Objection in Action
Once all things go right, we can inject Frida scripts into our target application. Open target application and enter following command in powershell
objection -g YOUR-APPLICATION-NAME explore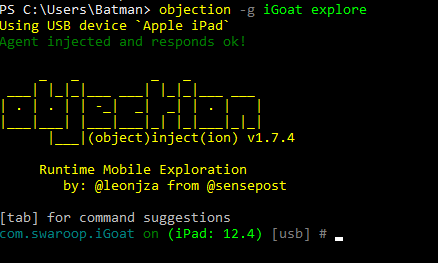
You will now have access to application’s file over device’s shell
Test Cases:
> Application exploration:
1. To browse applications file
ls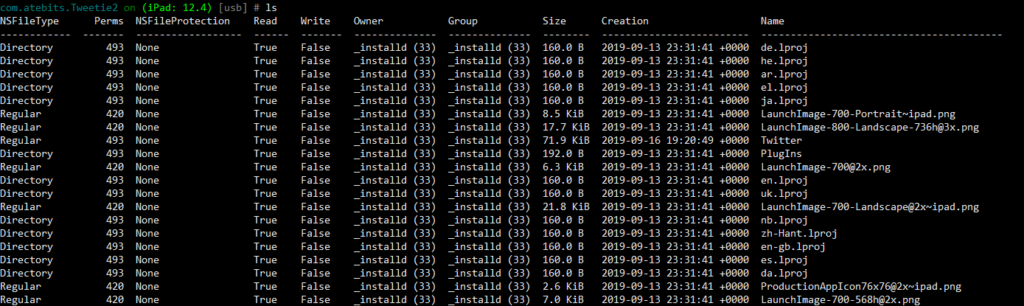
2. Print current directory
pwd print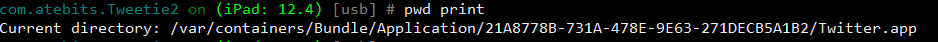
3. To browse applications file
cd /folder/path/name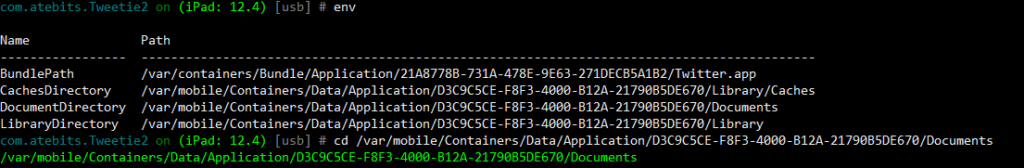
> Sensitive Data Exposure
1. Dump .plist files:
Property List file is a structured binary formatted file which contains the essential configuration of a bundle executable in nested key value pairs. Plist files are used to store the user preferences and the configuration information of an application.
i. Print environment information
env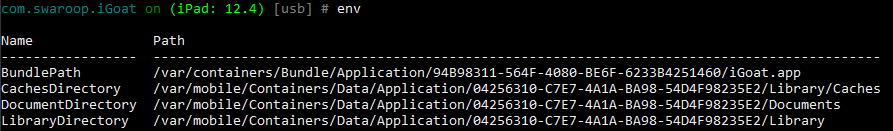
ii. Goto document folder
cd /var/mobile/Containers/Data/Application/04256310-C7E7-4A1A-BA98-54D4F98235E2/Documents
ls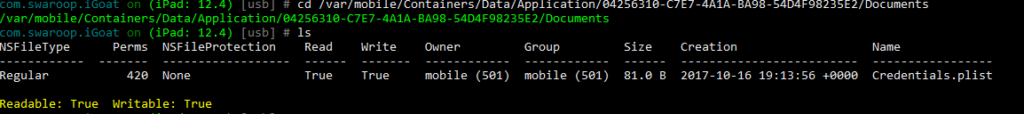
iii. Download .plist file
file download Credentials.plist creds.plist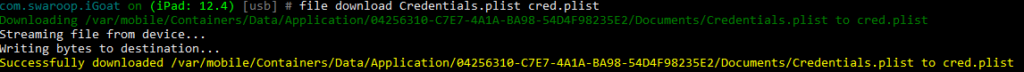
It will get stored in your “C:\Users\USERNAME” path as “creds.plist” name.
iv. To read that downloaded file:
!type creds.plist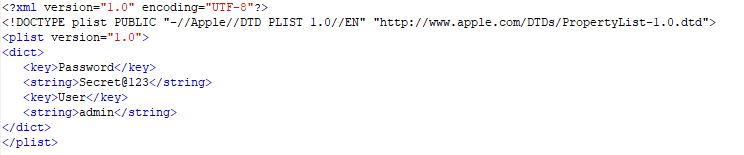
2. Dump keychain file of target application:
Keychain is an encrypted container (128 bit AES algorithm) and a centralized SQLite database that holds identities & passwords for multiple applications and network services, with restricted access rights.
ios keychain dump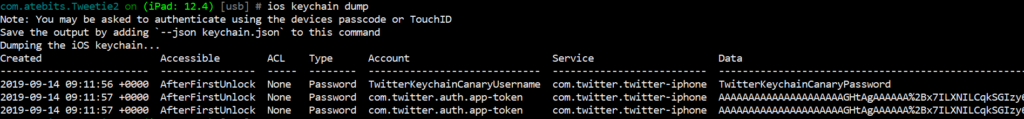
3. Dump sqlite files:
The SQLite database that comes with iOS does not have a built-in support for encryption. Most of the iOS applications store lots of sensitive data in plain text format in SQLite files.
