What is a VPN?
Privacy is the most important aspect of our life. We can never compromise with our security. To keep up with our privacy when we surf online, the VPN was invented.
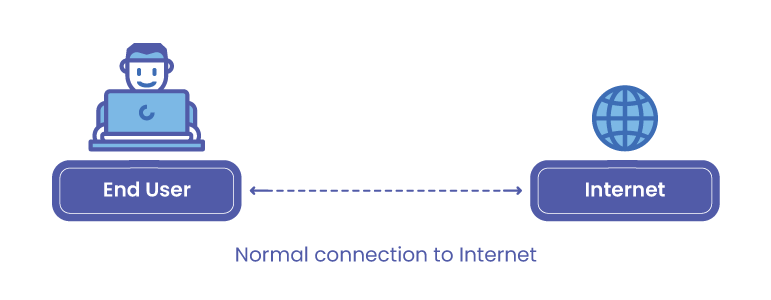
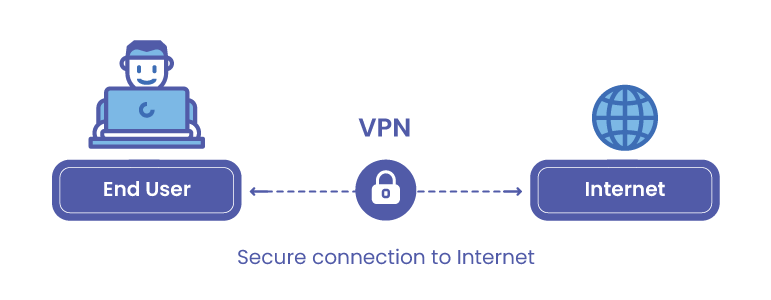
Virtual Private Network, very commonly known as VPN, gives you the liberty of online privacy and anonymity by creating a private network from a public internet connection. VPNs basically mask your internet protocol (IP) address, so that your online actions are virtually untraceable.
The most important feature of VPN services is that they establish secure and encrypted connections to provide greater privacy than even a secured Wi-Fi hotspot. The intensity of the encryption of the VPN tunnel depends on the type of tunneling protocol used to encapsulate and encrypt the data that is going to be exchanged from your device and the internet.
VPN Client
A VPN client can be a standalone purpose-built device or a standard networking software, which is required to connect to the VPN server and successfully create an encrypted tunnel between the two communication endpoints.
Different VPN protocols
| Name | Description | Encryption Strength | Status |
|---|---|---|---|
| L2TP/IP | Layer 2 Tunneling Protocol/Internet Protocol Security | 256-bit session encryption | Strong |
| SSTP | Secure Socket Tunneling Protocol with limited compatibility with windows and some android | SSL 3.0 Encryption. Can disguise VPN traffic as SSL/Https | Medium |
| PPTP | Point – to – Point Tunneling Protocol | supports encryption keys up to 128-bits | Broken |
| SSL/TLS | Secure Sockets Layer/ Transport Layer Security | OpenVPN supports up to 256-bit session encryption and 4096-bit keys | Strong |
| SSH | Secure Shell | Standard | Strong |
Different VPN clients
There are many types of VPN clients available as of now. Some of the commonly known clients are:
- Forti Client
- Pulse Secure
- Cisco AnyConnect
- Juniper Net Connect
- Windows standard VPN
As these are the most commonly used clients, the services they offer are also open to lots of vulnerabilities, which have been exploited and exposed in recent case studies and research.
To know about the vulnerabilities, we will start with 2 Major VPN protocols and their weaknesses, namely:
- IPsec
- SSL
IP security (IPsec)
IP security (IPsec) is an Internet Engineering Task Force (IETF) standard suite of protocols between 2 communication points across the IP network that provide data authentication, integrity, and confidentiality.
It also defines the encrypted, decrypted, and authenticated packets. The protocols needed for secure key exchange and key management are defined in it.
In order to protect the data transfer between two different networks, IPsec operates in two modes i.e.
- Transport mode: The transport mode encrypts the message in the data packet.
- Tunneling mode: The tunneling mode encrypts the entire data packet.
IPsec originally defined two mechanisms for imposing security on IP packets:
- The Encapsulating Security Payload (ESP) protocol, which defines a method for encrypting data in IP packets and
- The Authentication Header (AH) protocol, which defines a method for digitally signing IP packets. The Internet Key Exchange (IKE) protocol is used to manage the cryptographic keys that are used by the hosts for IPsec.
In simpler terms, It means that Internet Protocol Security (IPsec) is a secure network protocol suite, that allows private communication by using the Internet Key Exchange (IKE) protocol to ensure a secure connection.
Do not miss
Common IPsec vulnerabilities
There are security flaws with another internet key exchange protocol called the “IKEv2.” Numerous differences exist between IKEv1 and IKEv2. The latter is the more recent of the two. Despite IKEv1 being considered obsolete, it is still popular and even used on newer devices.
1. Man in the middle attack
IPsec VPN requires keys for identification. In this vulnerability, the weak Pre-Shared Key can be retrieved by an attacker. So in this, the attacker targets IKE’s handshake implementation used for IPsec-based VPN connections. And with the retrieved keys, can decrypt connections.
