Denial of Service (DoS) attacks are among the most disruptive cybersecurity threats, designed to overwhelm systems, networks, or applications and make them unavailable to legitimate users. Rather than stealing data or exploiting software flaws, DoS attacks target availability by exhausting bandwidth, server resources, or application capacity.
Understanding the different types of DoS attacks, their potential impact, and effective prevention strategies is critical for building resilient systems. From simple traffic floods to sophisticated distributed attacks, DoS threats continue to evolve alongside modern infrastructure. A proactive, layered defense approach – combining monitoring, scalable architecture, and response planning helps organizations reduce risk and maintain reliable service availability.
Why DoS Attacks Remain a Major Cybersecurity Threat
Denial of Service (DoS) attacks remain a major cybersecurity threat because they directly disrupt service availability, which is critical for modern businesses that rely on always-on digital platforms. As organizations increasingly depend on websites, cloud services, APIs, and online applications, even short outages can lead to revenue loss, operational downtime, and customer dissatisfaction.
The growing use of cloud infrastructure, connected devices, and distributed systems has further increased exposure to DoS attacks. Misconfigurations, exposed services, and unsecured endpoints provide attackers with more opportunities to overwhelm systems. Attack traffic often mimics legitimate user behavior, making detection harder and response slower.
How DoS Attacks Disrupt Availability, Performance, and Business Operations
DoS attacks disrupt availability by exhausting critical resources such as bandwidth, CPU, memory, or application threads, preventing legitimate users from accessing services. Systems under attack may become extremely slow, unresponsive, or crash entirely. This degradation affects not only external-facing services but can also impact internal applications and dependent systems.
From a business perspective, these disruptions can halt operations, delay transactions, interrupt customer services, and affect employee productivity. Prolonged or repeated DoS incidents may lead to revenue loss, breach of service-level agreements (SLAs), customer churn, and reputational damage.
Difference Between DoS and Broader Availability Attacks
A Denial of Service (DoS) attack typically originates from a single source or a limited set of systems targeting a specific service or resource. Traditional DoS attacks are often easier to detect and mitigate because the traffic source is limited.
Broader availability attacks, such as Distributed Denial of Service (DDoS) attacks, involve multiple compromised systems working together to overwhelm a target. These large-scale attacks generate massive traffic volumes and are harder to block due to their distributed nature. While DoS is a subset of availability attacks, modern threats often combine multiple techniques, making availability protection a critical focus of cybersecurity strategies.
What is a DoS Attack?
A Denial of Service (DoS) attack is a cybersecurity threat where an attacker deliberately overwhelms a system, network, or application to make it unavailable to legitimate users. Instead of breaking into systems or stealing data, the attacker focuses on disrupting normal operations by exhausting resources such as bandwidth, processing power, or memory.
DoS attacks are particularly disruptive because availability is a core requirement for digital services. When users cannot access a website, application, or online service, business operations, customer experience, and trust are immediately affected.
Core Goal of a DoS Attack: Making Systems Unavailable to Legitimate Users
Denial of Service (DoS) attack is to disrupt the availability of systems, applications, or networks so that legitimate users can no longer access them. Instead of stealing data or breaching security controls, DoS attacks focus on overwhelming the target with excessive traffic or requests, exhausting critical resources such as bandwidth, processing power, memory, or connection limits.
When these resources are depleted, systems become slow, unstable, or completely unresponsive. Legitimate users experience service outages, failed transactions, or long delays, while business operations are interrupted. By targeting availability, DoS attacks can cause immediate financial loss, damage customer trust, and impact service reliability.
How Attackers Target Networks, Servers, Applications, and Services
Attackers target networks, servers, applications, and services by overwhelming them with traffic or requests designed to exhaust critical resources. At the network level, attackers flood bandwidth using massive volumes of packets, preventing legitimate traffic from reaching the destination. For servers and infrastructure, they exploit limitations in CPU, memory.
At the application and service layer, attackers focus on resource-intensive functions such as login pages, search queries, APIs, or database calls. Cloud services and SaaS platforms are also targeted by exploiting auto-scaling limits or shared resources, turning normal application behavior into a denial-of-service condition that disrupts availability for legitimate users.
