A report by Markets and Markets projected that the penetration testing sector will nearly double in size, from $1.4 billion in 2022 to $2.7 billion by 2027. This underscores the importance of web application security assessments to pinpoint and remediate vulnerabilities proactively. penetration testing.
As the defacto face of your company, these applications are typically data-driven client-server software that helps businesses establish a dominant online presence, provide stellar customer service, and achieve a competitive edge over their market rivals. Web apps accomplish this by leveraging the information they collect through the large volume of user interactions with the application.
This is why regularly assessing their cybersecurity posture should be a business’s utmost priority to protect sensitive information such as their users’ personal, medical, and credit card information. But how does penetration testing come into the picture, and what does web application penetration testing have to do with it? Well, keep reading to gain an in-depth understanding of how cybersecurity plays an important role in uplifting businesses globally.
The primary objective of this article is to equip you with valuable insights into the various aspects of web application penetration testing, including methodology and best practices for carrying it out effectively within your organization.
What is Web Application Pentesting
Web application penetration testing is a vital element of web app security, which aids in identifying potential threats or vulnerabilities to assess system security. This simulates hack-style attacks to determine whether unauthorized access to sensitive data is possible on the web app attack surface.
Penetration tests or pen tests are a widely used security assessment technique where a cyber security professional performs a self-inflicted simulated attack on an application’s internal and external networks to weed out underlying flaws, threats, and vulnerabilities.
The objective of web application penetration testing is to uncover and address security risks to improve the application’s overall security posture so that no malicious actor could take undue advantage of the security lapse. This ensures the safety and security of crucial data while also building trust in your brand among customers. In addition, it helps organizations meet security standards like PCI-DSS, HIPAA, GDPR, etc.
Regular penetration testing is also helpful in fixing misconfigurations, bugs, and flaws present early in their web application development cycle before a public launch. These assessments are essential to proactively combat emerging attack vectors and threats that the increasingly sophisticated cybercriminal’s may employ to target your business.
Web Application Penetration Testing Methodology
The web application penetration testing methodology uses a structured approach to identify vulnerabilities in the web app security environment:
1. Information Gathering:
This phase involves collecting information about the target, such as web application URLs, descriptions of application logic, and other critical functions.
2. Business and Application Logic Mapping:
Now, pentesters manually evaluate applications to map business functions, workflows, and access controls within the application.
3. Automated Web Crawling:
Pentesters run automated crawls to identify pages accessible to unauthenticated users and the entire site tree.
4. Authenticated Vulnerability Scanning:
In this stage, penetration testers verify results manually for web application crawling and run manual tests for enhanced security coverage.
5. Manual Web Vulnerability Tests:
Pentesters conduct manual tests to identify vulnerabilities in application-level functionality, business logic, and deployment, such as injection attacks, session management flaws, and access control issues.
6. Reporting:
This is the final phase, where comprehensive findings are presented as reports to help stakeholders enhance their short-term and long-term security strategies.
Web App Pentesting: Common Web App Test Cases
Web application penetration testing helps identify and address various security vulnerabilities that could be exploited by attackers. Some of the key security flaws that web app pentesting counters include:
1. Injection Flaws:
Injection vulnerabilities like SQL injection enable malicious actors to inject malicious code into the web app environment, resulting in session hijacking, keystroke logging, or unauthorized actions.
2. Input Validation Issues:
Insufficient input validation allows unauthorized data to enter the system workflow, causing malfunctions.
3. Misconfigurations:
Misconfigurations in firewall systems, applications, or network components leave security loopholes that bad actors can exploit.
4. Insecure Direct Object References (IDOR):
IDOR vulnerabilities allow threat actors to access or manipulate data objects directly without requiring access controls.
5. Cross-Site Scripting (XSS):
XSS attacks involve injecting malicious scripts into web pages.
