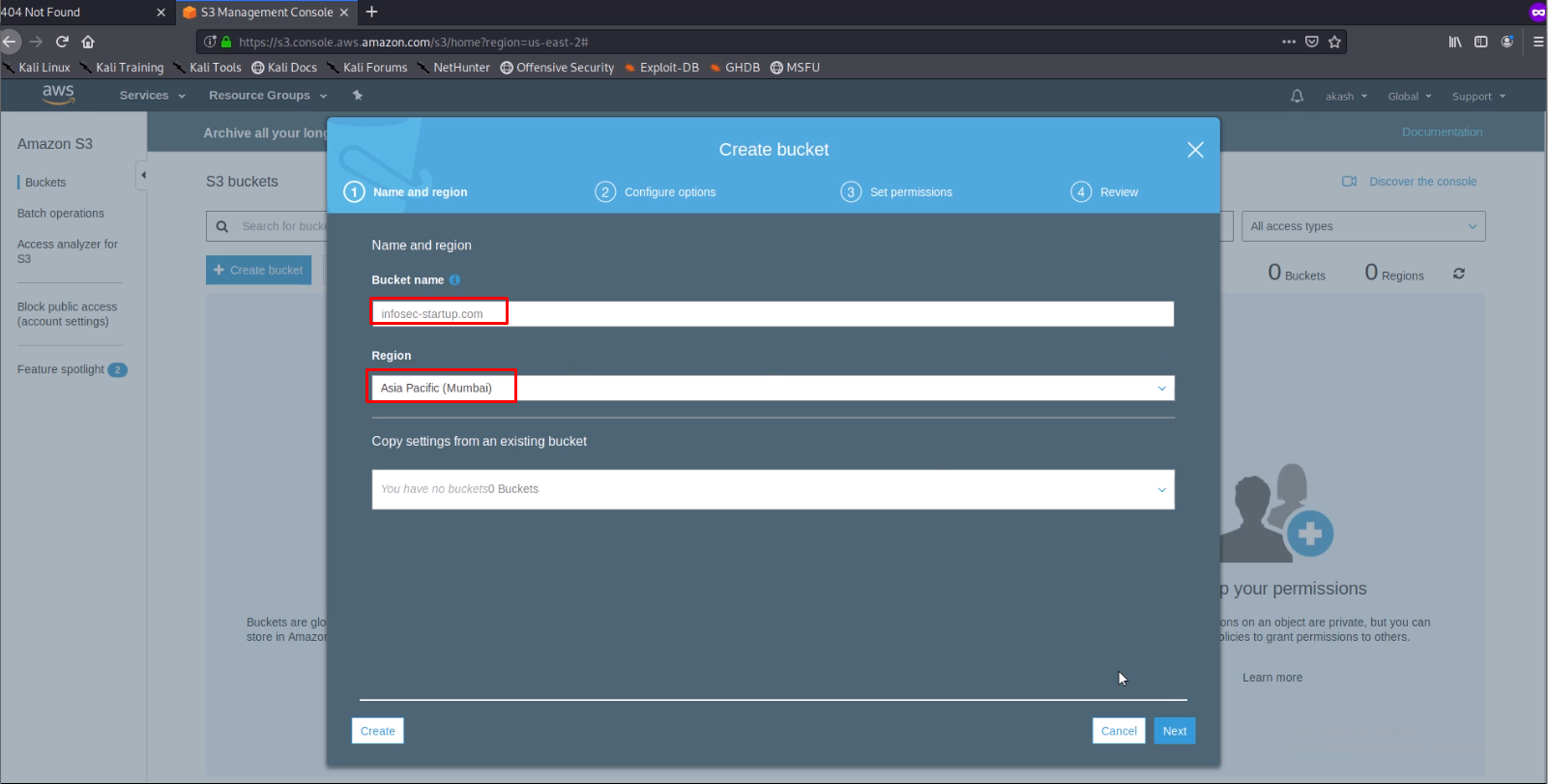
3. Enter the Bucket name and Region Name that we found previously and click on next
