Nessus Explorer is a powerful security and vulnerability scanning tool developed by Tenable Network Security that helps organizations identify vulnerabilities and potential security threats in their network infrastructure.
With cyber threats constantly evolving and becoming more sophisticated, it’s critical to conduct regular vulnerability assessments to ensure the security of your network.
In this blog, we will provide a step-by-step guide on how to run a Nessus scan, as well as best practices for conducting comprehensive security scans with Nessus Explorer.
We will cover important aspects such as scan configuration, result interpretation, and remediation of identified vulnerabilities.
By the end of this blog, you will have a better understanding of how to use Nessus Explorer to identify and address potential security issues before they can be exploited by attackers.
What is Nessus Explorer?
Nessus Explorer is a comprehensive vulnerability scanner that can perform various security checks on network systems, devices, and applications. It is specifically designed to detect and report security issues such as misconfigurations, weak passwords, missing security patches, and malware infections.
The tool also offers guidance on how to address identified vulnerabilities, which helps organizations maintain a secure and compliant IT infrastructure.
Nessus Explorer is widely used by IT teams and security professionals to conduct vulnerability assessments, compliance audits, and penetration testing due to its accuracy, reliability, and ease of use.
For any organization that wants to ensure its network infrastructure is secure, Nessus Explorer is an essential tool.
Key Features of Nessus Explorer
Some of Nessus Explorer’s key features include the following.
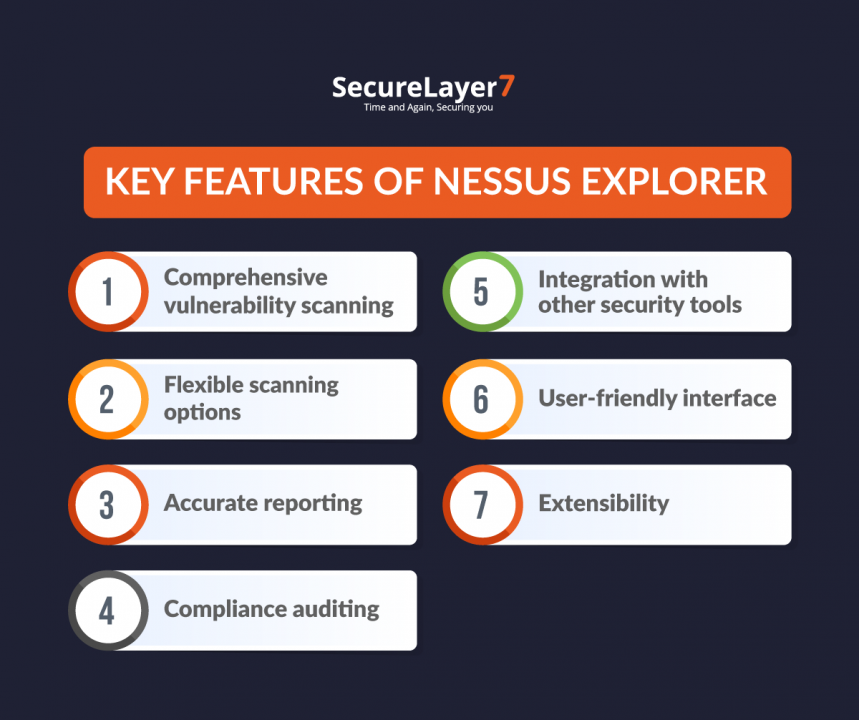
1. Comprehensive vulnerability scanning
Nessus Explorer can perform both credentialed and non-credentialed scans of a network, web applications, and databases to identify vulnerabilities and potential security threats.
2. Flexible scanning options
It allows you to customize the scanning process by configuring scan policies, setting scan targets, selecting specific ports and protocols, and defining exclusions.
3. Accurate reporting
Nessus Explorer provides detailed reports that prioritize vulnerabilities based on severity, with clear remediation guidance to help you address any issues that are discovered.
4. Compliance auditing
The tool also includes pre-built compliance templates for various regulatory frameworks, such as PCI DSS, HIPAA, and CIS, enabling organizations to assess their compliance posture and ensure they meet relevant security standards.
5. Integration with other security tools
Nessus Explorer can be integrated with other security tools, such as Security Information and Event Management (SIEM) systems and ticketing systems, to provide a more complete view of an organization’s security posture.
6. User-friendly interface
The tool features an easy-to-use interface that enables users to quickly configure and launch scans, view results, and generate reports.
7. Extensibility
Nessus Explorer supports a wide range of plugins and extensions, allowing users to extend its functionality and customize the tool to their specific needs.
