In the world of cybersecurity, Intrusion Detection Systems (IDS) has long been a cornerstone of defense against threats.
But since technology is evolving to a great extent and so are the techniques to bypass them, it’s critical to assess whether they are enough to safeguard your organization.
In this comprehensive blog, we delve deep into the intricacies of IDS, providing a thorough understanding of their capabilities and limitations. But our main focus is to guide you through a critical comparison between IDS and Manual Penetration Testing.
We believe knowledge is power, and making informed choices about your organization’s cybersecurity strategy is paramount.
By the end of this blog, you’ll be equipped with the insights needed to decide if you should rely solely on IDS or complement them with the adaptive and comprehensive approach of Manual Penetration Testing.
With that being said, without any further ado let us get started.
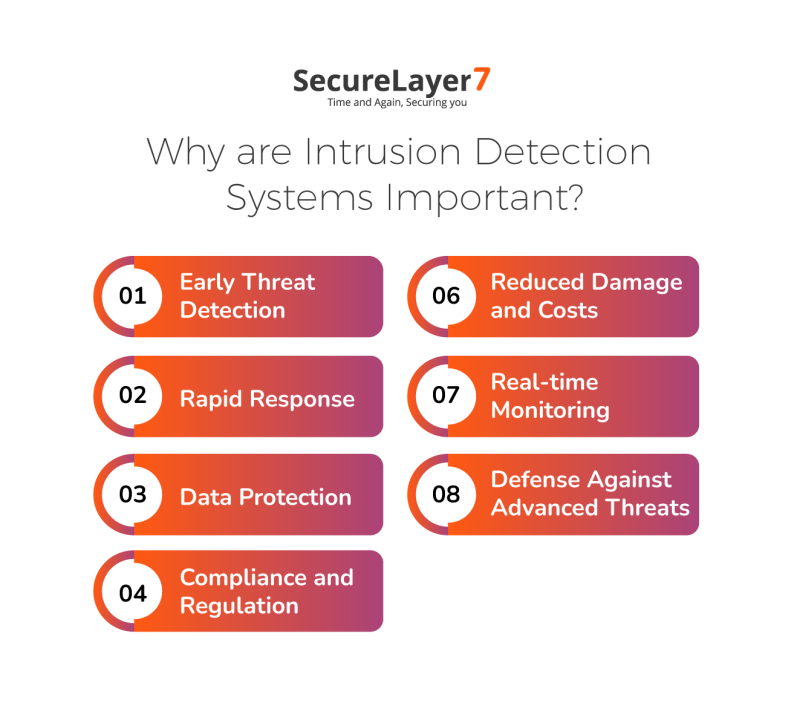
Why are Intrusion Detection Systems Important?
The necessity of protecting sensitive information has fundamental relevance in the context of our digitally intertwined lives, which is emphasized by widespread technological integration.
In this scenario, Intrusion Detection Systems (IDS) assume a crucial function, providing several essential benefits that raise their prominence in the field of cybersecurity.
- Early Threat Detection
- Rapid Response
- Data Protection
- Compliance and Regulation
- Reduced Damage and Costs
- Real-time Monitoring
- Defense Against Advanced Threats
1. Early Threat Detection
IDS has numerous advantages, but its unmatched capacity for proactive threat identification stands out.
IDS serves as an early warning system, skillfully identifying unusual patterns, attempts at illegal access, and other abnormalities that might point to possible cyber dangers.
Security professionals can take proactive action to mitigate emerging risks before they develop into significant breaches thanks to this timely discovery.
2. Rapid Response
The ability of IDS to spark quick action in the face of threats discovered is fundamental to the technology.
As a result of notifications from the system, security officers working out of a Security Operations Center (SOC) launch investigations as part of a rapid reaction process.
This quick reaction not only limits the potential injury but also slows down the assailants’ momentum, impeding their capacity to plan damage.
3. Data Protection
IDS is diligent in identifying unapproved efforts to breach data repositories, upholding the sacred character of data integrity.
IDS prevents data from being compromised or accessed by unauthorized parties by spotting and preventing these efforts, which is a key component of protecting privacy and confidentiality.
4. Compliance and Regulation
IDS develops as a compliance facilitator in industries subject to strict regulatory frameworks. Its duties also include keeping an eye out for and swiftly pointing out any actions that might compromise legal requirements.
IDS assists enterprises in avoiding legal ramifications and assures ethical data practices by aligning with these standards.