6. Password Cracking:
This is a commonly used technique where a cybercriminal illegally obtains sensitive passwords using an application, an algorithm, or several other methods to steal sensitive data, including company resources, credentials, and credit card information
Best Practices to Follow in Web App Penetration Testing
Below are some key best practices that organizations must follow while conducting web app pentesting:>
- Define Scope and Budget: Clearly define the goals and scope of the web app penetration test, including a list of systems, networks, and assets that need to be tested. Take note of the budget, as it may be a limiting factor in the scope.
- Understand Laws and Obtain Necessary Permissions: Obtain all necessary consents and authorizations before conducting target attacks. Also, ensure compliance with applicable laws and regulations before, during, and after the test.
- Prepare an Appropriate Production Environment: Conduct penetration tests in the production environment. Set appropriate limits for pen testers to avoid slowdowns and prevent DoS attacks.
- Set Testing Boundaries Clearly: Define in advance who will conduct testing, the timing of the test, permissible attack targets, and how the report will be structured.
- Follow Proper Incident Response Protocols: Adhere to proper incident response protocols once significant vulnerabilities are uncovered to address and patch them.
- Prepare the Post-Reporting Procedure: Document all penetration testing findings, including vulnerabilities and remediation recommendations. The purpose of the document should be to assist decision-makers in short- and long-term strategic planning.
- Communicate Timely and Clearly: Establish an open communication channel that allows stakeholders to track progress, ask questions, clear doubts, and share information, as trust is paramount in any communication.
Types of Web App Pentesting
There are two ways in which a tester conducts penetration tests. They are:
- Internal Penetration Testing
- External Penetration Testing
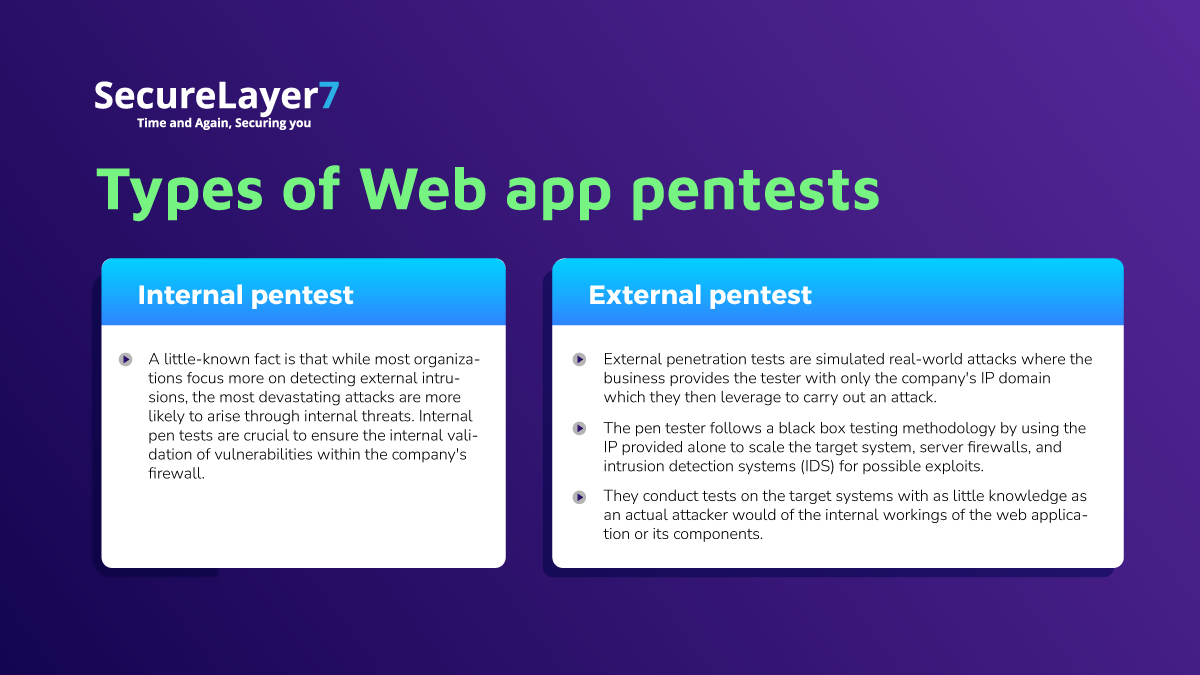
Internal Penetration Testing
Internal penetration testing is a type of pentesting that assesses the security posture of web applications on the company’s intranet. This aims to uncover vulnerabilities within the firewall that an intruder could exploit from within.
