What is Amazon S3?
Amazon Simple Storage Service (Amazon S3) is a public cloud service offered by Amazon web services (AWS). Amazon S3 provides object storage through a simple web service interface. It is widely used to store photos, videos, text files, documents, PDF files and to store backups of large amounts of data as well.
What is Access Control List?
Amazon S3 access control lists (ACLs) empower the user to manage access to buckets and objects. Each and every bucket has an ACL to it as a sub-asset. It characterizes which AWS accounts or groups are granted access and the type of access. Whenever a user had made a request, Amazon S3 checks the corresponding ACL to verify that the requester has the necessary access permissions or not.
A little bit about S3 bucket naming conventions!
- An Amazon S3 bucket name:
- Globally unique
- The namespace is shared by AWS accounts
- Name of the bucket cannot be used by another AWS account in any region until the bucket is deleted
- They are created in a region specified by the user and which is geographically close to the user or place from where data would be accessed.
Accessing a Bucket
Amazon S3 supports two addressing models Virtual-Hosted–Style and Path-Style URLs to access a bucket hosted on AWS Cloud
Virtual Hosted Style Access
In Amazon S3, Virtual Hosted Style URLs follow the format shown below:
https://nameofbucket.s3.Region.amazonaws.com/key name
In this example, infosec-securelayer7.net is the bucket name, ap-south-1 is the Region, and credentials.txt is the key name:
https://infosec-securelayer7.net.s3-website.ap-south-1.amazonaws.com/credentials.txt
Path-Style Access
In Amazon S3, path-style URLs follow the format shown below.
https://s3.Region.amazonaws.com/nameofbucket/keyname
In this example, infosec-securelayer7.com is the bucket name, ap-south-1 is the Region, and credentials.txt is the key name:
https://s3.ap-south-1.amazonaws.com/infosec-securelayer7.net/credentials.txt
There are different ways using which we can find AWS S3 buckets of any target application?
- Tools
- Manual Method
The tool used for AWS Penetration Testing Enumeration
There are different tools available to find the S3 bucket names :
- Bucket Finder
- S3Scanner
https://github.com/sa7mon/S3Scanner
- Lazy
S3
https://github.com/nahamsec/lazys3
- S3
Bucket Finder
https://github.com/gwen001/s3-buckets-finder
- Pacu – (for configuration flaws and many more)
https://github.com/RhinoSecurityLabs/pacu
Identifying Manually:
Using Google Dorks:
site: amazonaws.com inurl: infosec-securelayer7.net
Using Github:
“target application name” amazonaws.com
Using CDN object URL:
- Find CDN object URL
- Append following string to after URL: `
- It will reveal the bucket name in error response
Using the burp suite while uploading:
When you are uploading any images or files in target application capture the request in burp suite and search for a string like
