With the increasing reliance on apps, API-related security attacks have also increased. The nature and complexity of such attacks have grown more sophisticated, and addressing them demands specialized expertise aligned with industry standards like the OWASP API Security Top 10 (2023 update).
But selecting the right API security vendor is not easy in a market where every provider appears the same.
For example, an API security testing vendor with limited discovery capability is more likely to miss critical API endpoint security gaps. Or, they may lack specialized tools to test critical vulnerabilities, such as broken function-level authorization, business logic abuse, or creating test cases.
The purpose of this blog is to help you address this challenge. We have curated a list of the top 12 API security testing companies for you.
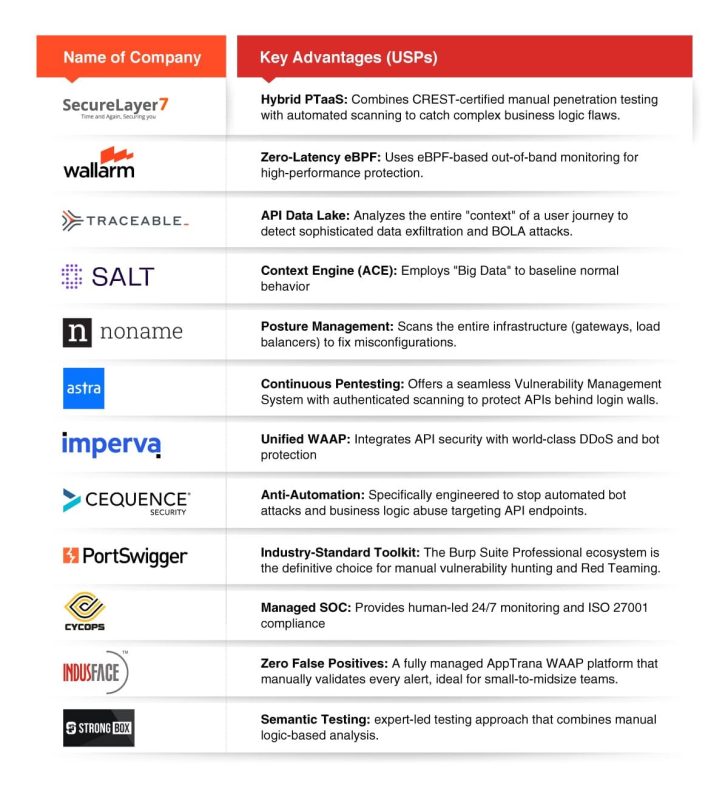
List of Top 12 Best API Security Companies
The purpose of the following list is to provide a starting point for businesses. It’s not a ranking of companies. Each of these companies has distinct capabilities catering to your unique security and business needs.
1. SecureLayer7

Based in Austin, Texas, SecureLayer7 specializes in penetration testing with robust API security testing capabilities. It offers a blend of manual and automated vulnerability scanning capabilities to uncover obvious and subtle API vulnerabilities, such as business logic flaws.
It adopts a hybrid approach that ensures thorough coverage, minimizing the chances of attacks, including those targeting publicly exposed APIs, shadow APIs, and compliance monitoring.
With over 12 years of experience, SecureLayer7 brings advanced best practices in API security. It has a robust team of CREST-certified API penetration testing experts who can root out every possible API security risk while ensuring adherence to the latest compliance standards.
Additionally, its powerful BugDazz API Security scanner automatically detects vulnerabilities as they emerge. This platform supports multiple API description formats and integrates seamlessly with CI/CD pipelines.
Key features:
- Blends manual and automated scanning capability
- Vetted and CREST-certified pentesters
- Unlimited number of scans available in both basic and enterprise version
- Supports REST and SOAP API
- Gartner-assessed pentest reports
- Dedicated project manager
Pros:
- Thorough coverage including complex business logic vulnerabilities
- Integration with JIRA, Jenkins, and ServiceNow
- Enables early detection by integrating into development workflows
- Supports diverse API types and authentication methods
- Continuous testing reduces breach risks
- Free trial available
- Basic plan starts with $3999 per year/license
Cons:
- More integration support needed in standard pricing as well.
2. Wallarm

