What are cyber security metrics?
Cyber security metrics are the number of systems with known vulnerabilities.
Knowing the number of vulnerable assets in your environment is a key cyber security metric to determine the risk your business incurs. Managing updates and patches is a complex process, but very important to avoid loopholes that can be exploited in your environment.
10 Cybersecurity Metrics You Should Be Monitoring :
Effectively managing variable performance ratios in information security can mean the difference between a practical and efficient project and a complete waste of money.
Although managers have been tracking KPIs for quite some time, in information security, this is a rare and still developing practice for tracking cybersecurity metrics.
So, here are some suggestions for cyber security metrics that can and should be tracked to ensure the efficiency of your security projects.
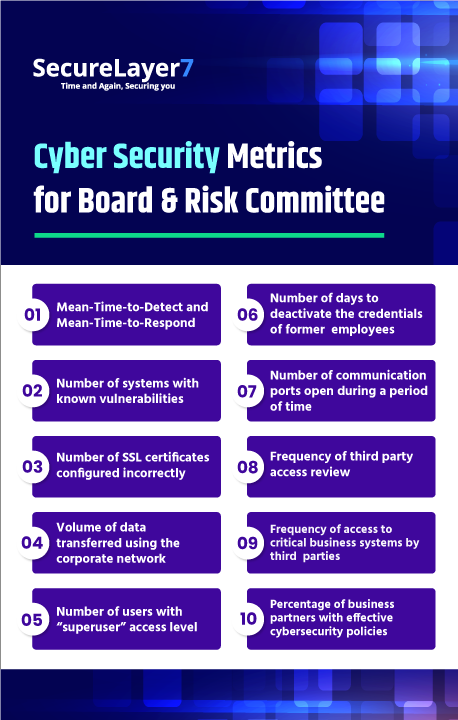
1. Mean-Time-to-Detect and Mean-Time-to-Respond:
The mean time to identify (MTTI) and mean time to contain (MTTC) for US companies indicate that the detection and response phases are suffering. In fact, the MTTC in 2017 was 208 days and the MTTI 52 days. At the same time, the probability of incurring an average default cost of $ 2.25 million is almost 28% over the next 24 months for US companies.
Poor performance on MTTI and MTTC is a large contributor to default costs. These should be your two most important KPIs when measuring information security. It is also a good KPI for CISOs to measure and display their Board for long-term improvement. Everyone on the security team should prioritize improving these two KPIs.
2. Number of systems with known vulnerabilities:
Knowing the number of vulnerable assets in your environment is a key cybersecurity metric to determining the risk that your business incurs. Managing updates and patches is a complex process, but very important to avoid loopholes that can be exploited in your environment. A vulnerability scan that includes all the assets will indicate what needs to be done to improve the security posture of your company. A vulnerability management program is not a nicety, but a necessity.
3. Number of SSL certificates configured incorrectly:
An SSL certificate is a small file that certifies the ownership of a cryptographic key to the website or company with which data is being exchanged, guaranteeing the authenticity of the transaction. Monitoring the security requirements for each certificate, as well as ensuring that they are properly configured on servers, prevents them from falling into the wrong hands and that your company’s digital identity is not used to steal user information.
4. Volume of data transferred using the corporate network:
If your employees have unrestricted access to the internet through the corporate network, monitoring the volume of traffic allows you to identify misuse of company resources. When downloading software, videos, movies, and applications a user can leave the door open for botnets and malware to invade their environments, even more, if the downloads are from websites known to be dangerous.
5. Number of users with “superuser” access level:
Best practices in information security management include full control of the level of user access to company resources; an employee only needs to access the data, systems, and assets that are necessary for her job. Identifying the access levels of all users on the network allows you to adjust them as needed by blocking any superuser or administrator that doesn’t make sense.
6. Number of days to deactivate the credentials of former employees:
By monitoring these cyber security metrics, you can define whether HR and IT teams are working in step. In an ideal scenario, the access of users terminated from the company should be terminated immediately. Keeping them active is a tremendous risk, as it leaks sensitive information and can lead to compromised devices.
7. Number of communication ports open during a period of time:
As a general rule, avoid allowing incoming traffic for NetBIOS (UDP 137 and 138, TCP 135-139 and 445). Be careful with outgoing SSL (TCP 443) – a session that stays active for a long time could be an SSL VPN tunnel that allows two-way traffic. All common ports for protocols that allow remote sessions, such as TCP 22 (SSH), TCP 23 (telnet), TCP 3389 (RDP), and TCP 20 and 21 (FTP), should be monitored for a period of time.
8. Frequency of third party access review:
IT managers often grant access to third parties on their networks to complete a project or activity. It is important to monitor whether access is cancelled at the end of service provisioning. Failure to do so endangers your environment if the third party decides to come back and extract data or carry out other malicious activity; for example, they may be employees of a competitor. Possibly worse, if a third party’s network is breached, you could expose your network to the same threat.
9. Frequency of access to critical business systems by third parties:
Mapping critical business systems and knowing the users who access them is imperative in the context of security. Monitoring attempts to access servers or applications that should not be the target of unauthorized users can indicate misconduct and intentions to compromise your environment.
10. Percentage of business partners with effective cybersecurity policies:
You must maintain strict control and monitor the cybersecurity metrics of the companies that provide services for your business. Giving this outsourced company access to your environments can be a huge risk if you don’t have effective policies in place for their security in the first place. It’s no exaggeration to say that if your business invests in security but has third parties connected to your systems that don’t, you have no security at all.