Businesses often use penetration testing and red teaming interchangeably, assuming one can replace the other. This is a mistaken notion that may lead to misaligned security investment. Therefore, distinguishing between these two exercises is critical for resource allocation.
Penetration testing and red teaming operations serve two distinct goals:
- A red team assessment is more like adversarial simulation designed to test how your people, processes, and technology respond to a real-world multi-stage attack.
- Penetration testing primarily focuses on identifying and cataloging security flaws within a specified scope.
In this blog, we’ll discuss in detail about the key differences in penetration testing and red teaming.
What is Red Reaming?
A red team acts like real-world hackers to see if your Security Operations Center (SOC), or blue team can actually spot and manage the threat before it’s too late. It tests your overall security resilience.
Red teaming evaluates how your organization reacts when breach happens in the real world scenario. Red teamers think and act like Advanced Persistent Threats (APTs) that stay hidden for long and map out your system environment.
This is typically employed by organisations with more mature or sophisticated security postures.
A red team assessment begins with thorough reconnaissance. Using Open Source Intelligence (OSINT), red teamers map out your IT infrastructure and daily operations to identify the path of least resistance.
This allows them to launch attack with precision, including:
- Custom payloads: Crafting malicious files designed to bypass your specific filters.
- Physical tools: Using RFID cloners or hardware trojans to breach onsite security.
- Social engineering: Creating fake personas or companies to exploit human trust.
Red teamers don’t just look for security gaps; they try to find out how far they can get before your team catches them.
What is Penetration Testing?
Penetration testing (PT) is a pre-defined manual security exercise where cybersecurity experts systematically attempt to find a hidden vulnerability within a system.
Pentesting methodology involves a structured five-step process starting from reconnaissance, planning and attack, exploitation, movement and report generation.
Pentesters are typically aware of the potential engagement, what they are going to test, and how far they can go.
A penetration testing exercise is more time efficient, focusing on finding as many vulnerabilities as they can. This approach pinpoints the specific areas where the problems are and which of them you need to prioritize first based on their severity score.
Red Teaming And Pentesting: Key Differences
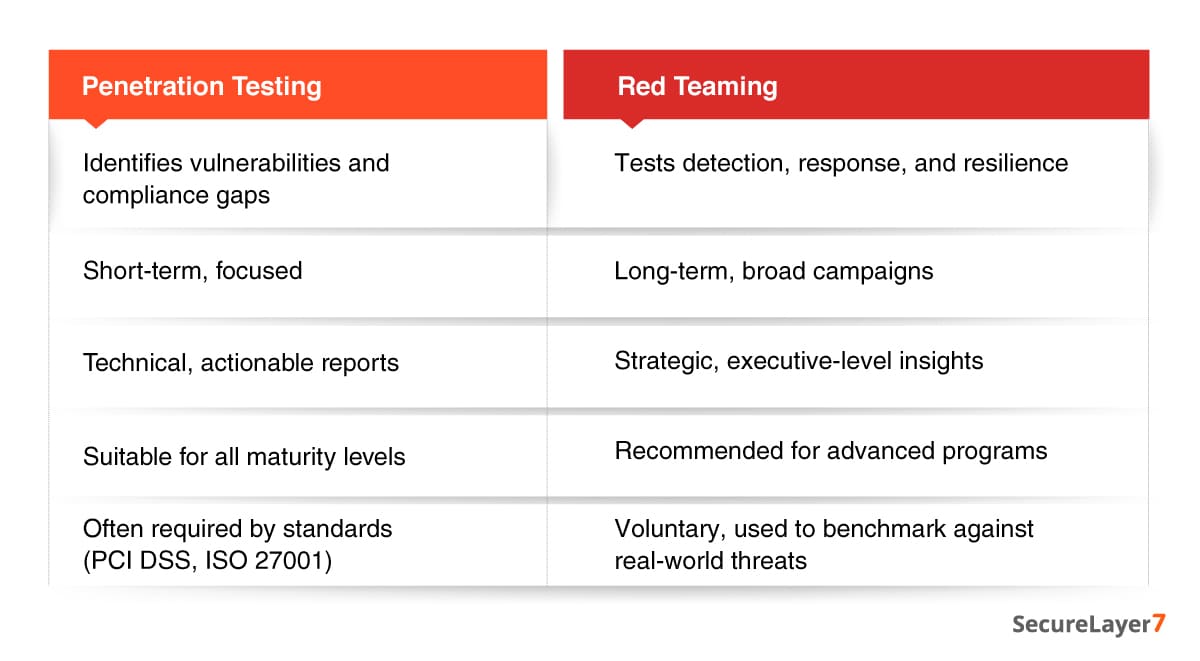
Penetration testing and red teaming differ vastly in the purpose, scope, methodology, and duration.
