Recently I got an assignment where I had to work on the Umbraco application – a free Open Source Content Management System built on the ASP.NET platform and is
SSRF Vulnerability in Feedproxy.aspx (CVE-2015-8813)
Let me get start with Server side request forgery (ssrf) attack found within the feedproxy.aspx. Those who new to SSRF, please follow this link.
I started off playing with the feedproxy.aspx, it is intersting page in Umbraco . the feedproxy.aspx is used to access the external resources using the URL GET parameter.
http://local/Umbraco/feedproxy.aspx?url=http://bobsite/index
once you change the URL to the http://local/Umbraco/feedproxy.aspx?url=http://127.0.0.1:80/index, you able to access the localhost application of the server.
Using this payload change the port number to perform port scanning of the server. It will be helpful to find the more details of the server.
For example:
http://local/Umbraco/feedproxy.aspx?url=http://127.0.0.1:25/index
http://local/Umbraco/feedproxy.aspx?url=http://127.0.0.1:8080/index
If the port number is closed, you will find the error message on the feedproxy.aspx page. Umbraco assigned bug ID U4-7457 and fixed the issue by adding && requestUri.Port == 80.
Fix commit:
https://github.com/umbraco/Umbraco-CMS/commit/924a016ffe7ae7ea6d516c07a7852f0095eddbce
CSRF Bypass Vulnerability (CVE-2015-8814)
The Umbraco assigned bug ID U4-7459, It was discovered that Umbraco enabled sensitive actions, such as editing a user account information was vulnerable to CSRF vulnerability.
The vulnerable code in templates.asmx.cs on the line number 75, it is executing save operation without verifying the actual CSRF token.
In the file SetAngularAntiForgeryTokensAttributes.cs, on line number 25, function allowing empty CSRF value, the CSRF vulnerability is triggering.
Find the more details on this fix on the below given link:
https://github.com/umbraco/Umbraco-CMS/commit/18c3345e47663a358a042652e697b988d6a380eb
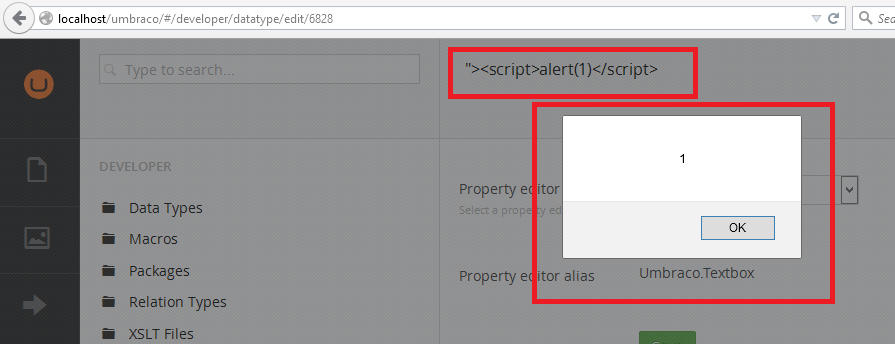
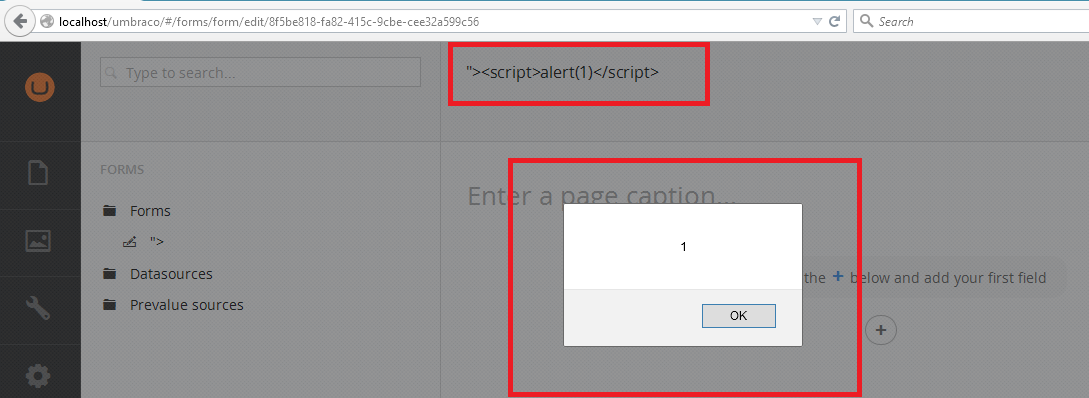
Persistent XSS Vulnerability(CVE-2015-8815)
It is found that Umbraco is also vulnerable to Persistent XSS in content type editor. Umbraco has been assigned bug ID U4-7461.. This vulnerability existed in the name field of the media page, the developer data edit page, and the form page.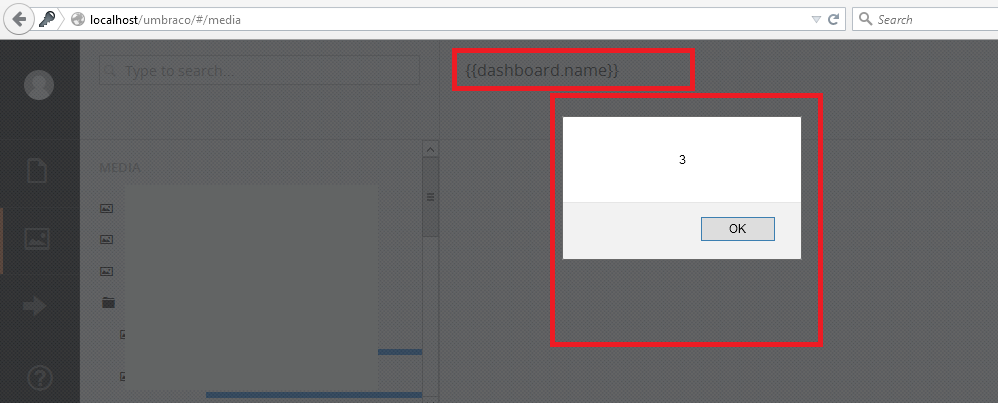
To mitigate these vulnerabilities, it is recommended to update Umbraco to the version V7.4.0.