Smart contracts have become a core building block of modern blockchain ecosystems, powering decentralized applications, DeFi platforms, and digital asset transactions without intermediaries. By automating business logic on public, permissionless networks, they enable transparency and efficiency at scale. This same openness and immutability make smart contracts a high-value target for attackers.
Organizations must adopt a comprehensive approach that combines secure-by-design development, thorough smart contract security audits, and proven best practices throughout the contract lifecycle. Understanding common risks, auditing methodologies, and preventive controls is essential for building resilient blockchain applications that protect user funds, maintain trust, and support long-term project sustainability.
Smart Contracts in Modern Blockchain Ecosystems
Smart contracts are self-executing programs deployed on blockchain networks that automatically enforce predefined rules without intermediaries. They form the backbone of modern blockchain ecosystems, enabling decentralized applications (dApps) across finance, gaming, supply chain, identity, and governance.
As blockchain adoption grows, smart contracts increasingly handle complex logic and high-value transactions. Their immutability and autonomous execution make them powerful – but also unforgiving. Any flaw embedded in the contract logic can persist indefinitely, emphasizing the need for strong security foundations from design through deployment.
Understanding the Role of Smart Contract Security Audits
Smart contract security audits are systematic reviews of contract code to identify vulnerabilities, logic errors, and design flaws before deployment. Audits typically combine manual code review with automated analysis to uncover issues such as reentrancy, integer overflows, access control weaknesses, and unsafe external calls.
Beyond finding bugs, audits validate whether contracts behave as intended under edge cases and adversarial conditions.
Why Smart Contract Security is Critical for Trust, Funds Protection, and Platform Stability
Smart contracts often directly control user funds and critical platform functions, making security inseparable from trust. A single vulnerability can lead to irreversible financial losses, reputational damage, and loss of user confidence. Unlike traditional systems, compromised smart contracts usually cannot be patched quickly or silently.
Robust smart contract security protects user assets, ensures predictable platform behavior, and supports long-term ecosystem stability. For projects seeking adoption, partnerships, or regulatory confidence, strong security practices are essential to demonstrating reliability and responsibility.
Understanding Smart Contract Security
Smart contract security focuses on protecting blockchain-based contracts from vulnerabilities that can lead to financial loss or misuse. Because smart contracts execute autonomously and are immutable once deployed, even minor flaws can be exploited with irreversible consequences.
Understanding smart contract security is critical for building reliable blockchain applications, as decentralized and public execution environments leave no room for post-deployment fixes.
How Smart Contracts Differ from Traditional Application Code
Smart contracts differ fundamentally from traditional application code in how they are deployed, executed, and governed. Traditional applications typically run on centralized servers where developers can patch bugs, roll back changes, or disable features if issues arise.
Smart contracts directly manage digital assets and enforce rules automatically. As a result, errors in smart contracts have immediate, irreversible effects, making secure design and validation far more critical than in conventional software development.
Security Challenges Introduced by Immutability and Decentralization
Immutability and decentralization are core strengths of blockchain technology, but they also introduce significant security challenges for smart contracts. Once a contract is deployed, its code cannot be modified, patched, or silently fixed. Any vulnerability embedded in the logic becomes a permanent part of the system, creating long-term exposure if it is not identified and addressed before deployment.
Decentralization further amplifies this risk by removing centralized control or intervention mechanisms. Combined with full public visibility of contract code, these properties give attackers unlimited time to analyze contracts and exploit weaknesses, making proactive security design and thorough audits essential.
Why Vulnerabilities Cannot Be Easily Patched After Deployment
A smart contract is deployed, patching a vulnerability is rarely straightforward. Fixes typically require deploying a new contract and migrating users, balances, and integrations, a process that can be technically complex and disruptive. In many cases, funds may already be locked or drained before corrective actions can be taken.
Even when upgrade mechanisms exist, such as proxy patterns, they introduce additional complexity and risk if not implemented securely. This reality makes pre-deployment security – through secure coding practices, rigorous testing, and thorough audits – far more effective than post-deployment remediation, reinforcing why smart contract security must be treated as a foundational requirement rather than an afterthought.
Why Smart Contracts are Prime Targets for Attackers
Smart contracts are prime targets for attackers because they directly manage valuable digital assets on public, permissionless blockchains where code and transactions are fully visible. Their immutable nature means vulnerabilities cannot be easily fixed after deployment, and even small flaws can be exploited repeatedly through automated attacks, making smart contracts highly attractive for financially motivated adversaries.
