Active Directory (Pen Test ) is most commonly used in the Enterprise Infrastructure to manage 1000’s of computers in the organization with a single point of control as “Domain Controller”. Performing Penetration Testing of Active Directory is more interesting and are mainly targeted by many APT Groups with a lot of different techniques. We will focus on the basics of Active Directory to understand its components before the attack.
Understanding the Active Directory and its Components
Directory Service:
A Directory Service is a hierarchical structure which map the names of all resources in the network to its network address. It allows store, organize and manage all the network resources and define a naming structure. It makes easier to manage all the devices from a single system
Active Directory:
Active Directory is a Microsoft Implementation of Directory services. It follows x.500 specification and it works on the application layer of the OSI model. It allows administrators to control all the users and resources in the network from a single server. It stores information about all the users and resources in the network in a single database Directory Service Database. Active Directory at its uses “Kerberos” for Authentication of the users and LDAP for retrieving the directory information.
Domain Controller (DC)
A Domain Controller is a Windows Server running Active Directory Directory Services in a domain. All the users, user’s information, computers and its policies are controlled by a Domain Controller. Every User must authenticate with the “Domain Controller” to access any resource or service in a domain. It defines the policies for all the users what actions needs can be performed and what level of privileges to be granted etc. It makes the life of administrators easy to manage the users and the computers in the network.
Naming Conventions in AD:
An Object can be any network resource in the Active Directory Domain. These objects can be Computers, Users, printers etc.
A Domain is a logical grouping of objects in the organization. It defines the security boundary and allows objects within the boundary to share the data among each other. It stores information about all the objects within the domain in the domain controller.
A Tree is a collection of one or more domains. All domains within a single tree share a common schema and Global Catalogue which is a Central Repository of information about all the objects.
A forest is a collection of one or more trees which share a common Directory Schema, Global Catalogue and Configurations across the organization
Kerberos Authentication:
Kerberos is an authentication protocol which is used for Single Sign-on (SSO) purposes. The concept of SSO is to authenticate once and use the token to access any service for which you are authorized to.
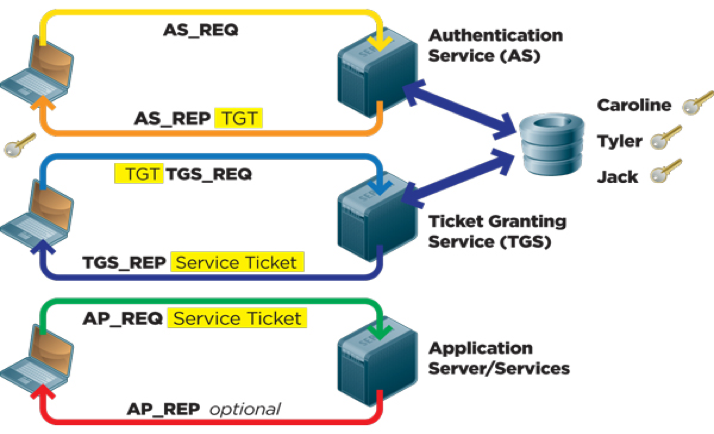
Kerberos Authentication Process follows:
Step1: The User sends an “Authentication Service Request (AS_REQ)” to “Key Distribution Centre”(KDC) for “Ticket Granting Ticket (TGT)” with the “User Principle Name (UPN)” and current Timestamp which is encrypted with User password.
Step2: KDC decrypts the request (AS_REQ) with the local copy of the User’s password stored in the database and checks the UPN and Timestamp. After verification, it will respond with a reply (AS_REP). It has two levels of encryption one has TGT which is encrypted with KDC’s password and second is Session Key along with expiry Timestamp is encrypted with hash of the user’s password.
Step3: Now the User’s machine will cache the TGT and Session Key. This TGT is used when requesting for a service. The session key is being used for further communication with KDC which does not require credentials. All the resources in the domain are available as a service and require service ticket for the same.
Step4: Now User’s Machine send a request(TGS_REQ) to KDC for Ticket Granting Service(TGS) along with TGT, Service Principle Name(SPN) which contains the name of the service and its IP Address and port number and Timestamp which is encrypted with session key received in Step2.
Step5: KDC will decrypt the request with User’s Session Key and checks the SPN, Timestamp and TGT which is encrypted with the KDC password. If all the details are valid, it will send a reply (TGS_REP) with the TGS encrypted with the password hash of the service provider, Ticket Expiry Timestamp encrypted with AS_REP Session key.
Step6: User’s machine will decrypt the request with the session key and extract the TGS ticket. User’s Machine will forward this ticket to the Application as a (AP_REQ), the application decrypts the request with its password and extract the session key and other attributes about the client regarding privileges and groups. It verifies these details and grants the access to the application.
This is the total process of the Kerberos authentication implemented in the Active Directory.
Attacks on Kerberos:
Silver Tickets are the Ticket Granting Service (TGS) which is obtained from the KDC can be forged and is effectively cracked offline to compromise the service machine
Golden Tickets are the Ticket Granting Ticket (TGT) which is obtained from the KDC on the AS_REP. It can be forged and cracked offline to compromise the KDC
Roasting AS-REP can be performed when the server disables DONT_REQ_PREAUTH, an attacker can request the KDC on behalf of the machine and crack the password offline
LDAP is a Lightweights Directory Access Protocol which acts as a communication protocol that defines the methods for accessing the directory services in a domain. It defines the way that data should be presented to the users, it includes various components such as Attributes, Entries, and Directory Information Tree.
Reconnaissance:
- SPN Scanning instead of Port Scanning of all the machines
Active Directory can be enumerated in multiple ways as follows:
- Active Directory can be enumerated even without a Domain Account
- Active Directory can be enumerated to gather all the Domain and Forests Information, Forest and Domain Trusts many more things without Admin Rights
- Active Directory can be enumerated to retrieve Privileges accounts, Access Rights of all groups using PowerView
Attacks on AD
- PassTheHash: It is a technique used to pass the NTLM hash of a service to the remote server to login rather than plain text password
- PassTheCache: Passing the cached credentials of Linux/Unix-based systems which are part of the domain to a windows-based machines to gain access to the system
- Over-Pass-The-Hash: Obtained NTLM hash can be passed to KDC to grab a valid Kerberos ticket and pass it to another system to gain access
Maintaining Access in the Domain:
- DCSync: Requires Domain Admin or Enterprise Admin permission and pull all the password data to sync with another malicious and stay in the domain
- DCShadow: Allows register a new domain to add new objects into targeted infrastructure
There are many more attacks can be performed to compromise the objects in the Enterprise Active Directory infrastructure. I have listed most commonly performed attacks. I have covered the basics of Active Directory and its necessary conventions which are necessary to learn before going for pen testing. In the next article, i will explain these attacks in details with practical scenarios.
Image Ref: https://redmondmag.com/articles/2012/02/01/~/media/ECG/redmondmag/Images/2012/02/0212red_Kerberos_Fig1.ashx