i. Print environment information
env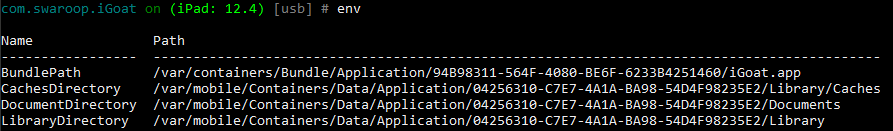
ii. Goto document folder
cd /var/mobile/Containers/Data/Application/04256310-C7E7-4A1A-BA98-54D4F98235E2/Documents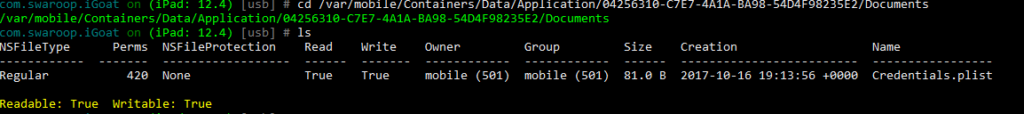
iii. Download .sqlite file
sqlite connect /var/mobile/Containers/Data/Application/04256310-C7E7-4A1A-BA98-54D4F98235E2/Documents/Credentials.sqlite file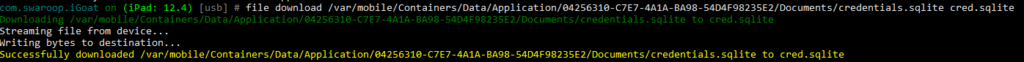
4. Memory dump:
i. We will download and save memory dump into json file:
memory list modules --json memory.json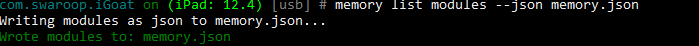
ii. It will list memory modules and store in “memory.json”
iii. To read memory.json
!type memory.json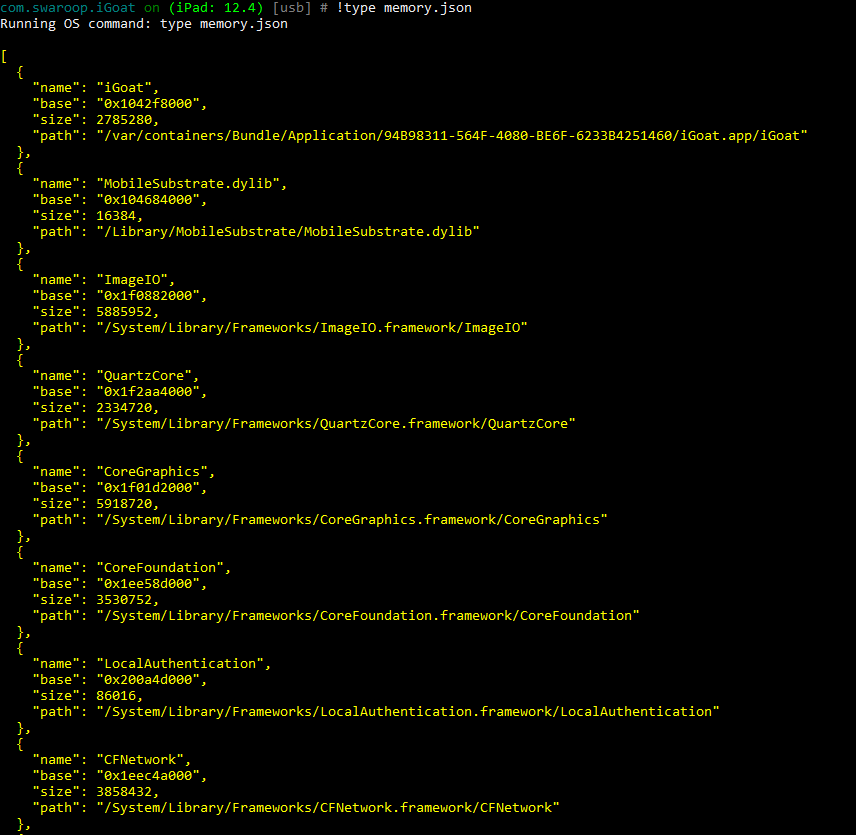
> SSL pinning disable/bypass:
One of the cool feature of objection is one command ssl pinning bypass. To disable ssl pinning checks for target application run following command:
ios-sslpinning-disable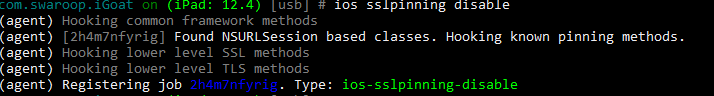
This will start ssl pinning disable task and will run without interruption. You can kill this process or job with following commands
> Dump cookies stored by target application:
Some of iOS application’s stores user’s session cookies into local storage. This cookies may contain server secrets, oauth tokens, api keys, etc.
ios cookies get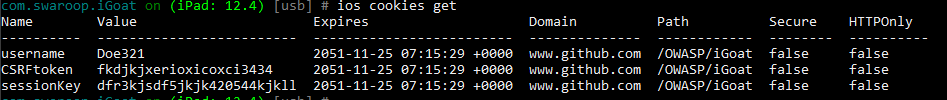
> Job listing and kill:
You can list and enable/kill any running job according to test scenarios.
i. To list out all running jobs:
jobs list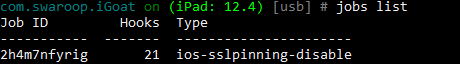
ii. Note job id to be killed
iii. Run following command to kill job
jobs kill JOBID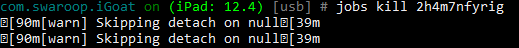
That’s all for today folks. Happy Hacking!!
References:
https://github.com/sensepost/objection
https://leonjza.github.io/blog/2017/07/11/objection—runtime-mobile-exploration/