Direct Custody of Digital Assets and Tokens
Smart contracts often have direct control over digital assets, including cryptocurrencies, tokens, NFTs, and locked liquidity pools. Unlike traditional applications where assets are typically protected behind multiple backend layers, smart contracts frequently act as the final authority over fund movement.
This direct custody makes smart contracts especially attractive targets. A single flaw can result in immediate and large-scale financial loss, with little to no opportunity for recovery, raising the stakes far beyond most conventional application vulnerabilities.
Public Visibility of Smart Contract Source Code
Smart contracts deployed on public blockchains are transparent by design. Their source code or bytecode is openly accessible, allowing anyone – including attackers to analyze contract logic in detail. While transparency supports trust and verification, it also enables adversaries to thoroughly study contracts, identify subtle logic flaws, and test exploit scenarios offline before launching attacks.
This asymmetry favors attackers, who can spend unlimited time reviewing contract behavior without detection. As a result, even minor oversights or edge-case bugs can be discovered and weaponized once a contract goes live.
Real incidents show how quickly public code weaknesses can be weaponized, see SecureLayer7’s case write-up on an NFT marketplace vulnerability: SQL Injection Vulnerability in Xhibiter NFT Marketplace
Permissionless Interaction Model
Smart contracts typically operate within a permissionless interaction model, meaning any user or system can interact with contract functions without prior authorization. While this openness is fundamental to decentralized blockchain networks, it significantly expands the attack surface.
Because access cannot be limited at the network level, smart contracts must defend themselves entirely through on-chain logic. Every function, input, and state transition must be designed with the assumption that it will be called by an adversary. Secure permission checks, strict input validation.
High Financial Incentives and Automated Exploitation
The financial incentives for attacking smart contracts are exceptionally high. Successful exploits can yield instant profits, often worth millions of dollars, with minimal risk of reversal. This has led to the rise of highly skilled attackers and automated bots that continuously scan blockchain activity for vulnerable contracts.
A vulnerability is identified, exploitation can be fully automated and executed within seconds, often before defenders can react. This combination of high rewards and automation makes smart contracts one of the most aggressively targeted components in the blockchain ecosystem.
OWASP Smart Contract Top 10 (2026) – Key Risks
The OWASP Smart Contract Top 10 (2026) provides the latest industry-backed list of the most critical vulnerabilities affecting blockchain applications. Compared to earlier versions, the 2026 update reflects evolving attack patterns, DeFi risks, and complex contract logic issues.
Following are the Top 10 Smart Contract Security Risks (2026):
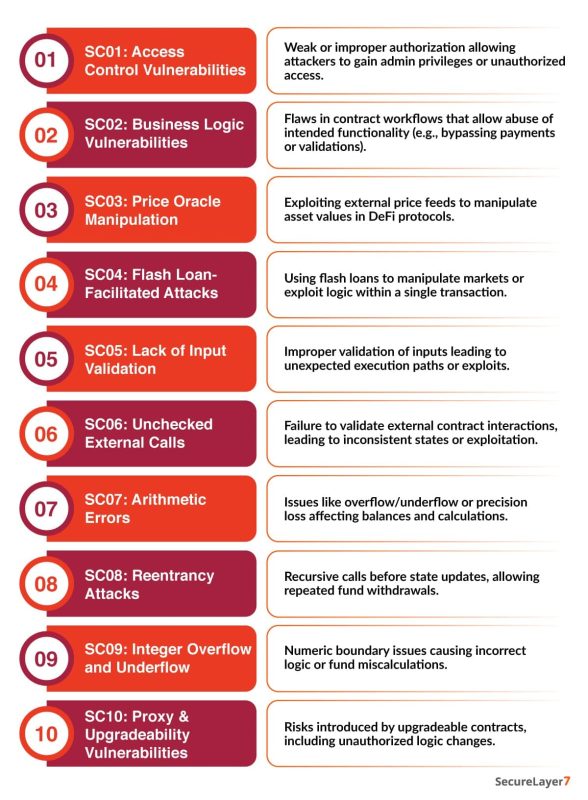
Key Takeaways from the 2026 Update
- Shift toward business logic risks: Traditional bugs are no longer the only concern – logic flaws are now top threats.