It will lead to Man-in-the-middle (MitM)attacks. Eventually, this will result in leakage of VPN session data i.e Commonly known vulnerability: Internet Key Exchange protocol “IKEv1”
2. Password cracking
Another vulnerability in IPsec is with password cracking. It is a re-occurring issue with both IKEv1 and IKEv2 versions. The User is required to enter the credentials for getting connected successfully. Once the user enters them, the server first encrypts it and compares it with stored values. If the values get matched, the user gets access.
Using weak passwords in IPsec VPN is what makes it vulnerable to offline dictionary or brute force attacks.
3. Buffer overflow
Buffer is a temporary storage space. While the application or software is in execution, it may not remember the buffer location and overwrites adjacent memory locations. This vulnerability takes place due to a buffer overflow in the affected code area. As a result, it allows the attacker to execute arbitrary code and obtain full control over the system.
SSL VPN?
Secure Sockets Layer (SSL) is IPsec’s default alternative as a VPN protocol. Originated in the 1990s, SSL is the most recent method for implementing VPNs, which is becoming increasingly popular. Later in 2015, this was overtaken by Transport Layer Security (TLS) due to some improvements in SSL versions and encryptions.
This technology provides the VPN capability, using the SSL function that is already built into the modern web browser. The SSL VPN allows users from any Internet-enabled location to establish remote-access VPN connections by using a web browser thus promising productivity enhancements and improved availability.
Common SSL-VPN vulnerabilities
1. Lack of host and endpoints security
The hosts which are to be utilized for creating secure VPN connections, are not properly configured often and also are not tuned.
Major areas of misconfiguration or vulnerabilities in the hosts or endpoint are as mentioned below:
- Encryption
- Anti-Virus Software
- Network security
2. Use of obsolete and insecure SSL implementations
The VPNs which require SSL implementation, for connecting to a server are susceptible because the administrators have to properly configure and update all the SSL versions to appropriate TLS versions.
This removes the major flaws related to cryptographic ciphers and broken algorithms
3. Remote data modification vulnerability
Any form of unauthorized or unauthenticated data alteration is considered a breach of security standards and this is caused by a specific vulnerable scenario. The data altered, may range from passwords, and configuration files, to inserting some malicious codes.
Furthermore, in a whole different scenario, there may be authenticated and unauthenticated data modifications or disclosures.
Recent critical vulnerabilities identified in common VPN products
1. OpenVPN
- LDAP authentication bypass on our Access Server 2.8.0 (CVE-2020-9853)
- The VORACLE attack vulnerability
Mitigations:
All the other relevant mitigations and latest updates being pushed by the team are listed on their portal available at https://openvpn.net/security-advisories/
2. Pulse Connect Secure
- CVE-2019-11510: Pre-auth arbitrary file reading
- CVE-2019-11539: Post-auth command injection Specific Advisory for these vulnerabilities
In CVE-2019-11510, an unauthenticated remote attacker can send a specially crafted URI to perform an arbitrary file reading vulnerability.
More vulnerabilities and other details can be located up here @ https://devco.re/blog/2019/09/02/attacking-ssl-vpn-part-3-the-golden-Pulse-Secure-ssl-vpn-rce-chain-with-Twitter-as-case-study/
Mitigations:
All the other relevant mitigations and latest updates being pushed by the team are listed on their portal available at https://kb.pulsesecure.net/?atype=sa
3. Fortinet FortiOS
- CVE-2018–13379
- CVE-2018–13383
- CVE-2018–13382
CVE-2018-13379 & CVE-2018–13379 The exploits for this vulnerability worked, if the admins or authenticated users downloaded the files required, the usernames and passwords of active users, Path traversal vulnerability in the FortiOS SSL VPN web portal that could potentially allow an unauthenticated attacker to download files through the specially crafted HTTP resource requests.
CVE-2018–13383 Heap buffer overflow vulnerability in the FortiOS SSL VPN web portal could cause the SSL VPN web services to terminate for the logged-in users. It could also potentially allow the remote code execution on FortiOS due to a failure to handle JavaScript href content properly. This would require an authenticated user to visit a specifically-crafted and proxied webpage.
Mitigations:
All the other relevant mitigations and latest updates being pushed by the team are listed on their portal available at https://fortiguard.com/psirt
4. Palo Alto
- CVE-2019-1579
This was a format string vulnerability in the PAN SSL Gateway which handles client/server SSL handshakes. This vulnerability exists because the gateway passes the value of specific parameters in an unsanitized request and makes the exploits work.
An unauthenticated attacker could exploit the vulnerability by sending a specially crafted request to a vulnerable SSL VPN target in order to remotely execute code on the system.
It was originally reported and shared by researchers Orange Tsai and Meh Chang. You can refer to more details on http://blog.orange.tw/2019/07/attacking-ssl-vpn-part-1-preauth-rce-on-palo-alto.html
Mitigations:
All the mitigations and latest updates being pushed by the team are listed on their portal available at https://security.paloaltonetworks.com/
General Mitigations and preventive measures:
- Update the patches released by the vendor
- Configure the servers and gateways
- Disable the default configurations
- Enable MFA in security options
- Monitor and assign the alert to the response team
- Assign the security operations to implement another optional security restriction in case the VPN is compromised
Conclusion
Accessing the internet for multiple purposes is a new way of life and also a necessity. The best we can do is follow the best practices ensured by any regulating organization to help protect our security and privacy.
If you are unaware of the technical details and guidelines, you can follow the details mentioned in our blog or connect with us for any questions. We hope this will help in securing your IT infrastructure.
You can start you secure vpn today with vpnwelt proxy server.