Headquartered in San Francisco, USA, Wallarm is a leading API security company offering end-to-end API discovery, risk assessment, and real-time protection against API security threats. Wallarm’s unified platform provides comprehensive API discovery and defends against a full spectrum of risks, including API abuse and data leaks. Wallarm is a leader in eBPF-based solutions providing zero-latency monitoring.
The platform can be deployed on-premises and in cloud-native environments, with advanced capabilities to protect businesses from existing and emerging API threats.
Key features:
- Combines the power of managed API security testing and automated vulnerability scanning
- Protects in any environment that includes AWS, GCP, Azure, Kubernetes, and against any threat.
- Comprehensive API discovery with endpoint mapping and risk scoring
- API SOC-as-a-Service
- 24/7 monitoring and response
Pros:
- Flexible deployment: cloud, on-prem, hybrid
- Automatic BOLA Protection
- Robust incident response
- Easily Integrates with CI/CD and security tools
- Detailed traffic analysis
Cons:
- Setup can be a bit complex as reported by some users in review forums
- Cloud API uptime, false positives not shown in the web panel
- Pricing information not available.
3. Traceable

Counted among the best API security companies in India, Traceable helps businesses safeguard their API assets in today’s cloud-first world. It offers a comprehensive suite of API security solutions, including API discovery, security testing, attack detection, and protection. Traceable uses a unique API Data Lake approach to address these challenges effectively.
Its strong focus on API Data Lake and its eBPF-first architecture helps it standout in the crowd. Its merger with Harness has established them as a leader in the AI-native DevSecOps.
Key features:
- Offers automated API security testing
- Intelligent context aware approach
- Context aware security
Pros:
- Intuitive UI
- Full-spectrum API security testing
- Strong customer support
Cons:
- Automated API vulnerability detection
- Difficult to scale-up
- Heavy reliance on active API traffic and it may miss APIs without traffic or outside monitored gateways
- Complex integration
4. Salt Security

Salt Security offers API security solutions across all stages of the API lifecycle. It provides threat intelligence and detailed insights for API discovery, attack prevention, and the integration of security best practices. Powered by its proprietary API Context Engine (ACE), Salt enables comprehensive API discovery, attack mitigation, and remediation insights.
Salt Security has partnerships with CrowdStrike and Invicti. While it primarily offers automated scanning, its collaboration with Bright Security enables it to deliver hybrid security services.
Key features:
- Robust AI capabilities
- Seamless integration
- Dynamic run-time protection
Pros:
- API inventory management
- Strong customer support
- Easy-to-navigate UI
- Strong partnership with Invicti and CrowdStrike
Cons:
- Need more customization in some areas
- Some users have pointed scalability challenges
- Startup plan starts from $36,000
5. Noname Security(Akamai Security)

Founded in 2020 and now acquired by Akamai, Noname Security is a well-known vendor in the API security space. Its offerings cover the complete API security lifecycle, including posture management, runtime protection, and integration with the secure API software development lifecycle (SDLC).
Noname provides hybrid API testing solutions that combine manual penetration testing with automated vulnerability scanning. The platform integrates seamlessly with DevOps workflows, delivering high-quality, actionable vulnerability insights.
Key features:
- Identifies all APIs including managed, unmanaged, shadow, and discarded APIs
- Tests for both REST, SOAP APIs
- On-prem scanning available
- GraphQL API Support
Pros:
- Run-time anomaly detection
- Both manual and automated API security testing
Cons:
- Deployment can be slow and complex
- More suitable for network security engineers than developers
6. Astra Security