SecureLayer7’s API penetration testing guide explains how testing can surface these weaknesses and help harden endpoints against such abuse.
Common Targets: Websites, APIs, Cloud Services, Enterprise Networks
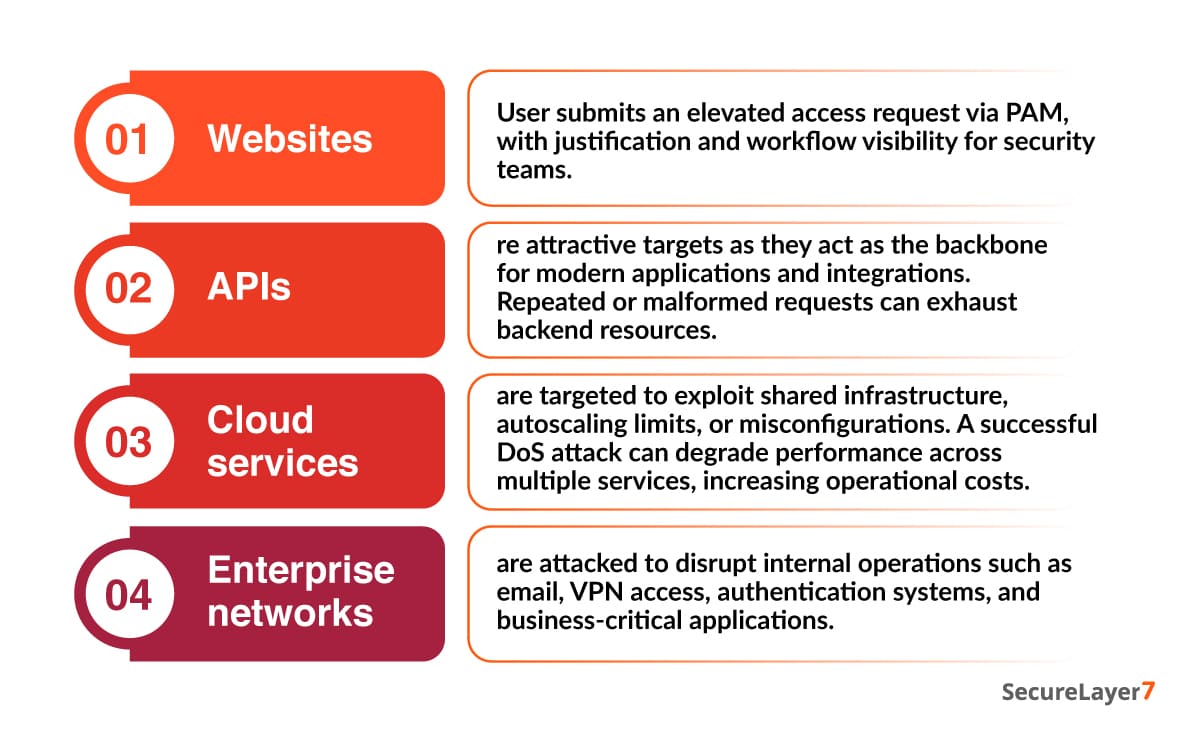
- Websites are frequent DoS targets because they are publicly accessible and directly impact customer experience and revenue.
- APIs are attractive targets as they act as the backbone for modern applications and integrations. Repeated or malformed requests can exhaust backend resources.
- Cloud services are targeted to exploit shared infrastructure, autoscaling limits, or misconfigurations. A successful DoS attack can degrade performance across multiple services, increasing operational costs.
- Enterprise networks are attacked to disrupt internal operations such as email, VPN access, authentication systems, and business-critical applications.
How a DoS Attack Works
A Denial of Service (DoS) attack works by overwhelming a system to the point where it can no longer respond to legitimate user requests. Rather than breaking into systems or stealing data, attackers exploit capacity limits by forcing networks, servers, or applications to handle more traffic or requests than they are designed to support.
As resources become exhausted, services slow down or stop functioning altogether. DoS attacks can operate at different layers – network, server, or application – depending on the attacker’s objective and the target’s weaknesses.