5. Reduced Damage and Costs
Facing a cyber event can have far-reaching consequences, impacting both finances and operations. However, the role of Intrusion Detection Systems (IDS) in this scenario is akin to that of a shield against impending damage.
By swiftly detecting and halting threats, IDS operates as a crucial buffer, effectively minimizing the potential for substantial financial losses and disruptions to operational flow.
6. Real-time Monitoring
IDS constantly monitors network activity, acting as a tireless sentry and operating without interruption.
This constant watchfulness guarantees the prompt detection of potential risks even when human oversight may be compromised.
7. Defense Against Advanced Threats
IDS is known for its ability to adapt to a changing threat landscape. It can defend against a variety of online dangers, including sophisticated attacks that may get past traditional security measures.
This adaptability is crucial for fending off the dynamic strategies used by contemporary cyber attackers.
How does IDS work?
The interesting fusion of technology and awareness that drives Intrusion Detection Systems (IDS) efficacy in protecting digital environments becomes clear when one understands the inner workings of IDS.
IDS uses a variety of techniques to spot potential risks and anomalies, operating primarily on the principles of surveillance and pattern recognition.
1. Signature-Based Detection:
Signature-based detection serves as a digital equivalent of recognizing familiar patterns. Here, Intrusion Detection Systems (IDS) play the role of a vigilant observer, comparing ongoing network activities with a collection of well-known attack patterns or signatures.
When IDS spots a match between ongoing actions and a stored signature, it sounds the alarm. This method is highly effective in spotting known threats that have been encountered before.
However, it can struggle when facing new, cleverly disguised, or evolving attacks that deviate from established patterns.
2. Anomaly-Based Detection:
Anomaly-based detection is akin to detecting something unusual or out of the ordinary. In this approach, IDS establishes a baseline of what’s considered normal behavior for the network.
It continuously monitors ongoing activities and measures them against this baseline. When deviations from the expected behavior occur – indicating potential threats – IDS sends out alerts.
This method excels at catching novel and previously unseen attacks that might not fit any predefined patterns. It’s like teaching IDS to recognize not just specific faces but also to raise an alarm if someone’s acting suspiciously in a crowd.
3. Heuristic Analysis:
Think of heuristic analysis as observing behavior to predict intent. Instead of relying solely on predetermined signatures, IDS uses a set of rules that define what’s considered suspicious behavior.
These rules capture patterns that might not be explicitly malicious but could still signify an attack. When network activities align with these rules, IDS triggers an alert.
This method offers versatility, as it can identify both known and unfamiliar threats, making it like an adaptable problem solver that can respond to new challenges.
4. Real-time Monitoring:
Regardless of the specific detection method used, real-time monitoring is a constant thread that runs through IDS’s functionality.
IDS operates like a tireless watchman, constantly overseeing network activities without interruption. It’s ever vigilant, alerting security teams the very moment it detects any behavior that raises suspicion.
This unwavering watchfulness is a cornerstone in ensuring that potential threats are promptly identified and addressed, making IDS a vital component in maintaining the security of digital environments.
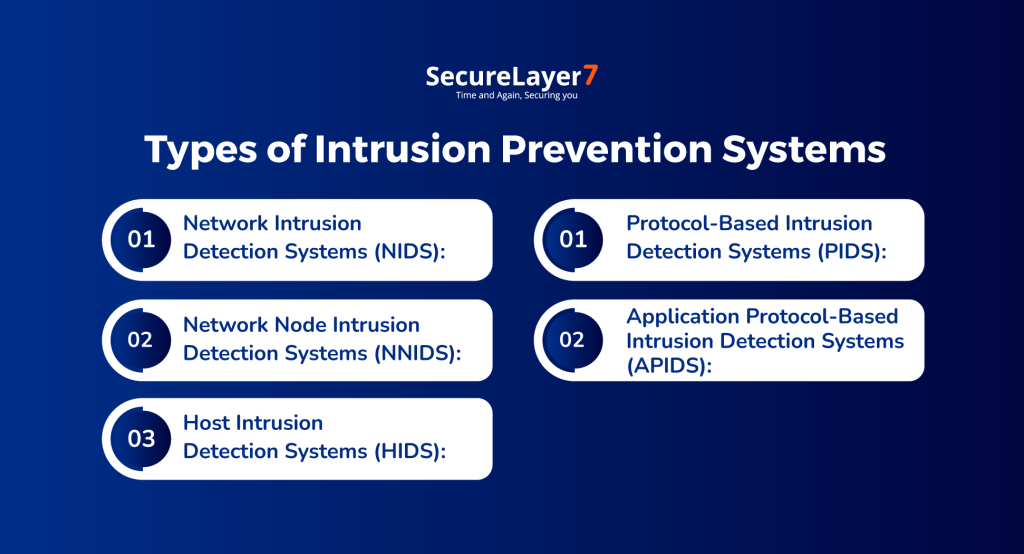
Types of Intrusion Prevention Systems
Although all intrusion detection systems serve the same purpose, they operate in slightly distinct ways.