- Rise of DeFi-specific attacks: Flash loans and oracle manipulation dominate modern exploits.
- New risks from upgradeability: Proxy patterns introduce new attack surfaces if not secured properly.
Secure Smart Contract Development Best Practices
Building secure smart contracts requires more than fixing vulnerabilities after development. Because smart contracts are immutable once deployed, security must be embedded into the design, implementation, and testing phases.
The following best practices form the foundation of secure smart contract development and help minimize the risk of exploitation in real-world blockchain environments.
Secure-by-Design Approach for Smart Contracts
A secure-by-design approach treats security as a core architectural requirement, not an afterthought. Smart contracts should be designed with the assumption that attackers will attempt to exploit every possible edge case, logic flaw, and interaction path.
This approach emphasizes threat modeling, minimizing complexity, and clearly defining trust boundaries before writing code. By anticipating failure scenarios and adversarial behavior early, development teams can prevent entire classes of vulnerabilities rather than patching issues later.
Principle of Least Privilege for Roles and Permissions
The principle of least privilege ensures that each role or function within a smart contract has only the permissions necessary to perform its intended task. Overly permissive roles significantly increase the attack surface and make privilege escalation attacks more damaging.
Administrative functions, upgrade mechanisms, and emergency controls should be tightly restricted, well-documented, and auditable. Clear separation between user, operator, and admin roles reduces the impact of compromised accounts or misconfigurations.
Input Validation and State Consistency Checks
All external inputs to a smart contract should be treated as untrusted. Input validation ensures that parameters meet expected formats, ranges, and conditions before being processed.
Equally important is enforcing state consistency. Contracts should validate that the system is in the correct state before executing critical logic and that state transitions occur in a predictable, controlled manner. This prevents logic manipulation, replay scenarios, and unintended execution paths.
Safe Handling of External Calls and Dependencies
Smart contracts frequently interact with external contracts, tokens, or oracles. These interactions introduce additional risk because external code execution cannot be fully controlled or trusted.
To mitigate this risk, contracts should minimize external calls, update internal state before interacting externally, and avoid assumptions about external contract behavior. Dependencies should be well-audited, actively maintained, and widely adopted within the ecosystem to reduce exposure to hidden vulnerabilities.
Secure Error Handling and Failure Scenarios
Error handling in smart contracts must be explicit and intentional. Silent failures, unchecked return values, or unhandled exceptions can leave contracts in inconsistent or exploitable states.
Secure contracts are designed to fail safely, ensuring that unexpected conditions revert execution, preserve state integrity, and prevent partial completion of sensitive operations. Clear failure paths also make contracts easier to audit and reason about during security reviews.
Smart Contract Security Audit Process
A smart contract security audit is a structured, multi-phase assessment designed to identify vulnerabilities, logic flaws, and design weaknesses before contracts are deployed to production. Given the immutable nature of blockchain systems, audits play a critical role in preventing irreversible financial losses and safeguarding user trust.
Following are the detailed overview of the smart contract security audit process followed by mature security teams.
Pre-Audit Readiness and Documentation Requirements
The effectiveness of a smart contract audit depends heavily on pre-audit readiness. Auditors require complete and accurate documentation to understand the intended behavior, architecture, and assumptions behind the contract.
This phase typically includes reviewing:
- Smart contract source code and build artifacts
- Architecture diagrams and system workflows
- Business logic descriptions and economic models
- Deployment configurations and upgrade mechanisms
- Known constraints, dependencies, and trust assumptions
Static and Dynamic Code Analysis
Static analysis involves examining the smart contract code without executing it. Automated tools scan for known vulnerability patterns such as re-entrancy, access control issues, unsafe arithmetic, and improper error handling.
Dynamic analysis complements this by testing the contract during execution. Auditors simulate transactions, edge cases, and adversarial behavior to observe runtime behavior, gas usage, and state transitions.
Manual Logic Review and Threat Modeling
Automated tools alone cannot identify complex business logic flaws or economic vulnerabilities. Manual code review is essential for understanding how the contract behaves under real-world conditions. Auditors perform threat modeling to identify potential attacker goals, abuse paths, and failure scenarios.