Exhausting Server, Network, or Application Resources
Exhausting server, network, or application resources is a core technique used in Denial of Service (DoS) attacks to disrupt normal operations and make systems unavailable to legitimate users.
- Server level: Attackers aim to consume CPU, memory, disk I/O, or process limits by sending excessive or malformed requests. As resources are depleted, servers struggle to handle normal workloads, leading to slow response times, crashes.
- Network level: Attackers flood bandwidth with large volumes of traffic, saturating network links and preventing legitimate data from reaching the target.
- Application level: Attackers target resource-intensive functions such as authentication, database queries, file uploads, or API calls. These attacks may use relatively low traffic volumes but repeatedly trigger expensive operations, gradually draining application resources.
Difference Between Bandwidth Exhaustion and Resource Exhaustion
Bandwidth exhaustion and resource exhaustion are two common techniques used in Denial of Service (DoS) attacks, but they target different layers of a system.
- Bandwidth exhaustion focuses on overwhelming the network connection itself. Attackers flood the target with massive volumes of traffic, consuming all available bandwidth so legitimate requests cannot reach the system.
- Resource exhaustion, on the other hand, targets the internal resources of a system rather than the network link. Attackers send requests that consume CPU, memory, threads, or application-level resources such as database connections.
Simple Step-by-Step Flow of a Typical DoS Attack
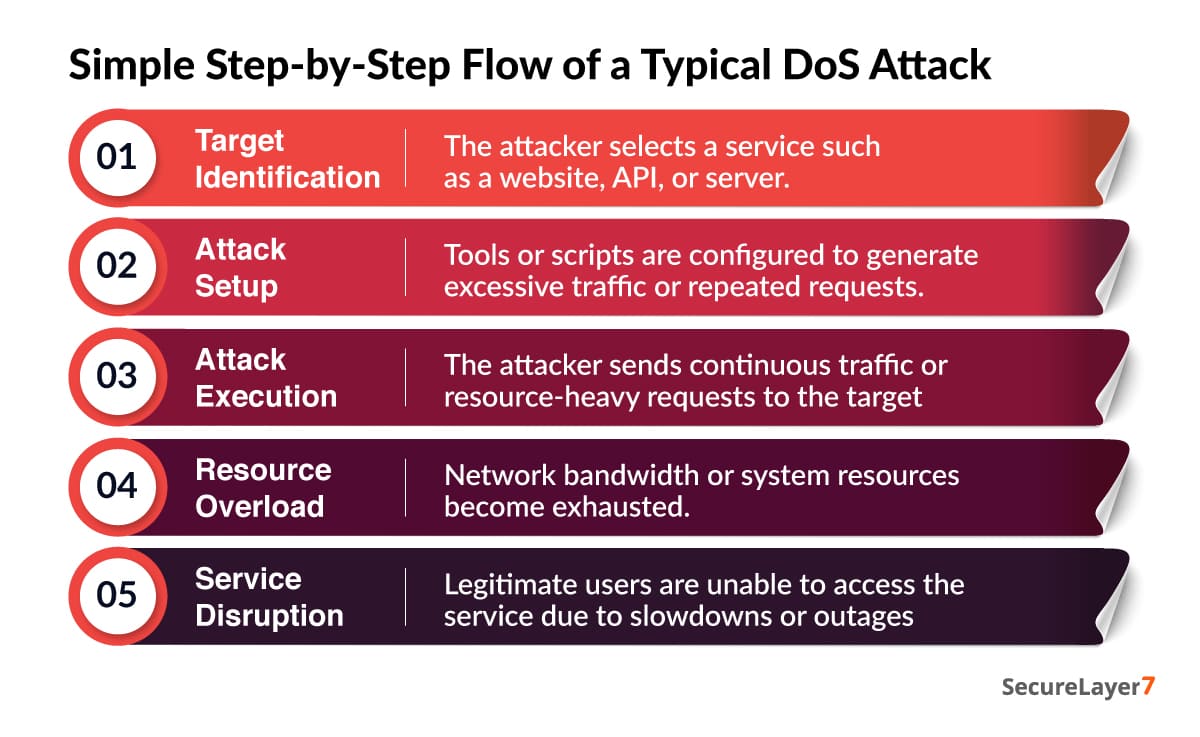
- Target Identification: The attacker selects a service such as a website, API, or server.