Advantages of Internal Pentesting
- Simulates insider threats.
- Provides a comprehensive evaluation of the security of internal systems.
- Enhances compliance and security standards.
Limitations of Internal Pentesting
- More effective on internal IT networks.
- The complexity of internal systems hinders vulnerability detection and impact assessment accuracy.
- The effectiveness of the testing can be constrained by the lack of skilled red team assessment personnel.
- External Penetration Testing.
External Penetration Testing
External web application penetration testing aims to identify security weaknesses outside the company’s network rather than within.
This security testing process encompasses applications accessible via the Internet. Testers simulate a hack from an outsider’s perspective, attempting to gain system access without prior knowledge of the organization’s IT infrastructure.
This test targets IDs, servers, and firewalls. Initially, testers use the company’s IP address exclusively, without additional data, and rely on public internet resources for information gathering. If they acquire details about the target web component, they leverage this insight to compromise it.
Advantages of External Pentesting
- Mimics real-world attacks, probing web, mobile, and network vulnerabilities to provide an accurate assessment of an organization’s security posture against genuine threats.
- It provides a fresh perspective, as internal IT security teams may overlook blind spots or become accustomed to existing setups. External testers approach your defenses from an outsider’s standpoint, free from any biases.
- Meets industry regulations mandating regular security assessments by independent third-party providers, ensuring compliance, and furnishing unbiased reports for auditors.
- Partnering with an external web app penetration testing service provider can be more cost-effective than maintaining an in-house team of security experts, particularly for organizations with limited resources.
Limitations of External Pentesting
- External web pentesting provides a snapshot of the website’s security posture at a particular point in time. Any vulnerabilities that arise after the testing cannot be detected.
- With an external provider, organizations may have to limit the scope of their pen tests or rely on them to test only specific areas.
- Working with third parties often involves communication hurdles that can cause inordinate delays.
Benefits of Web Application Penetration Testing
Ensure Compliance
Penetration tests enable your business’s transactions, processes, and functions to stay compliant and up-to-date with the constantly changing data privacy laws and regulations.
They allow companies to pinpoint and remediate functions that are non-compliant with the current industry standards and apply strong security measures that protect sensitive information.
Interestingly, some industries require businesses to perform penetration tests on their web applications to achieve compliance.
Assess Risks
When launching your web applications, it is common to have security flaws, technical problems, misconfigured firewalls & DNS servers, UX issues, and other weaknesses. Before launching the defective product to the public, developers can leverage penetration tests to identify and mitigate all weaknesses and security concerns in the target application’s infrastructure.
This practice ensures businesses release an ironclad version with minimal security or data leak concerns that is less likely to be attacked.
Safeguarding Sensitive Data
The dark web is a significant marketplace where bad actors use cryptocurrency to buy and sell stolen data. This illegal data marketplace is the primary motivation behind attacks purportedly targeting web-based data-driven applications that hold invaluable information about businesses and their users.
Another top motive that drives attackers to steal web application data is its value to a business’s competitors. Subjecting your web application to a comprehensive penetration test is crucial to managing and curbing data leak risks that could affect the company and its reputation. Doing so reduces the application’s attack surface and safeguards its valuable data.
Additionally, the enhanced safety provided by periodic pen tests upholds the company’s reputation as one that values the security of its users data.
Common Tools Used in WAPT
Kali Linux and Parrot Security are ideal and effective operating systems (OS) for web application penetration testing. Some popular tools used are OWASP ZAP, Arachni, Burp Site, Nessus, Nikto, and WPScan testers for dynamic application security testing (DAST), and Snyk Code, Semgrep, SonarQube, and Fortify Static Code Analyzer for static application security testing (SAST).
