Most security tools can identify potential flaws, but they lack the contextual intelligence to determine if those vulnerabilities actually pose a real-world risk.
All this is set to change with the launch of Sandyaa, an open-source autonomous source code auditor, by SecureLayer7. This is designed to analyze a complete codebase and validate real vulnerabilities. Furthermore, it uses LLMs to understand code context, trace execution paths, and craft exploits — without any setup or an API key.
What is Sandyaa?
Sandyaa, powered by LLMs such as Claude, is an autonomous security bug hunter. Simply point it to a local directory or a Git repository, and it handles the entire code analysis.
The system builds a contextual understanding across the codebase, identifies vulnerabilities, and generates exploit code for each finding. It compiles findings into structured reports, mapping issues directly to specific files and lines of code.
Platforms
It offers platform support for the following:
- macOS: Fully supported and actively tested.
- Linux: Expected to work, though not yet actively tested.If you notice any blockers, report them.
- Windows (native): Native Windows is not supported. It uses Unix-only commands and invokes the Claude CLI directly, which fails on Windows. It can run on WSL2 using a Linux environment. Native Windows support requires changes or a community PR.
Vulnerability Coverage
Sandyaa can find the following categories of bugs:
- Memory safety: Use-After-Free, buffer overflow, type confusion, and double-free
- Logic bugs: Auth bypass, TOCTOU, and state machine errors
- Injection: SQL, command, XSS, SSRF, and path traversal
- Crypto misuse: Weak algorithms, ECB, hardcoded keys, and bad randomness
- Concurrency: Races, atomicity violations
- Integer issues: Overflow, underflow, truncation, and signedness
- Unsafe APIs: Deserialization, XXE, and prototype pollution
How It Works
Sandyaa follows a structured approach as given below:
- Accepts input: Direct it to a local directory or provide a GitHub repository link for Sandyaa to scan the assigned codebase.
- Builds context: Reads across files to understand how different code parts interact.
- Breaks code: Splits large codebases into smaller chunks for efficient processing.
- Runs recursive analysis: Instead of scanning once, it revisits the code multiple times using LLMs to refine findings and identify deeper issues.
- Traces execution flows: Follows call chains and data movement through the application to identify vulnerabilities in logic and data handling.
- Filters real risks: Checks whether a vulnerability can actually be triggered in a real-world scenario.
- Generates PoCs: For each validated vulnerability, Sandyaa creates working proof-of-concept code.
- Produces structured reports: Organizes findings with clear references to file paths and line numbers, making it easier to locate and fix issues.
Key Features of Sandyaa
The core capabilities of Sandyaa includes the following.
- No setup required: Runs on your existing Claude Code login with no ANTHROPIC_API_KEY or additional configuration needed.
- RLM-based pipeline: Uses Recursive Language Models with a Python REPL, sub-LLM queries, and programmatic aggregation.
- Multiple recursive passes: Performs recursive passes including call-chain tracing, data-flow expansion, self-verification, vulnerability chaining, PoC refinement, contradiction detection, assumption validation, and exploitability proof.
- Attacker-aware filtering: Eliminates findings from untrusted inputs.
- Evidence chain (evidence.json): Links each finding to the exact file and line number.
- Dynamic chunk sizing: Adjusts code chunk sizes based on code density and token limits.
- Checkpointing support: Resumes interrupted scans without restarting.
- Optional Gemini support: Supports Gemini via CLI routing without requiring an API key.
- Terminal dashboard: Provides a real-time view of analysis progress and findings.
- Generates POC: Generates proof-of-concept code and can optionally execute it.
What Makes It Different
It has two key differentiators:
- First, Sandyaa operates seamlessly via your existing Claude Code authentication, eliminating the need for an ANTHROPIC_API_KEY, complex setup, or additional billing layers.
- Second, it leverages a Recursive Language Model (RLM) approach to handle large and complex codebases.