Astra Security, established in 2013, is a well-known name in API security, offering both automated and manual API penetration testing. It provides continuous penetration testing and comprehensive vulnerability management. Astra’s AI-driven penetration testing platform is recognized for its ease of use, scalability, and actionable insights, making it suitable for companies of all sizes and industries.
Astra’s standout feature is its authenticated scanning capability, which allows the platform to navigate complex login flows and test protected endpoints.
Key features:
- Comprehensive security coverage from API discovery, scanning, reporting, and remediation
- Low false positives rate
- Scans APIs behind login pages
- Supports authenticated and protected endpoints
- Compliance reporting for PCI-DSS, HIPAA, SOC2, and ISO 27001 standards.
Pros:
- Publicly verifiable safe-to-host certificates
- Seamless integration with CI/CD pipelines, JIRA, and Slack
- Tailored reports designed for both executives and engineers
- Scan APIs behind authenticated (logged-in) pages
Cons:
- Expensive for SMEs
7. Imperva

Imperva is counted among the top API security providers, offering robust protection for public, private, and shadow APIs. Leveraging its Web Application and API Protection (WAAP) platform that enables security teams to seamlessly integrate API security into their CI/CD workflows.
Imperva’s platform provides strong threat protection against API attacks and business logic abuse, regardless of where APIs are deployed: on-premises, in the cloud, or in hybrid environments.
Imperva’s primary USP (Unique Selling Proposition) is Unified WAAP (Web Application and API Protection) architecture.
Key features:
- Automated API discovery and classification
- Real-time threat detection
- Seamless WAF integration
Pros:
- Granular control over API traffic
- Compliance support to ISO/IEC 27001:2022, NIST
- Advanced bot protection
- Strong DDoS protection
Cons:
- Only automated API testing available
- Pricing on the expensive side
- Complex deployment and configuration
- Reports could be more granular
8. Cequence Security

Cequence Security, established in 2014 and headquartered in Santa Clara, has emerged as a powerful player in API security. It offers a Unified API Protection (UAP) platform to help businesses with API discovery, compliance, and protection across internal, external, and third-party APIs. Cequence serves an impressive list of Fortune 500 companies and global enterprises.
Key features:
- Full-spectrum API security testing from API discovery, compliance, and scanning
- Advanced level incident response
- API Edge protection
Pros:
- API risk classification
- Robust defense capabilities
- Fully operational within Kubernetes environment
- Effective customer support
- Extended data retention
Cons:
- Lack of customizable reporting option
- Steep learning curve to fully use the product
- Complex custom rule creation
9. Portswigger

Recognized globally for its Burp Suite platform, the industry-standard toolkit widely used by testers across the world. It enables organizations to secure their web applications.
Key features:
- Automated API scanning
- Helps visualize API attack surface
- Seamless integration with CI/CD pipeline
Pros:
- Loaded with power packed features
- Strong customer focus
- Large community
- Intuitive dashboard and UI
- Free trial available
- Pricing starts from $475
Cons:
- Steep learning curve
- Performance issues reported by users during intensive testing
- Monthly subscription not available
10. CyCops Infosec

CyCops Infosec, headquartered in Hyderabad, is a reputed cybersecurity company offering managed security solutions, including API security testing and secure software development consulting. It also provides SOC and managed services to clients.
Key features:
- Comprehensive offerings
- ISMS audit and implementation
- Compliance support
Pros:
- ISO/IEC 27001 certified
- Strong focus on proactive monitoring
- Rapid incident response with a dedicated SOC.
- Partnerships with global technology vendors
Cons:
- Limited publicly available information on automated scanning
11. Indusface

Powered by a fully managed AI-based solution, the Indusface platform is a global leader in application and API security. Its flagship product, AppTrana, protects users from DDoS attacks, bots, zero-day vulnerabilities, and OWASP Top 10 threats. With more than 5,000 customers worldwide, Indusface combines automated scanning with manual testing to deliver effective security for web and API environments.
Key features:
- Robust API discovery and protection
- Powerful vulnerability scanning capability
Pros:
- Comprehensive range of features
- Robust customer support
- Custom rules
- Easy-to-use dashboard
Cons:
- Reports could be better
- Monthly reports are not saved as reported by users
12. StrongBox IT