Finding security vulnerabilities in your dependencies while developing and testing your applications requires tools such as OWASP Dependency Check and Snyk io.
It is worth noting that while automated tools are excellent means to scan and identify the most common vulnerabilities quickly, they have their limitations and are prone to generating false positives.
Only through manual testing can you help find more complex business logic vulnerabilities. Manual testing is also an efficient way to reduce false positives and verify actual vulnerabilities.
To summarize, while automated tools significantly improve the process, an experienced tester employs both methodologies for the best results.
Why Choose SecureLayer7
SecureLayer7, a CREST-certified vulnerability assessment and penetration testing provider, has over a decade of experience conducting advanced web app penetration services for customers worldwide.
Here are the following USPs that set us apart from the competition:
- Specialized Pentesting Services: We offer a wide range of penetration services, including web and mobile app vulnerability assessment, cloud infrastructure penetration testing, IoT pentesting, source code audits, and more, making us a one-stop solution for all web app pentesting needs. .
- Certified and Globally Vetted Experts: Our team comprises certified experts with industry-recognized certifications like CREST, CISSP, CEH, and CISA, enabling us to provide the highest quality pentesting services.
- Global Reach: With over 70,000 hours of service to 150+ clients spread across the USA, the Middle East, and India, SecureLayer7 has the reach and expertise to cater to specific client needs.
- Innovative Tools: Unlike our competitors, we use in-house tools like BugDazz, a pentest-as-a-service platform that allows customers to gain end-to-end visibility of security posture and remediation workflows with compliance-ready reports.
- Hybrid Pentesting Approach: We follow a combination of automated and manual pentesting, allowing us to completely eliminate false positives.
- Industry Certifications: SecureLayer7 holds industry-recognized certifications such as Certified AppSec Practitioner (CAP), Certified Network Security Practitioner (CNSP), CREST Certified and Recognized Vulnerability Assessment and Penetration Testing Provider,SOC 2 Type II Compliance Certification, ISO/IEC 27001:2013, and ISO 9001:2015. This reflects our commitment to quality and expertise.
- Unique Depth and Breadth of Industry Experience: We have helped 26+ Fortune 100 companies, 6 of the top 10 manufacturers, 8 of the top 10 tech companies, and 10 of the top 20 retailers. It allows us to better understand your unique industry-specific security needs.
- Zero-Day Vulnerability: We assist in uncovering Zero-Day web app vulnerabilities and promptly address and disclose issues. Once the penetration testing is over, we provide comprehensive reports detailing identified security gaps in web applications, firmware, and thick client software.
At SecureLayer7, our certified and experienced security professionals conduct thorough patch verification to ensure all vulnerabilities are successfully remediated, thoroughly securing web applications. We guarantee high-quality results while optimizing costs.
Get in touch with us to learn how we can assist in identifying and mitigating web app security.
Final Thoughts
In short, your business-critical data residing on the internet can harbor security loopholes in design, storage, or configuration, potentially granting access to malicious threat actors. web applications offer undeniable convenience, cost-effectiveness, and value, but these advantages come with a certain level of risk.
Web application penetration testing can safeguard your valuable assets by identifying and addressing these vulnerabilities. Utilizing it can protect the web application environment, including web/application servers, application layers, and other areas, from malicious actors.
Frequently Asked Questions (FAQs)
The five stages of web penetration testing typically include reconnaissance, scanning, gaining access, maintaining access, and covering tracks. These stages involve systematically probing and testing the web application’s security measures to identify potential vulnerabilities and weaknesses.
Security frameworks that need web pentesting include the following:
• OWASP (The Open Web Application Security Project (OWASP)
• NIST (The National Institute of Standards and Technology)
• PCI DSS (The Payment Card Industry Data Security Standard (PCI DSS)
• ISO 27001
• GDPR and HIPAA
Some of the common question that needs to be asked include:
• What certifications do you hold?
• What’s your pen testing methodology?
• What do your pen test reports look like?
• Can I talk to a previous customer?
• Which certifications do your penetration testers hold?
• How do you ensure they stay updated with the latest industry trends and attack techniques?