Getting Started
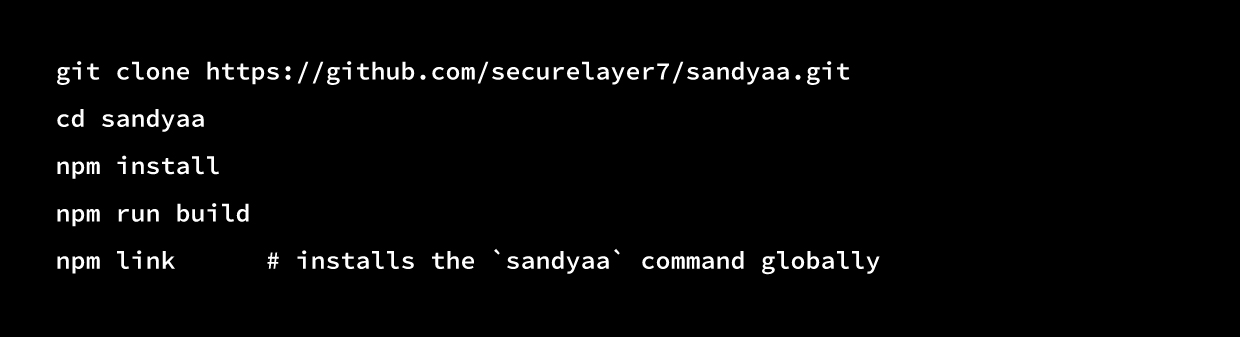
To get started, access the Sandyaa GitHub repository. Below are the steps to begin the process.
A. Install
Requirements:
- macOS (actively tested), Linux (expected to work), or Windows via WSL2
(Native Windows is not supported due to Unix-only commands and Claude CLI dependencies) - Node.js 18 or newer
- Claude Code installed and logged in
- git (used to clone remote repositories; auto-installed on macOS/Linux if missing)
Gemini (Optional)
You can optionally run some parts of the analysis on Gemini instead of Claude:
- If the gemini CLI is available in your PATH and authenticated, Sandyaa will use it, no API key required as it reuses the CLI login.
- If you use the REST API, export GEMINI_API_KEY before running Sandyaa.It’s used to resolve the latest Gemini model tiers at startup. Otherwise, static defaults apply. If neither is available, Sandyaa performs the entire analysis on Claude.
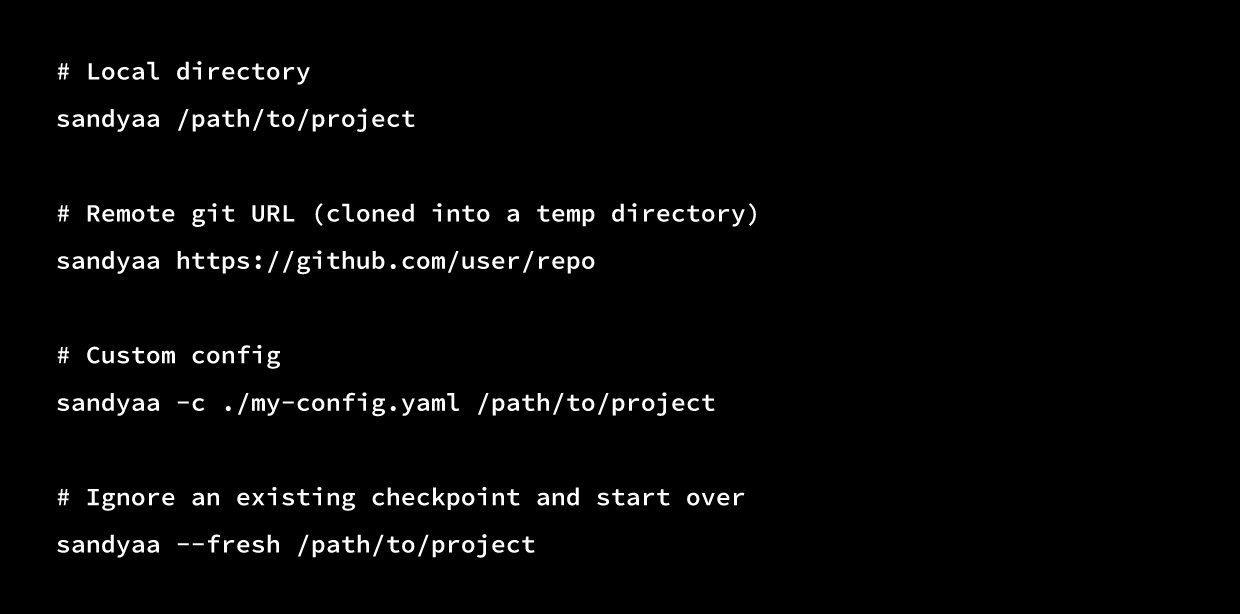
B. Usage
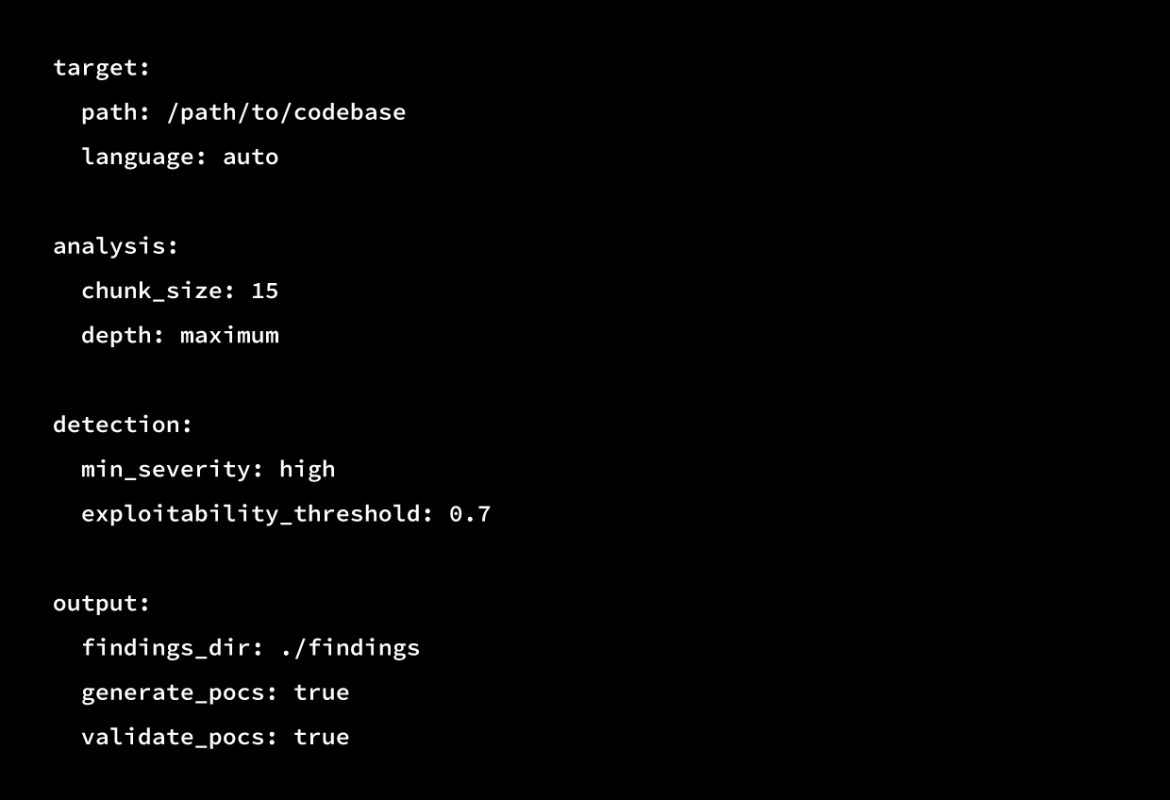
C. Configuration
It now reads .sandyaa/config.yaml from the existing directory. An example is shown below:
D. Output Format
Sandyaa organizes findings into a structured directory for easy navigation and traceability.
- It stores findings in the findings/ directory.
- It organizes each bug into its own folder (e.g., bug-001-sql-injection/, bug-002-xss/).
Each folder contains the following sequentially:
- analysis.md
- poc.py
- SETUP.md
- evidence.json
It provides a summary with evidence.json links that map each claim back to specific file paths and line numbers.
Conclusion
On a final note, Sandyaa shifts code security from merely listing issues to proving them. This makes findings easier to prioritize and act on, allowing teams to focus on vulnerabilities that are actually exploitable.
As codebases grow and software release cycles move faster, Sandyaa can be a gamechanger. While still in the early phase of development, it clearly shows how the code security is heading from detection to validation.
How to Contribute
If Sandyaa helped you identify a bug that was assigned a CVE, we’d like to hear about it. You can open a PR to add an entry in CVES.md along with the following details:
- CVE ID
- Affected project and version
- One-line description
- Link to the public advisory or writeup
- Clearly mention which Sandyaa phase surfaced it (context building, detection, recursive pass, etc.).
Include only the CVEs that are already publicly disclosed. Avoid submitting embargoed findings.
For valid findings, add them to the case-studies/ folder in the github repository, while including the target repo, commit hash, analysis.md, and evidence.json.