In total, there are five primary types of IDS, each offering unique approaches to safeguarding digital environments. Let’s delve into the details, benefits, and limitations of each type.
Different types of Intrusion Prevention Systems are
- Network Intrusion Detection Systems (NIDS):
- Network Node Intrusion Detection Systems (NNIDS):
- Host Intrusion Detection Systems (HIDS):
- Protocol-Based Intrusion Detection Systems (PIDS):
- Application Protocol-Based Intrusion Detection Systems (APIDS):
1. Network Intrusion Detection System (NIDS):
A Network Intrusion Detection System (NIDS) functions by monitoring the entire network through one or more points.
Typically installed on dedicated hardware within the network infrastructure, an NIDS inspects each packet of data that traverses it.
NIDS can analyze all traffic, but to prevent information overload, it allows the creation of customizable “rules” to filter specific types of packets.
While NIDS offers real-time event detection and strategic placement possibilities, it may demand hands-on maintenance and need more specificity due to the volume of analyzed traffic.
2. Network Node Intrusion Detection System (NNIDS):
A Network Node Intrusion Detection System (NNIDS) is a variation of NIDS that focuses on individual network nodes.
It analyzes packets passing through each node rather than centralizing monitoring. NNIDS boasts higher speeds and consumes fewer resources, as it spreads the monitoring load across network nodes.
However, NNIDS requires multiple installations, one for each monitored node, which must report to a central dashboard.
3. Host Intrusion Detection System (HIDS):
A Host Intrusion Detection System (HIDS) extends the concept of NNIDS by installing IDS software on each device within the network.
HIDS captures snapshots of a device’s state and compares them to detect changes that could indicate intrusion.
HIDS offers device specificity, effective insider threat detection, and the ability to detect modified system files. However, it might suffer from slower response times and require frequent monitoring.
4. Protocol-Based Intrusion Detection System (PIDS):
A Protocol-Based Intrusion Detection System (PIDS) focuses on monitoring specific protocols, often HTTP or HTTPS.
Positioned at the front end of a server, PIDS safeguards web servers by analyzing inbound and outbound traffic.
While not comprehensive, PIDS can augment a robust cybersecurity strategy by focusing on protocol-based threats.
5. Application Protocol-Based Intrusion Detection System (APIDS):
An Application Protocol-Based Intrusion Detection System (APIDS) specializes in securing software applications.
Typically associated with host-based IDS (HIDS), APIDS monitors communication between applications and servers.
Installed on groups of servers, APIDS complements other IDS types and provides a layer of defense against application-specific threats.
These distinct types of IDS offer a variety of approaches to bolstering cybersecurity measures. By understanding their strengths and limitations, organizations can tailor their intrusion detection strategies to better protect their digital assets.
IDS vs. Firewall vs. IPS
An IDS actively monitors network traffic for unauthorized activities and generates alerts when suspicious behavior is detected. It serves as a watchful guardian that identifies potential threats without actively intervening in the traffic flow.
Whereas a firewall acts as a gatekeeper between networks, controlling the flow of traffic based on predefined rules. It allows or denies traffic based on these rules, providing access control and safeguarding network boundaries.
The IPS on the other hand combines the functionalities of IDS and firewalls, actively monitoring network traffic and taking preventive actions to block threats. It not only detects but also intervenes to halt potential attacks in real-time.
While all three components play critical roles in network security, their functions, approaches, and outcomes vary.
IDS focuses on detection, firewalls prioritize access control, and IPS offers both detection and prevention.
Organizations often deploy a combination of these tools to create a comprehensive security infrastructure that safeguards against a diverse range of threats.