- Attack Setup: Tools or scripts are configured to generate excessive traffic or repeated requests.
- Attack Execution: The attacker sends continuous traffic or resource-heavy requests to the target.
- Resource Overload: Network bandwidth or system resources become exhausted.
- Service Disruption: Legitimate users are unable to access the service due to slowdowns or outages.
Types of Denial of Service Attacks
Denial of Service attacks can be classified based on the layer they target and the method used to exhaust resources. The end goal remains the same – making systems unavailable to legitimate users – the techniques vary significantly. Understanding these attack types helps security teams recognize attack patterns, assess potential impact, and implement effective mitigation strategies.
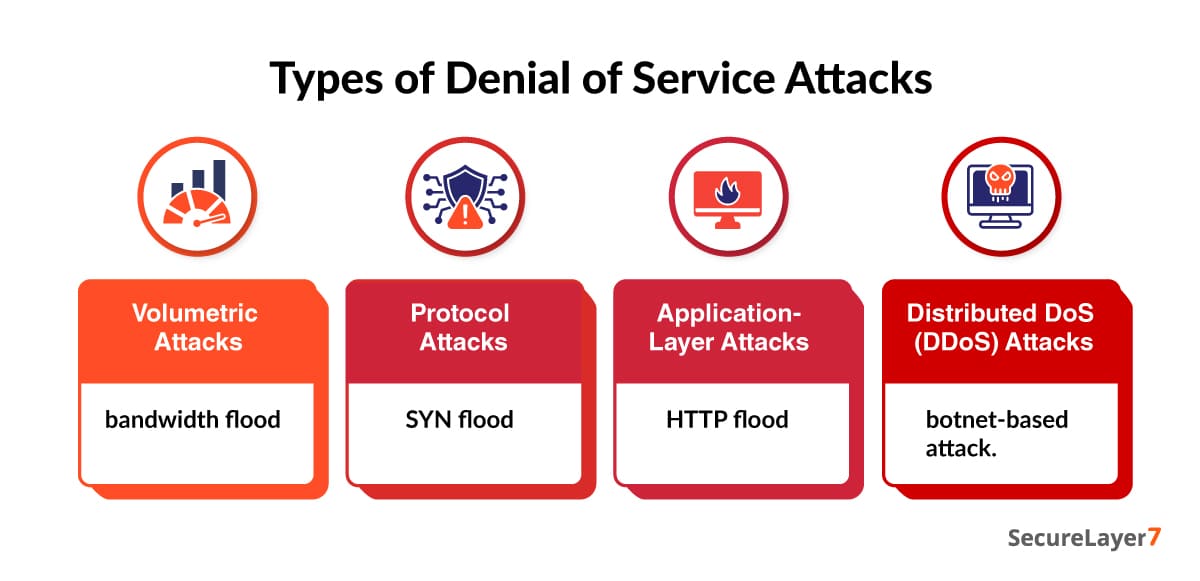
Volumetric Attacks
Volumetric attacks are designed to consume all available network bandwidth between the target and the internet. By flooding the target with massive amounts of traffic, attackers prevent legitimate requests from reaching servers, effectively cutting off access.
Common examples include:
- UDP Floods: Attackers send a high volume of UDP packets to random or targeted ports, forcing the server to respond and consuming bandwidth.
- ICMP Floods (Ping Floods): Massive numbers of ICMP echo requests overwhelm network links and devices.
Protocol Attacks
Protocol attacks target weaknesses in network and transport layer protocols to exhaust server or networking device resources.
Following attacks consume critical resources such as connection tables, memory, or CPU on servers, firewalls, or load balancers – often causing services to slow down or crash entirely.
Examples include:
- SYN Floods: Attackers send a large number of TCP connection requests without completing the handshake, filling up the server’s connection queue.
- Ping of Death: Malformed or oversized packets cause systems to crash or behave unpredictably.