A. Purpose
Penetration testing focuses on identifying security gaps in predefined systems or applications. Pentesters probe, report, and recommend fixes for identified vulnerabilities. Organizations primarily conduct penetration testing for security auditing and meeting compliance requirements.
In contrast, red teamers test how well an organization detects and responds to an active, stealthy adversary.
B. Scope
Penetration testing typically targets a single web application or a defined segment of an IT network, with clear boundaries, objectives, and timelines. For example, a web application test may focus solely on identifying OWASP Top 10 security risks.
Red teaming has a broader focus. Its targets may include people (through phishing or pretexting), processes (such as incident response drills), and technology (servers, cloud platforms, physical access).
Red teamers may act with the same flexibility as real attackers, unless restricted by the rules of engagement.
For example, a pentester may pinpoint a vulnerability, such as a server with an open port and compromised API authentication mechanism.
In contrast, a red team exercise simulates a full-spectrum attack — leveraging social engineering to harvest credentials, establishing a network foothold, and executing a silent data exfiltration of sensitive assets. It goes beyond security auditing.
C. Tactics
Penetration testers leverage a combination of automated scanning tools and manual exploration methodologies to identify vulnerabilities.
Conversely, red teaming relies on creativity and stealth to execute complex missions. Their methodology extends beyond digital exploits to include social engineering, custom malware development, zero-day exploitation, and even physical breach attempts.
D. Duration
Penetration tests are targeted, time-bound assessments typically spanning several days to a few weeks.
However, a red team engagement duration can be longer, lasting up to weeks or even months.
E. Outcomes
The penetration testing process culminates with a detailed report outlining a list of vulnerabilities, their severity, and final recommendations to act on.
Red teaming, conversely, delivers a high-level analysis of systemic security postures—identifying critical gaps in monitoring, delays in incident response, and lapses in security culture.
The value proposition of pentesting is limited to fixing vulnerabilities, while red teaming is geared towards building cyber resilience.
F. Audience
The audience of penetration testing reports and red teaming differs. Pentesting reports are for IT administrators and security engineers who actually fix the issues.
Red team reports are geared towards executives, SOC leaders, and decision makers as they highlight strategic risk posture and provide a high-level view of the organization’s readiness.
Real-World Use Cases
Let’s understand the difference between red team assessments and penetration testing with an example.
An ecommerce platform wants to assess the security of a newly launched payment gateway. Penetration testers identified SQL injection vulnerabilities and authentication weaknesses, helping the company remediate issues and support its PCI DSS compliance efforts.
In contrast, a financial firm conducts a red team exercise. The red team simulates a real-world attack by launching a phishing campaign, compromising credentials, moving laterally, and attempting data exfiltration, while testing the organization’s detection and response capabilities.
The difference is evidently clear:
- Penetration testing focuses on identifying specific technical vulnerabilities within a defined scope
- Red teaming evaluates how well an organization can detect and respond to a realistic, multi-layered attack across people, processes, and technology.