Penetration Testing and Vulnerability Assessment with Nessus
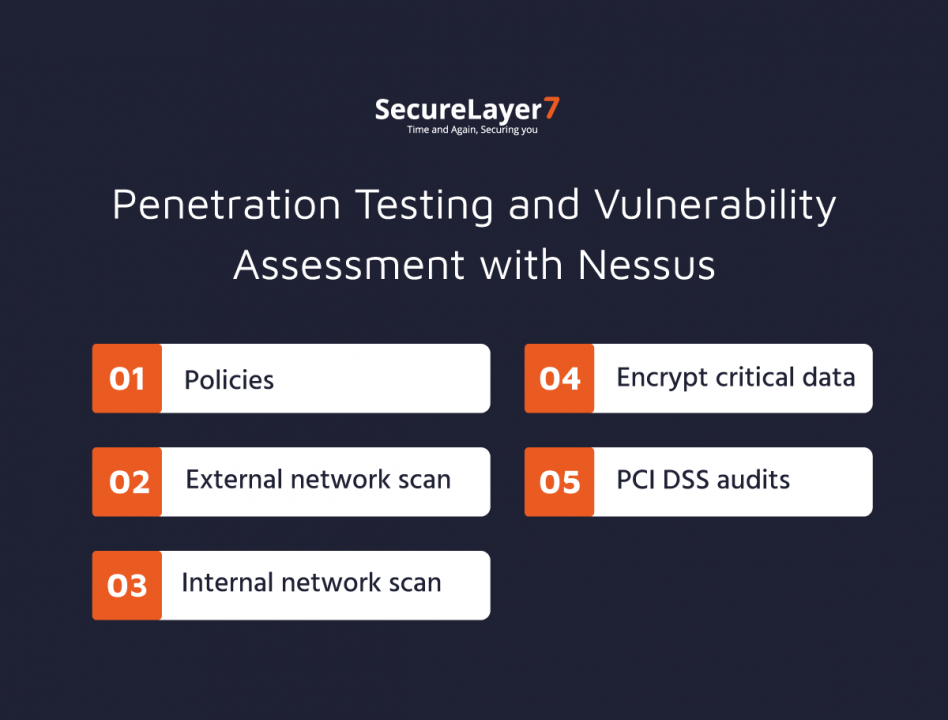
Nessus is a comprehensive vulnerability scanning tool that can be used for both penetration testing and vulnerability assessments. Here’s how you can use Nessus for different types of security assessments:
1. Policies
Nessus allows you to create custom policies for vulnerability scans, which include selecting the scanning options, targets, credentials, and other parameters. You can define policies based on your organization’s security needs and regulatory compliance requirements.
2. External network scan
To perform an external network scan with Nessus, you need to specify the target IP addresses or domain names, select the appropriate policy, and configure the scan options.
Nessus can scan for vulnerabilities in web servers, databases, network devices, and other systems exposed to the internet. You can use the results to prioritize and remediate any security issues identified.
3. Internal network scan
For an internal network scan, Nessus can scan for vulnerabilities in systems within your organization’s private network. You can perform a credentialed scan to obtain more comprehensive results.
Nessus can detect vulnerabilities in operating systems, applications, and other devices on the network. You can use the results to identify security weaknesses and apply appropriate remediation measures.
4. Web app tests
Nessus can perform web application tests to identify vulnerabilities in web-based applications. You can use the Nessus web application scanner plugin to scan web applications for common vulnerabilities such as SQL injection, cross-site scripting, and command injection. You can use the results to improve the security of your web applications and protect against potential attacks.
5. PCI DSS audits
Nessus has pre-built compliance templates for various regulatory frameworks, including the Payment Card Industry Data Security Standard (PCI DSS). You can use Nessus to perform PCI DSS audits to identify vulnerabilities and compliance gaps in your organization’s network, systems, and applications.
Nessus can generate reports that show compliance status and remediation recommendations, helping you to achieve and maintain PCI DSS compliance.
However, it is important to acknowledge that Nessus is not a replacement for a comprehensive penetration test.
Limitations of Nessus Explorer
The Nessus vulnerability scanner and management platform does have some limitations, which include:
1. False positives
Like any automated tool, Nessus may generate false positives, which are alerts that indicate a vulnerability that is not actually present in the system being tested. This can lead to wasted time and effort in investigating and mitigating non-existent vulnerabilities.
2. Limited scope
Nessus is primarily designed to scan for vulnerabilities in the IT infrastructure, networks, and web applications, but it may not be effective in detecting vulnerabilities in other areas, such as social engineering or physical security.
3. Network limitations
Nessus requires access to the network being scanned and may not be effective in scanning systems that are not accessible or hidden behind firewalls or other security measures.
4. Time-consuming
Scanning with Nessus can be time-consuming, especially for large and complex IT environments. It can also consume significant network bandwidth and system resources.
5. Lack of context
Nessus may not always provide the context necessary to determine the severity or impact of a vulnerability. It’s important to have human expertise and analysis to understand the implications of the vulnerability and prioritize remediation efforts.
While Nessus is a powerful vulnerability scanning tool, it is important to acknowledge its limitations and the need for a comprehensive penetration test.
Get Comprehensive Coverage of Your Attack Surface with In-Depth Pentests
A comprehensive penetration test involves a simulated attack on an organization’s entire attack surface, including its networks, systems, and applications. This type of testing provides a more complete understanding of an organization’s security posture and can identify vulnerabilities that may not be detected by vulnerability scanners alone.
That’s where SecureLayer7 comes in. As a leading provider of comprehensive penetration testing services, SecureLayer7 can help organizations get a true understanding of their attack surface and close out every vulnerability.
SecureLayer7’s comprehensive penetration testing services include
- Network Penetration Testing: We can perform a simulated attack on an organization’s network infrastructure to identify vulnerabilities and provide recommendations for remediation.
- Web Application Penetration Testing: SecureLayer7 can test an organization’s web applications for vulnerabilities such as SQL injection, cross-site scripting, and authentication bypass.
- Mobile Application Penetration Testing: We test organization’s mobile applications for vulnerabilities such as insecure data storage, insufficient authentication, and insecure communication.
- Wireless Penetration Testing: We also work on checking for wireless networks for vulnerabilities such as weak encryption, rogue access points, and unauthorized access.
- Social Engineering Testing: We can simulate social engineering attacks such as phishing, vishing, and pretexting to test an organization’s employees’ awareness and response to these types of attacks.
Contact us today to schedule a comprehensive penetration test with SecureLayer7 and get a true understanding of your attack surface, identify vulnerabilities that may not be detected by scanners, and close out every vulnerability.
Don’t wait until it’s too late – take action now to secure your organization’s digital assets.