This includes analyzing:
- Contract state transitions
- External integrations and dependencies
- Privileged roles and upgrade logic
- Incentive structures and economic assumptions
Vulnerability Classification and Risk Scoring
Identified findings are categorized based on severity, exploitability, and potential impact. Vulnerabilities are typically classified into levels such as critical, high, medium, or low risk.
Risk scoring considers factors like:
- Likelihood of exploitation
- Financial impact and asset exposure
- Ease of remediation
- Scope of affected functionality
Remediation Guidance and Post-Audit Validation
A security audit does not end with vulnerability identification. Auditors provide actionable remediation guidance, including recommended code changes and secure design improvements.
Post-audit validation verifies that:
- All identified vulnerabilities have been properly resolved
- Fixes did not introduce new issues
- Contract behavior aligns with security and business requirements
Tools and Techniques for Enhancing Smart Contract Security
Securing smart contracts requires a combination of automated tools, rigorous testing techniques, and human-driven review processes. Given the immutable nature of blockchain deployments, vulnerabilities must be identified and mitigated before contracts go live.
The following tools and techniques form a comprehensive approach to strengthening smart contract security across the development lifecycle. If you are validating an entire Web3 application (contracts + APIs + front end).
SecureLayer7’s Guide To Web3 Penetration Testing explains a practical testing approach
Static Analysis and Linting Tools
Static analysis tools examine smart contract source code without executing it to detect common vulnerability patterns, insecure coding practices, and deviations from best practices. These tools help identify issues such as re-entrancy risks, access control weaknesses, unsafe arithmetic, and improper error handling early in development.
Linting tools complement static analysis by enforcing coding standards, improving code readability, and reducing human error. By integrating these tools into continuous integration (CI) pipelines, teams can catch security issues consistently as code evolves.
Formal Verification Methods
Formal verification uses mathematical models to prove that a smart contract behaves exactly as intended under all possible conditions. Instead of testing specific scenarios, this method verifies correctness against predefined specifications and invariants.
Formal verification is especially valuable for contracts that manage large amounts of value or implement complex logic. While resource-intensive, it provides a high level of assurance that critical properties – such as fund safety and access restrictions, cannot be violated.
Fuzz Testing and Simulation
Fuzz testing involves supplying smart contracts with random, unexpected, or malformed inputs to uncover edge cases and unexpected behavior. This technique helps identify vulnerabilities related to state transitions, arithmetic errors, and input handling that may not surface during traditional testing.
Simulation environments allow auditors and developers to model real-world usage patterns, attacker behavior, and extreme conditions. Together, fuzzing and simulation provide insight into how contracts behave under stress and adversarial conditions.
Testnet Deployments and Peer Reviews
Deploying smart contracts to test networks enables teams to observe real execution behavior in a blockchain environment without risking real assets. Testnet deployments help validate gas usage, transaction flows, upgrade mechanisms, and failure scenarios.
Peer reviews further strengthen security by introducing independent perspectives. Reviewing code with experienced developers and security professionals often reveals logic flaws or risky assumptions overlooked by the original authors.
Preventing Smart Contract Exploits in Production
Smart contract is deployed to a live blockchain network, it becomes public, immutable, and continuously exposed to attackers. At this stage, prevention shifts from code-level fixes to operational security, monitoring, and response readiness.
The following practices are essential for preventing smart contract exploits in production environments.
Secure Deployment Practices
Secure deployment begins with controlled release processes and strict validation before contracts go live. Deployment artifacts, configuration parameters, and constructor values must be carefully reviewed to ensure they match audited versions of the code.
Production deployments should use dedicated deployment wallets, multi-signature approvals, and repeatable scripts to reduce human error. Verifying deployed bytecode against audited source code helps ensure that no unintended changes are introduced during deployment.
Upgradeability and Proxy Pattern Risks
Upgradeability mechanisms, such as proxy patterns, allow contracts to be updated after deployment, but they also introduce new attack surfaces. Improperly secured upgrade functions can enable attackers to replace logic contracts or gain control over upgrade processes.
To mitigate these risks, upgrade permissions must be tightly restricted, well-documented, and auditable. Clear separation between proxy administration and business logic reduces the likelihood of privilege abuse or accidental misconfiguration.
Monitoring On-Chain Activity for Anomalies
Continuous monitoring of on-chain activity is critical for early detection of exploitation attempts. Monitoring systems should track abnormal transaction patterns, unexpected state changes, unusual gas consumption, and unauthorized access attempts.