When to Use Each Approach
Now the question arises :when are they used? Here is the quick decision matrix:
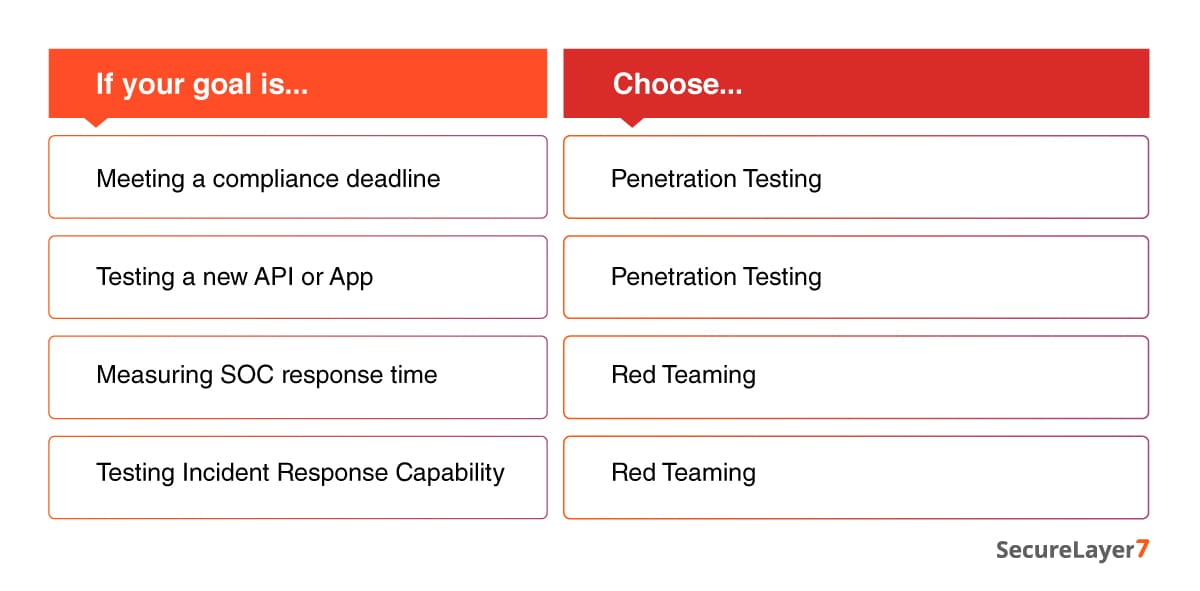
An effective approach involves integrating penetration testing and red teaming. This allows organizations to identify gaps and fix vulnerabilities quickly using pentesting, and stress-test resilience with red team assessment.
Furthermore, to maximize ROI, the findings from your red team operation can be used to refine your next penetration testing. For example, if a red team bypasses your perimeter through a specific misconfiguration, your next penetration testing should encompass this weakness across the enterprise.
Integrating both approaches eliminates the guesswork and helps you move from a reactive “patch-and-pray” model to a proactive “threat-informed defense”.
Closing Thoughts
Cybersecurity is not a static process. It requires constant improvement and fine-tuning. Organizations need to understand that cybersecurity isn’t a race to the finish, it’s a progression.
Attempting a red team exercise before penetration testing will not serve the purpose. If you keep finding common security vulnerabilities, there is no point to go for red teaming.
Don’t wait for a breach to expose your gaps. Contact us now if you are looking to strengthen your defenses before attackers do.
Frequently Asked Questions (FAQs)
No. Most regulatory frameworks (PCI DSS, HIPAA, SOC2) explicitly mandate a Penetration Test to document an exhaustive list of vulnerabilities. Red Teaming is more goal-oriented and stealthy to provide the broad technical audit that regulators require.
Only if your perimeter is already hardened. If your annual pentests are still finding “Critical” or “High” severity vulnerabilities, you are not ready. Red Teaming is a stress test for your detection and response (the people), not a discovery tool for basic unpatched software.
A pentest report is more tactical in nature, while a red team report is a strategic narrative for executives. One fixes the code; the other fixes the culture.