4. Continue clicking on the Next option button and in the end click on finish.
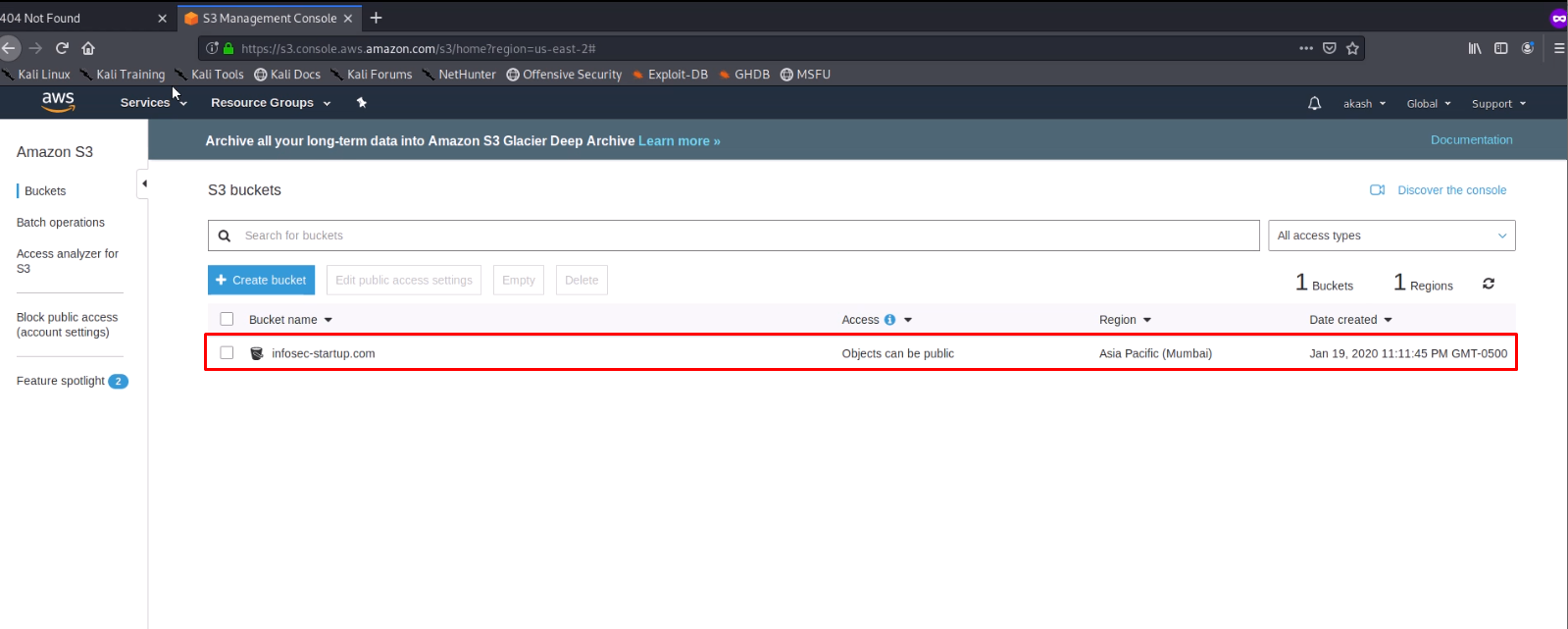
The bucket will be created as shown below.