Application-Layer Attacks
Application-layer attacks focus on specific application functions, such as web pages, login endpoints, APIs, or search features. Instead of overwhelming bandwidth or protocols, these attacks exhaust application-level resources like CPU, memory, threads, or database connections.
Common examples include:
- HTTP Floods: Repeated requests to dynamic pages overwhelm web servers or backend databases.
- Slowloris Attacks: Attackers keep multiple connections open by sending partial requests, exhausting server connection limits.
Distributed DoS (DDoS) Attacks
Distributed Denial of Service (DDoS) attacks amplify the impact of DoS attacks by launching them from multiple sources simultaneously. Instead of relying on a single system, attackers use botnets, networks of compromised computers, servers, and IoT devices – to generate traffic.
Key differences between DoS and DDoS:
- DoS: Originates from a single source or limited set of systems.
- DDoS: Originates from thousands or even millions of distributed devices.
Common Targets and Impact of DoS Attacks
Denial of Service (DoS) attacks are designed to disrupt availability by targeting systems that are critical to digital operations. Attackers focus on services that must remain accessible to users, customers, and internal teams, knowing that even short outages can cause significant damage.
It can lead to revenue loss, degraded customer trust, operational disruption, and long-term reputational harm, making it essential for organizations to understand which assets are most at risk and how these attacks affect business continuity.
Websites and Web Applications
Public-facing websites and web applications are among the most frequent DoS targets because they are easily accessible and directly tied to user experience and brand reputation. By overwhelming web servers with traffic or requests, attackers can make pages load slowly or become completely unavailable.
The impact includes loss of customer trust, reduced user engagement, and negative brand perception. For organizations that rely on their website for lead generation, customer support, or information sharing, even brief downtime can result in lost revenue and missed business opportunities.
APIs and Backend Services
APIs and backend services are frequent targets of DoS attacks because they act as the core communication layer between applications, users, and data sources. Attackers often flood APIs with excessive requests or abuse poorly protected endpoints, causing service slowdowns or complete outages.
When backend services are overwhelmed, the impact quickly spreads across dependent systems. Applications may fail to load data, transactions may time out, and user-facing services can become unavailable. In modern cloud-native and microservices architectures, a DoS attack on a single backend component can trigger cascading failures, disrupting entire platforms and business operations.
Cloud Infrastructure and SaaS Platforms
Cloud infrastructure and Software-as-a-Service (SaaS) platforms are high-value DoS targets due to their shared, scalable nature. Attackers aim to exhaust compute resources, bandwidth, or service limits, causing performance degradation or service disruption.
The impact can extend beyond a single customer, potentially affecting multiple tenants on the same platform. DoS attacks in cloud environments can also lead to unexpected cost spikes, SLA violations, and compliance issues if availability requirements are not met.
E-Commerce and Online Services
E-commerce platforms and online services are prime DoS targets because downtime directly translates to financial loss. Attackers often launch DoS attacks during peak traffic periods such as sales events, product launches, or holidays to maximize disruption.
The consequences include abandoned shopping carts, failed transactions, payment processing issues, and customer churn. In competitive markets, prolonged outages can push customers toward competitors, resulting in long-term revenue and reputation damage.
Signs and Indicators of a DoS Attack
Denial of Service (DoS) attacks are often designed to overwhelm systems quickly, but the warning signs usually appear before a complete outage occurs. Recognizing these indicators early can help security and IT teams respond faster, limit damage, and restore availability. Following are the most common signs that may indicate an ongoing or impending DoS attack.
Sudden Traffic Spikes
DoS attack is a sudden and abnormal spike in traffic. This traffic often comes from unfamiliar sources, unusual geographic locations, or a high number of repeated requests hitting the same endpoint.
Unlike legitimate traffic surges (such as marketing campaigns or seasonal demand), DoS-related spikes are typically aggressive, sustained, and lack normal user behavior patterns. If traffic volume increases sharply without a clear business reason, it may signal an attack in progress.
Slow Network or Application Performance
DoS attacks frequently cause noticeable performance degradation across networks and applications. Pages may load slowly, transactions may take longer to process, and users may experience lag or intermittent failures.