StrongBox IT is a well-known API security testing service provider offering extensive static and dynamic analysis to identify weak points such as insufficient authentication, data exposure, and injection flaws. Its testing approach focuses on API behavior. StrongBox has a skilled team of certified pentesters who analyze vulnerabilities and deliver detailed remediation reports.
Key features:
- Comprehensive API security offerings
- Offers manual API pentesting
- Robust red team assessment
- Certified experts
Pros:
- Robust compliance assistance for ISO27001, GDPR, HIPAA, PCI-DSS, SOC2
- Certified experts
Cons:
- Lacks automated scanning capabilities
Which API Security Company is Right for You? Quick Selection Guide
Factors to Consider While Selecting an API Security Testing Vendor
It’s no longer enough to simply “ask questions”; you must evaluate a vendor’s technical capabilities: Here are a few things you can use to evaluate your options:
A. Traffic Visibility & API Discovery Approach
Start by understanding how the company discovers and analyzes API traffic. Passive discovery is essential, but implementation matters.
- eBPF (Extended Berkeley Packet Filter): Vendors using eBPF operate at the kernel level, which empowers them with deep packet visibility without introducing latency or architectural friction. This is more suitable for high-performance, cloud-native environments.
- Sidecars / Agents: Sidecar-based inspection provides strong contextual visibility but can introduce performance overhead in high-throughput systems.
- Log-Based Analysis: Log-driven discovery is the most basic approach. It often lacks real-time behavioral context and may miss undocumented (“shadow”) or deprecated (“zombie”) APIs.
B. Business Logic & Authorization Risk Detection
Modern API security companies must go beyond injection flaws and detect stateful authorization weaknesses.
Ensure the vendor can detect:
- Broken Object Level Authorization (BOLA): Requires understanding user-object relationships across sessions
- Broken Function Level Authorization (BFLA): Detects privilege escalation where standard users access admin functions
- Mass Assignment: Identifies exposure of sensitive internal fields that can be manipulated by client-side input
These security issues dominate real-world API breaches and cannot be found with shallow scanning.
C. Continuous Monitoring, Compliance & Response Readiness
API security is not a one-time test. Evaluate how the company handles ongoing protection.
- Support for regulatory frameworks, such as GDPR and HIPAA through audit trails and automated reporting
- Continuous API behavior monitoring, not just periodic scanning
- Clear incident response workflows that adapt to evolving attack patterns
D. Platform Coverage & DevSecOps Integration
A capable API security company should integrate into your development lifecycle.
- Coverage across SAST, DAST, and SCA
- Ability to break the build on high-severity API vulnerabilities
- Support for REST, SOAP, and GraphQL architectures
- Seamless CI/CD integration without operational disruption
Bottomline: Getting Started
The success of API security posture depends on the partner you choose. The above list is not a final decision but it certainly provides you a starting point for businesses looking for a trusted API security partner who can strengthen your security posture.
Ignoring API security risks can be costly. At SecureLayer7, our experts are helping global enterprises to secure their digital assets. Contact us now to learn how we can help.
Frequently Asked Questions (FAQs)
Top API testing providers perform comprehensive security testing covering authentication, authorization, input validation, error handling, and injection flaws. They combine automated scans with manual testing to identify and prioritize critical vulnerabilities, preventing unauthorized access and data manipulation.
Leading providers support automation and integrate API security scans directly into CI/CD workflows, enabling early detection of vulnerabilities during development. This shift-left approach ensures continuous testing without disrupting release cycles, improving security posture while maintaining agility.
Providers typically use a mix of automated tools and manual techniques, including static code analysis, dynamic scanning, and penetration testing. They emphasize API inventory mapping, behavioral analysis, and adherence to standards to ensure thorough coverage and compliance.
Effective API testing includes load and stress testing to simulate high traffic and identify bottlenecks or failure points. Providers validate rate limiting and throttling controls to prevent abuse and ensure APIs maintain performance and availability under peak conditions.