Real-time alerts enable security teams to respond quickly to suspicious behavior, potentially limiting the impact of an attack before significant damage occurs.
Emergency Pause and Kill-Switch Mechanisms
Emergency controls such as pause functions or kill switches provide a last line of defense during active exploitation. These mechanisms allow authorized operators to temporarily halt sensitive operations, preventing further loss while the issue is investigated.
Because emergency controls themselves can be abused, they must be carefully designed, minimally scoped, and protected by strong access controls. Their existence and limitations should be transparent to users.
Business Impact of Smart Contract Security Failures
Smart contract security failures extend far beyond technical issues. Because smart contracts directly manage digital assets and enforce business logic, a single vulnerability can trigger severe financial, legal, and reputational consequences.
Understanding the business impact of smart contract security failures is critical for organizations building or operating blockchain-based platforms.
Financial Losses and Frozen Assets
Smart contract exploits often result in immediate and irreversible financial losses. Attackers can drain funds, manipulate token supplies, or permanently lock assets within compromised contracts. In many cases, stolen or frozen assets cannot be recovered due to the immutable nature of blockchain transactions.
Beyond direct theft, organizations may face indirect financial losses through halted operations, emergency remediation efforts, and compensation to affected users. Even projects that survive an exploit often struggle to restore full economic functionality.
Reputational Damage and Loss of User Trust
Trust is foundational to blockchain ecosystems. A publicly exploited smart contract undermines user confidence, investor sentiment, and partner relationships. Because blockchain activity is transparent, security failures are quickly exposed and widely discussed across the community.
Rebuilding trust after an incident is difficult and time-consuming. Users may permanently abandon the platform, liquidity providers may withdraw funds, and strategic partnerships can dissolve following a high-profile security breach.
Legal and Regulatory Implications
As blockchain adoption grows, regulators are increasingly scrutinizing digital asset platforms. Smart contract security failures can expose organizations to legal liabilities, regulatory investigations, and compliance violations, especially when user funds or sensitive data are affected.
Projects may face lawsuits, enforcement actions, or mandatory disclosures depending on jurisdiction. Failure to demonstrate reasonable security controls and due diligence can significantly worsen legal outcomes.
Long-Term Sustainability Risks for Blockchain Projects
Repeated or severe security failures threaten the long-term viability of blockchain projects. Loss of capital, community support, and regulatory confidence can stall development, limit funding opportunities, and hinder ecosystem growth.
In competitive blockchain markets, security incidents can permanently damage a project’s credibility, making it difficult to attract developers, users, or enterprise adoption. Sustainable blockchain platforms are those that prioritize security as a core business requirement, not just a technical concern.
Conclusion
Smart contract security is a foundational requirement for Web3 success, not an optional safeguard. As smart contracts increasingly manage valuable assets and critical logic, security failures can lead to irreversible financial loss and long-term trust erosion. Building secure, audited smart contracts is essential for protecting users and ensuring platform stability.
Security audits serve as a proactive risk-mitigation strategy, helping organizations identify and address vulnerabilities before exploitation. At SecureLayer7, we enable teams to build trust through secure-by-design development and rigorous smart contract audits. Secure your smart contracts today with SecureLayer7, before vulnerabilities become breaches.
Frequently Asked Questions (FAQs)
Smart contract security is fundamentally different because smart contracts are immutable, autonomous, and publicly accessible once deployed. Unlike traditional applications, vulnerabilities cannot be easily patched, transactions cannot be reversed, and attackers can continuously exploit flaws in a transparent, permissionless environment.
A smart contract security audit should be conducted before deployment to a production blockchain. Ideally, audits are performed after core development is complete but before final release, and again after any significant code changes, feature additions, or protocol upgrades.
No. Automated tools are effective at identifying known vulnerability patterns, but they cannot detect complex logic flaws, economic exploits, or design-level issues. Manual audits are essential for understanding business logic, attacker incentives, and real-world abuse scenarios.
Smart contracts should be audited whenever material changes occur, including new features, upgrades, dependency updates, or architectural modifications. Long-running or high-value protocols should also undergo periodic re-audits to account for evolving attack techniques and ecosystem changes.
The first step is adopting a secure-by-design mindset. This includes threat modeling early in development, minimizing complexity, enforcing strict access controls, validating inputs, and planning for failure scenarios.