This slowdown occurs because servers, bandwidth, or application resources are being consumed by malicious traffic, leaving insufficient capacity to handle legitimate requests. Performance issues that appear suddenly and worsen rapidly are strong indicators of a DoS attempt.
Unresponsive Services or APIs
As a DoS attack intensifies, critical services and APIs may become completely unresponsive. Applications that rely on backend services may fail to load data, authenticate users, or complete transactions.
For organizations with microservices or API-driven architectures, this can result in widespread service disruption even if only one component is targeted. Persistent unresponsiveness, especially under normal load conditions, is a clear warning sign of a DoS attack.
How to Prevent a Denial of Service Attack
Preventing Denial of Service (DoS) attacks requires a layered defense strategy that focuses on controlling traffic, protecting infrastructure, and maintaining service availability under stress. Because DoS attacks aim to overwhelm systems rather than exploit a single vulnerability, effective prevention combines network controls, cloud-based protections, and resilient architecture design.
Traffic filtering and rate limiting
Traffic filtering and rate limiting are foundational defenses against DoS attacks. By defining thresholds for how many requests a user, IP address, or API client can send within a given time frame, organizations can prevent systems from being overwhelmed by excessive traffic.
Rate limiting helps block abnormal request patterns early, while traffic filtering removes malicious or unnecessary traffic before it reaches critical resources. These controls are especially effective at stopping basic flooding attacks and protecting APIs, login endpoints, and application services from abuse.
DDoS Mitigation Services and CDNs
DDoS mitigation services and Content Delivery Networks (CDNs) play a critical role in absorbing and distributing large volumes of traffic. These services use globally distributed infrastructure to detect, filter, and mitigate malicious traffic closer to its source.
By routing traffic through a CDN or managed DDoS protection service, organizations reduce the load on origin servers and ensure that legitimate users can still access services even during large-scale attacks. This approach is particularly effective against volumetric and distributed attacks.
Load Balancing and Redundancy
Load balancing distributes incoming traffic across multiple servers or regions, preventing any single system from becoming a bottleneck. When combined with redundancy, it ensures that services remain available even if one component becomes overloaded or fails.
Redundant infrastructure – such as multiple data centers, failover systems, and backup resources – helps maintain uptime during attack scenarios. This approach limits the impact of DoS attacks by spreading traffic and enabling automatic recovery.
Network Firewalls and IPS/IDS
Firewalls, Intrusion Prevention Systems (IPS), and Intrusion Detection Systems (IDS) add another critical layer of defense. These systems analyze traffic patterns, detect suspicious behavior, and block malicious requests before they reach servers.
Advanced firewalls and IPS solutions can identify protocol abuse, malformed packets, and known attack signatures. Continuous monitoring through IDS also helps security teams respond quickly by identifying early indicators of a DoS attack.
Denial of Service (DoS) Response Plan
A Denial of Service (DoS) response plan defines how an organization prepares for, detects, and responds to attacks that threaten the availability of critical systems and services. Because DoS attacks can escalate rapidly and cause widespread disruption, having a structured response plan is essential to minimize downtime and operational impact. An effective DoS response plan combines technical controls, clear roles and responsibilities, and well-defined communication procedures.
Preparing a DoS Response Plan
Preparation is the foundation of an effective DoS response. Organizations should first identify critical assets and services that must remain available at all times, such as public-facing websites, APIs, authentication services, payment systems, and core business applications. Knowing what is most critical helps teams prioritize actions when an attack occurs.
Clear escalation paths and responsibilities should be defined in advance. This includes assigning ownership to security teams, network engineers, cloud administrators, incident managers, and leadership decision-makers.
Responding to an Active DoS Attack
When a DoS attack is suspected, the first step is to detect and confirm the incident. Teams should analyze traffic patterns, system metrics, and logs to distinguish malicious activity from legitimate traffic spikes. Accurate identification helps prevent unnecessary service disruptions.
Once confirmed, affected systems should be isolated to limit the attack’s impact. This may involve rerouting traffic, throttling specific endpoints, or temporarily restricting non-essential services. Organizations should immediately engage DDoS mitigation providers, CDNs, or cloud-based protection services to absorb and filter malicious traffic.