http://infosec-securelayer7.net.s3-website.ap-south-1.amazonaws.com/
In case of virtual hosted style addressing modes anythings before s3 is identified as a bucket name and from the above URL, the infosec-securelayer7.net is a bucket name
In case of path style addressing mode, it is
https://s3.ap-south-1.amazonaws.com/infosec-startup.com/
Using the burp suite while downloading:
When you are downloading any file from the target application we have to captures the request in burp suite and find the name of the bucket or just wait for the prompt in any browser it will show the path from where the file is being downloaded from. This is the endpoint where we find the bucket name.
From the URL’s included in the web page
If there are any images posted on a target web application just right click on it and open it in a new tab and observe the URL if it shows similar to the below URL, we can find the bucket name in the URL.
Spidering using burp suite
If you are using Burpsuite just send the target application for spidering and analyze request which is spidered and also go through HTTP history to find out the bucket name.
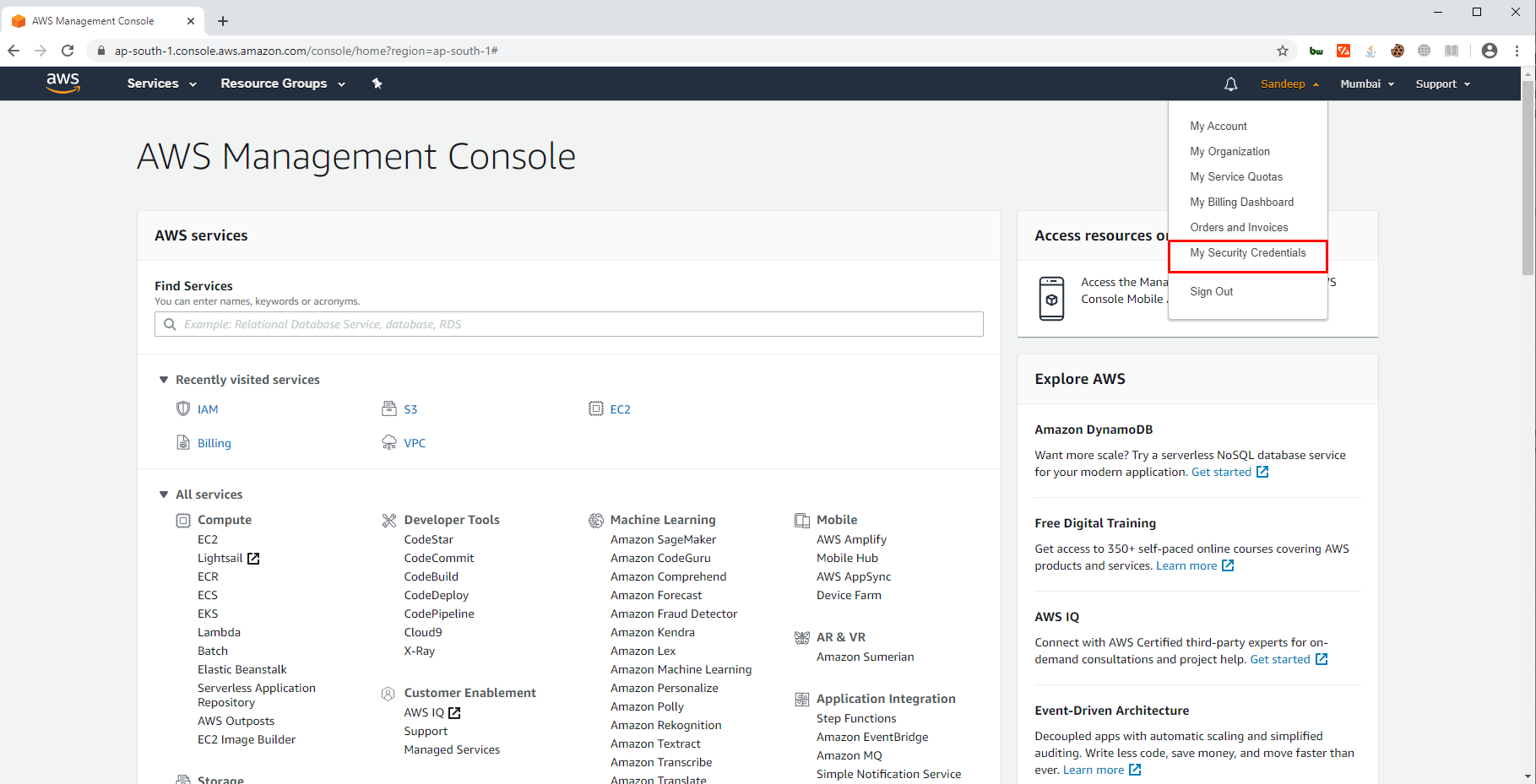
Getting AWS Credentials (Access Key ID and AWS Secret Access Key)
- Sign up for Amazon’s AWS from their official website
https://aws.amazon.com/free/?all-free-tier.sort-by=item.additionalFields.SortRank&all-free-tier.sort-order=asc - Login into your AWS account and click on My Security Credentials.
- Click on Access Keys (access key id and secret access key) to get your login credentials for AWS CLI.
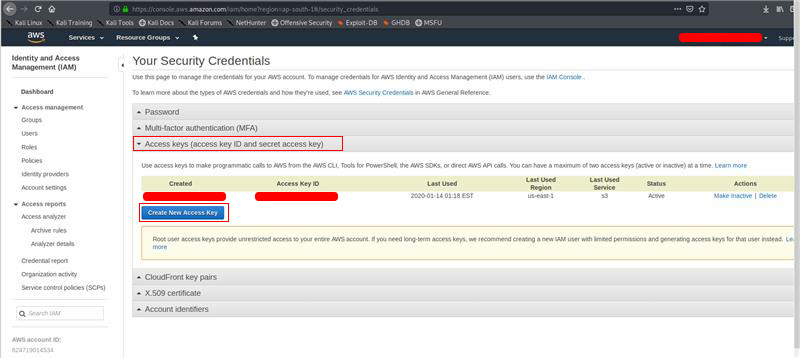
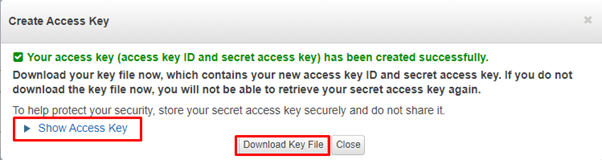
- Then click on Show Access Key option to get your Access Key ID and Secret Access Key or you can download it as well.
What is AWS CLI?
The AWS Command Line Interface (AWS CLI) is an open-source tool that enables you to interact with AWS services using commands in a command-line shell.
Installing AWS CLI on Kali Linux
To install AWS CLI you can simply install using below command
pip3 install awscli
For more commands and guide you can follow the official guide link below:
https://docs.aws.amazon.com/cli/latest/userguide/install-linux.html
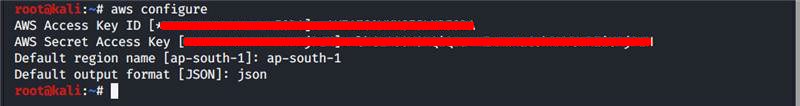
Configuring AWS CLI on Kali Linux
- Start a terminal and enter the below commands then enter the AWS Access Key ID and AWS Secret Access Key that was created in previous steps.
aws configure
Conclusion:
In this blog, we learned in brief about Amazon S3 bucket, why and where it is used, access control list which helps us manage user permission in S3, naming conventions, different addressing modes Virtual-Hosted–Style and Path-Style URLs and a bit about Amazon AWS CLI and its configuration. In the next part, we will be learning about the common vulnerabilities in AWS’s S3 bucket and its exploitations.
If you need support on the AWS Penetration testing, you can get touch with [email protected]