Below is the table to help you visualize the minute working differences between all three.
| Aspect | Intrusion Detection System (IDS) | Firewall | Intrusion Prevention System (IPS) |
| Function | Monitors network for threats | Controls traffic in/outbound | Monitors and blocks threats |
| Focus | Detects unauthorized activities | Filters traffic based on rules | Detects and prevents attacks |
| Action | Generates alerts | Allows or denies traffic | Blocks and takes preventive action |
| Passive/Active | Passive (Alert generation) | Active (Traffic control) | Active (Traffic control & block) |
| Response Time | Reactive (After detection) | Real-time | Real-time |
| Security Level | Detection | Access control | Prevention |
| Intrusion Knowledge | Known and Unknown | Known | Known and Unknown |
| Scalability | Good | Limited | Good |
| Deployment | Network-based or Host-based | Network perimeter | Network-based or Host-based |
| Granularity | High (Detailed analysis) | Medium (Based on rules) | High (Detailed analysis) |
| Use Cases | Identifying security breaches | Access control and filtering | Real-time threat prevention |
Limitations of IDS and Firewalls vs. Manual Penetration Testing
We’ll carefully examine these restrictions in this part, illuminating the limitations that businesses face when relying primarily on automated systems.
However, we won’t leave you hanging with just a list of constraints. Instead, we’ll introduce an alternative, more dynamic approach: Manual Penetration Testing.
By comparing the capabilities and drawbacks of IDS and Firewalls to Manual Penetration Testing, you’ll gain a deeper understanding of the evolving cybersecurity landscape and be better equipped to make informed decisions about your organization’s security strategy.
| Limitations of IDS and Firewalls | Description | Addressed in Manual Penetration Testing |
| Inability to Detect Unknown Threats | IDS and Firewalls rely on known threat signatures and predefined rules, making them less effective against novel or zero-day attacks. | Manual penetration testing can identify novel or zero-day vulnerabilities by simulating real-world attack scenarios. |
| False Sense of Security | Relying solely on IDS and Firewalls may create a false sense of security, as sophisticated attackers can bypass these defenses. | Manual penetration testing provides a more realistic assessment of an organization’s security posture, uncovering vulnerabilities that could be exploited. |
| Lack of Context | IDS and Firewalls often operate in isolation, lacking context about an organization’s specific environment, which can hinder accurate differentiation between benign and malicious activities. | Manual penetration testers understand the organization’s environment, allowing them to provide insights tailored to its specific context. |
| No Prevention of Insider Threats | These systems are primarily designed to protect against external threats, providing limited protection against insider threats that require a more nuanced approach to detection. | Manual penetration testing can simulate insider threats and assess an organization’s readiness to detect and respond effectively. |
| Encrypted Traffic Challenges | IDS and Firewalls may struggle to inspect encrypted traffic effectively as encryption becomes more common, limiting their visibility into potentially malicious activities. | Manual penetration testers can evaluate an organization’s security posture, including how it handles encrypted traffic and potential vulnerabilities. |
| Complex Management | Maintaining and fine-tuning IDS and Firewall rules can be complex and resource-intensive, especially for organizations lacking in cybersecurity expertise. | Manual penetration testing provides expert assessment without the need for organizations to manage complex rule sets. |
In light of these limitations, organizations are increasingly turning to manual penetration testing as a more comprehensive and adaptable approach to cybersecurity.
Where the threat landscape constantly evolves, manual penetration testing stands out as a proactive and adaptive approach that aligns with organizations’ growing security needs.
Its ability to address the nuances of an organization’s environment and provide actionable insights makes it an invaluable asset in the pursuit of robust cybersecurity.
How can SecureLayer7 help?
At SecureLayer7, we’re not just another cybersecurity company; we’re your trusted partners in safeguarding your digital fortress.
Our team comprises some of the most skilled and seasoned ethical hackers in the field. They don’t rely on automated scripts; they leverage their deep knowledge, experience, and creativity to simulate real-world attacks.
Our manual penetration testers go beyond the surface to identify vulnerabilities that automated systems often miss. They provide you with contextual insights, understand your unique security posture, and deliver actionable recommendations to fortify your defenses.
Trust in our elite team, trust in SecureLayer7. Your security is our priority. Get the consultation now.

![Top 7 Penetration Testing Companies In USA — [Updated 2024]](https://blog.securelayer7.net/wp-content/uploads/2023/11/Top-7-Penetration-Testing-Companies-in-the-USA-1-1.png)