Post-Attack Recovery and Review
After the attack is mitigated, organizations should focus on restoring services fully and safely. Systems should be monitored closely to ensure stability, performance, and data integrity before removing temporary controls or restrictions.
A thorough post-attack review is critical for long-term resilience. Teams should analyze attack patterns, traffic sources, duration, and effectiveness of mitigation measures. Insights gained from this analysis should be used to strengthen defenses, refine detection thresholds, and update response playbooks.
DoS vs DDoS: Key Differences
Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks both aim to disrupt the availability of systems, networks, or applications. They differ significantly in how they are executed, the scale of impact, and the complexity involved in detecting and mitigating them. Understanding these differences is critical for designing effective defense strategies.
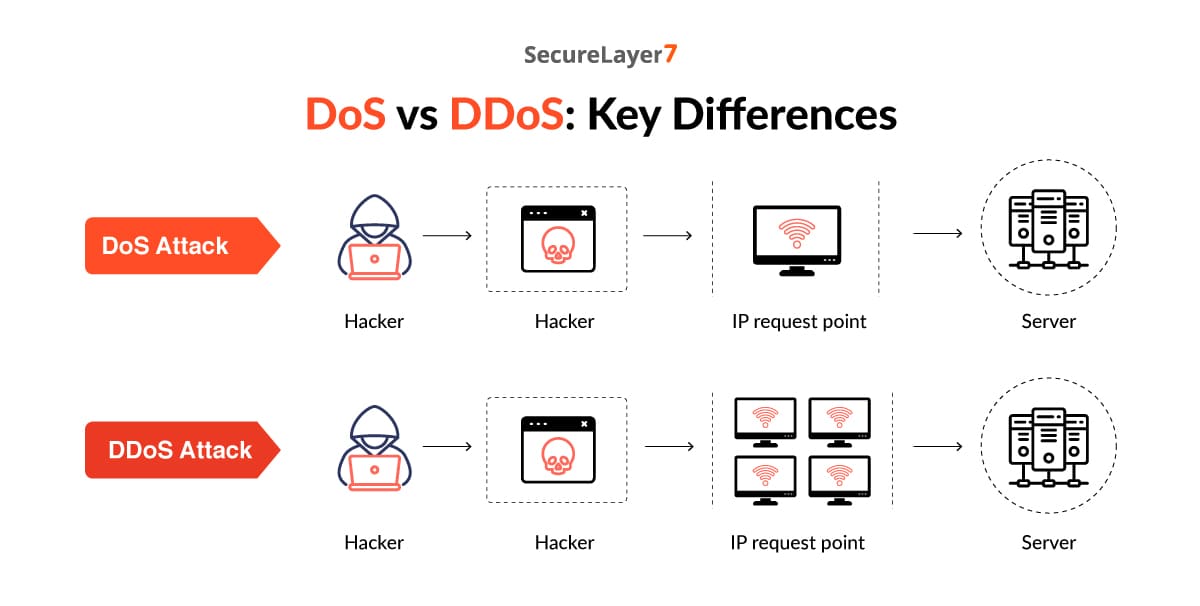
Single Source vs Distributed Sources
A DoS attack originates from a single system or source. The attacker uses one machine or network connection to flood the target with excessive traffic or requests, attempting to exhaust resources and make the service unavailable.
A DDoS attack, on the other hand, is launched from multiple distributed sources simultaneously. Attackers typically use botnets made up of compromised computers, servers, IoT devices, or cloud instances. Because traffic comes from many locations at once, DDoS attacks are far more difficult to block using simple IP-based filtering.
Attack Scale and Complexity
Attack scale and complexity are key factors that determine how damaging and difficult a Denial of Service attack can be to defend against. Smaller-scale attacks may originate from a single source and rely on basic traffic flooding or malformed requests, making them easier to detect and block using traditional firewalls or rate-limiting controls.
Larger and more complex attacks, especially distributed ones, involve massive volumes of traffic generated from thousands or even millions of compromised devices across different locations. This scale makes it harder to distinguish malicious traffic from legitimate users and overwhelms network bandwidth, servers, or applications.