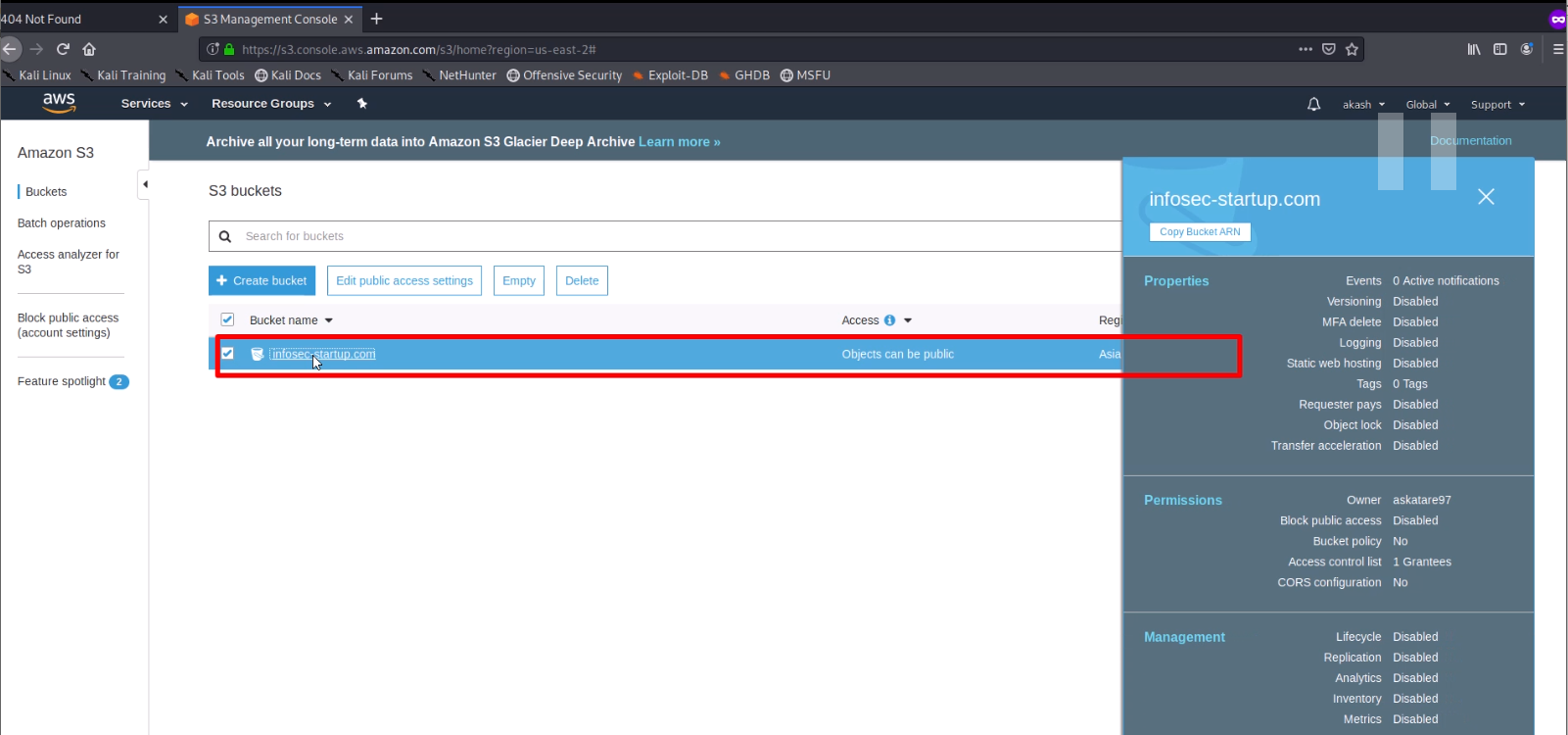
5. Select the bucket name and click on it.
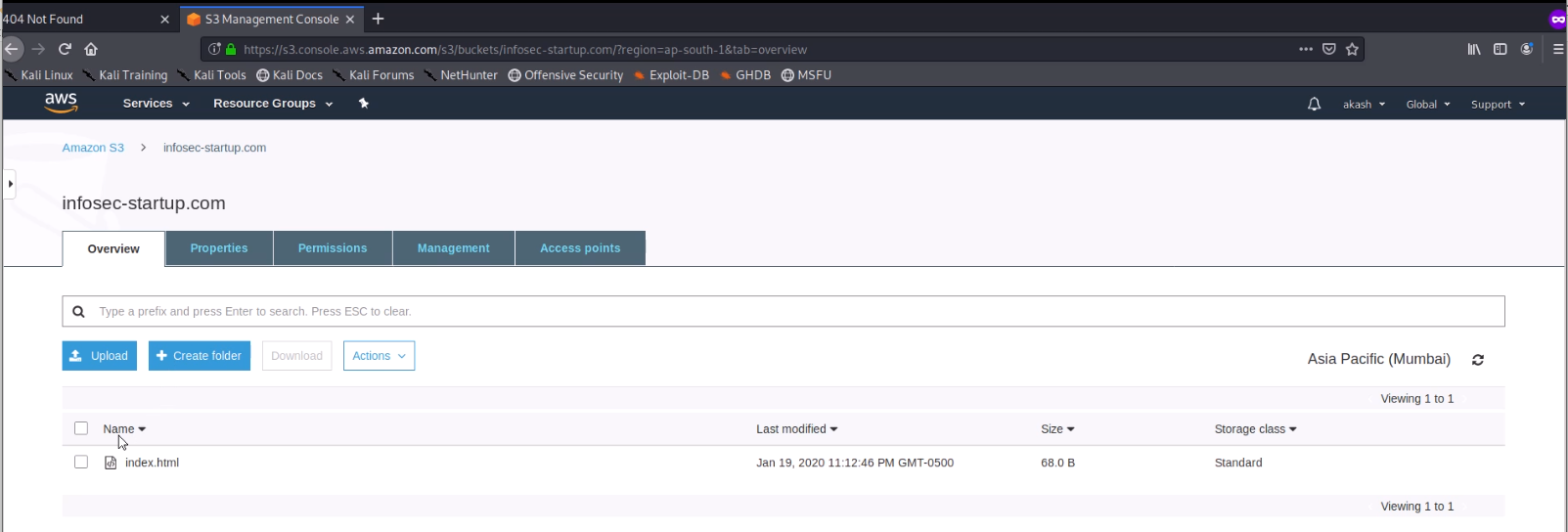
6. Click on upload and add files that you like to upload. Here I have uploaded index.html
7. Select the index.html file and click on Actions and from dropdown click on Make Public.
8. Click on Properties –> Static website hosting –> Use this bucket to host a website and enter the index document name i.e here index.html and finish.
9. Now just visit the domain.
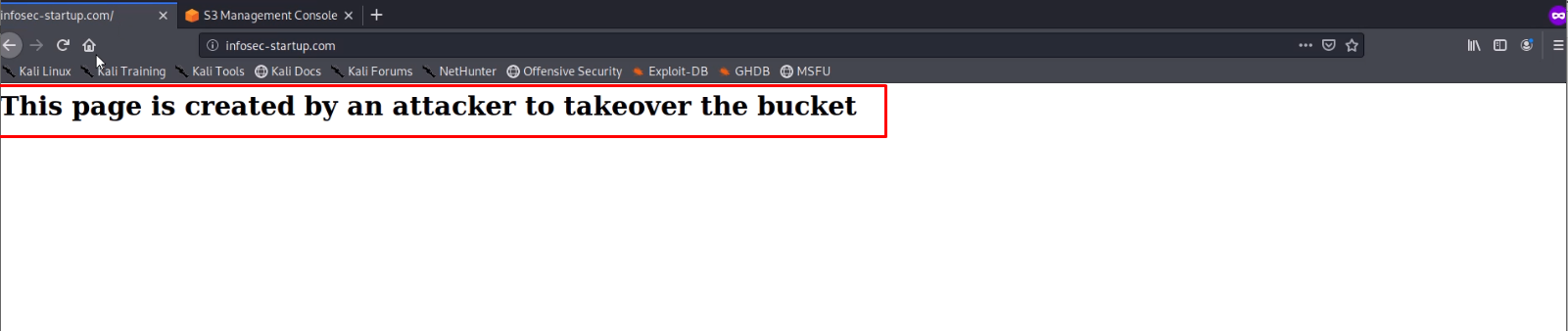
We have successfully taken over the AWS S3 bucket!
Conclusion:
In this blog, we have learned that once we have found an S3 bucket exposed in any of the error pages then how can we claim that bucket name and upload any malicious content to that bucket which is directly going to be displayed on the respective target web application. In the next part, we will be learning more about other vulnerabilities related to AWS and their hands-on exploitations.
If you need support on the AWS Penetration testing, you can get touch with [email protected]