Detection and Mitigation Challenges
DoS attacks are usually easier to detect and mitigate because traffic originates from a single or limited set of sources. Firewalls, rate limiting, and basic traffic filtering can often stop these attacks effectively.
DDoS attacks pose a much greater challenge. Because malicious traffic is distributed and may resemble legitimate user behavior, distinguishing attack traffic from normal traffic becomes difficult. Mitigating DDoS attacks often requires advanced detection, traffic analysis, and large-scale mitigation infrastructure such as CDNs, scrubbing centers, or cloud-based DDoS protection services.
Best Practices for Long-Term DoS Protection
Long-term protection against Denial of Service (DoS) attacks requires more than reactive controls. Organizations must adopt proactive, continuous security practices that strengthen resilience, improve visibility, and ensure infrastructure can withstand sustained attack conditions. Following are the best practices to help reduce risk and maintain service availability over time.
Continuous Traffic Monitoring
Continuous traffic monitoring is essential for detecting abnormal patterns early. By establishing baselines for normal traffic behavior, organizations can quickly identify sudden spikes, unusual request rates, or suspicious sources that may indicate a DoS or DDoS attack.
Real-time monitoring tools, dashboards, and alerts allow security and operations teams to respond faster and adjust mitigation controls before an attack escalates. Ongoing visibility also helps distinguish between legitimate traffic surges and malicious activity, reducing false positives and unnecessary service disruptions.
Cloud Scalability Planning
Scalability is a critical component of long-term DoS protection, especially in cloud and hybrid environments. Organizations should design infrastructure to scale dynamically in response to traffic surges, ensuring that legitimate users can still access services during high-demand or attack scenarios.
Effective scalability planning includes autoscaling policies, geographic distribution of resources, and integration with cloud-based DoS and DDoS protection services. This approach minimizes performance degradation and helps absorb attack traffic without manual intervention.
Security Awareness for IT and DevOps Teams
IT and DevOps teams play a central role in maintaining long-term DoS resilience. Security awareness training ensures these teams understand DoS attack patterns, early warning signs, and proper response procedures.
Educating teams on secure configuration, traffic management, and incident response reduces human error and improves coordination during attacks. Regular training also encourages a security-first mindset, ensuring availability and resilience are considered at every stage of system design, deployment, and maintenance.
Conclusion
Denial of Service (DoS) attacks remain a serious cybersecurity threat because they target availability, a core pillar of digital operations. Understanding how these attacks work, their types, impact, and warning signs is essential, but real protection comes from action – through proactive prevention, resilient architecture.
At SecureLayer7, we help organizations strengthen their defenses against DoS and DDoS threats through risk-driven security assessments, resilience testing, and tailored mitigation strategies. If your business depends on always-on digital services, now is the time to evaluate your readiness.
Partner with SecureLayer7 to proactively defend availability, reduce attack impact, and ensure your systems remain reliable when it matters most.
Frequently Asked Questions (FAQs)
A Denial of Service (DoS) attack is a cyberattack designed to make a system, network, or application unavailable to legitimate users. It works by overwhelming the target with excessive traffic or requests, exhausting its resources so it can no longer respond to normal user activity.
A DoS attack works by flooding a target system with more traffic or requests than it can handle. This overload consumes bandwidth, server capacity, memory, or processing power, preventing legitimate users from accessing the service.
The main types of DoS attacks include:
• Volumetric attacks, which overwhelm bandwidth with massive traffic floods
• Protocol attacks, which exploit weaknesses in network protocols to exhaust system resources
• Application-layer attacks, which target specific application functions using seemingly legitimate requests
• Distributed DoS (DDoS) attacks, which use multiple sources to amplify the impact
A DoS attack originates from a single source, making it relatively easier to detect and block. A DDoS (Distributed Denial of Service) attack comes from multiple sources, often using botnets of compromised devices. Because DDoS traffic is distributed and larger in scale, it is more difficult to detect, mitigate, and defend against.
DoS attacks commonly target:
• Websites and web applications
• APIs and backend services
• Cloud infrastructure and SaaS platforms
• E-commerce platforms and online services
• Enterprise networks and critical business systems



