Whether you’re protecting a hospital’s patient records, a bank’s customer data, or a SaaS startup’s infrastructure, the goal remains the same: find the path the attacker sees before they do. That’s why understanding attack vectors becomes critical.
In this blog, we’ll explore what attack vectors are, their types and examples, and how you can defend against them.
What Is an Attack Vector?
An attack vector is the path or tactic used by attackers to gain unauthorized access to a system, network, or application. It involves exploiting software vulnerabilities, manipulating human behavior, or misusing legitimate credentials.
Recognizing such weak points allows organizations to implement layered defenses —strong authentication, timely patching, and continuous monitoring—before attackers can strike.
You cannot manage cyberattacks without a proper understanding of attack vectors, as they connect how breaches occur to why they succeed. According to IBM’s Cost of a Data Breach Report 2024, 82% of breaches involve human factors or misconfigurations.
It may start with a human error, such as clicking a phishing link or reusing weak passwords. Some attackers may also exploit misconfigured cloud services, unpatched systems, or insecure APIs that expose sensitive data. Each of these API endpoints may become an opportunity for intrusion.
Attack Vector vs Attack Surface
The harsh reality is the math is against you in cybersecurity. As a defender, you have to protect every single employee, every server, each API node, and every line of code. You have to be successful all the time.
An attacker only has to find one mistake to succeed. They don’t need to hack your firewall if they can just trick an exhausted employee into clicking a “Password Reset” link on a Friday afternoon.
Think of your business as a house:
- The attack surface is the size of the house. Every window, door, and chimney is a part of that surface.
- The attack vector is how the thief gets in—like using a crowbar on a window or stealing a spare key from under a mat.
Why ” Single Layer” Security is not Enough
Most people think a single strong password or a good antivirus is enough. But modern attacks are “chained.” An attacker might use a phishing vector to get a username, then use a vulnerability vector to escalate their permissions.
This is why we use defense-in-depth. It’s the idea that if a thief breaks the window, they should still find a locked safe inside.
The reality is you’ll never close every single attack vector. The goal isn’t to be “unhackable”.
Instead, the objective is to make your systems difficult and costly to compromise, encouraging attackers to seek easier targets.
Common Types of Attack Vectors
Cyberattackers have many ways to break into digital systems. Here are some common methods that show how serious their effects can be.
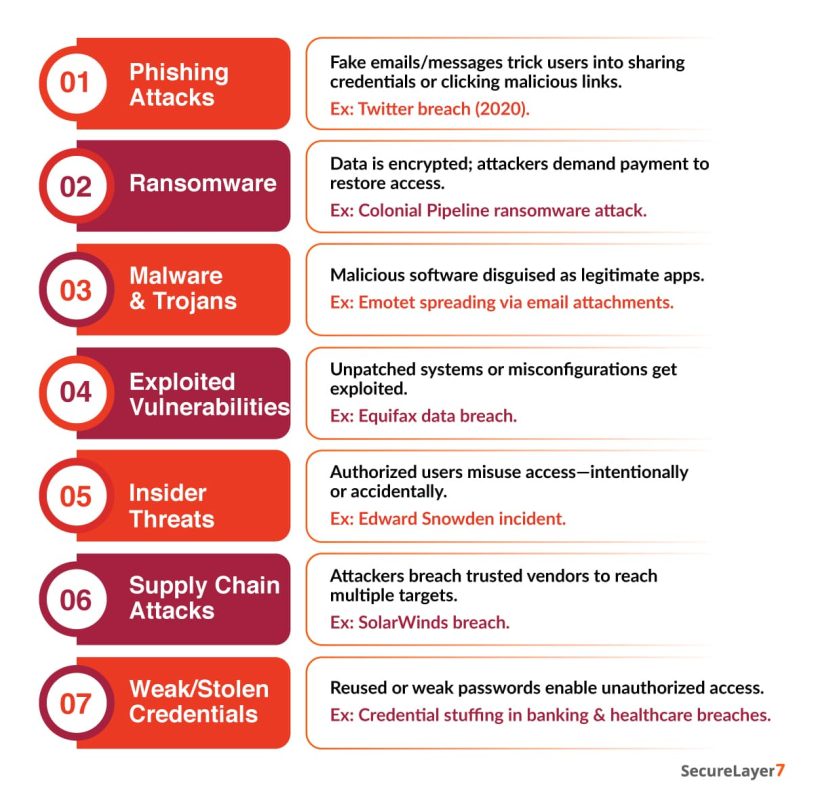
- Phishing: Attackers send fake emails or messages to trick people into giving away passwords or clicking harmful links. In 2020, for example, Twitter employees fell for a phishing scam that let hackers access major accounts, leading to scams and damage to Twitter’s reputation.
- Ransomware: Attackers use malicious software to encrypt data and demand payment for decryption keys. For example, the Colonial Pipeline attack in 2021 disrupted fuel distribution across the US East Coast, costing millions and prompting an emergency federal response.
- Malware and Trojans: These programs disguise themselves as legitimate software but execute harmful actions once installed. For example, the Emotet malware spreads through malicious attachments, infecting organizations globally and serving as a delivery system for other payloads.
- Exploited Vulnerabilities: Unpatched software or system misconfigurations create exploitable weaknesses. For example, the 2017 Equifax breach exploited an unpatched Apache Struts vulnerability, compromising the personal data of over 140 million individuals.
- Insider Threats: Employees or contractors with authorized access misuse privileges intentionally or accidentally. For example, the Edward Snowden incident exposed classified NSA data through insider misuse, emphasizing the human element in security risks.
- Supply Chain Attacks: Adversaries compromise a trusted vendor or service provider to infiltrate downstream clients. For example, the SolarWinds breach embedded malicious code in legitimate updates, impacting thousands of global organizations.
- Weak or Stolen Credentials: Attackers exploit reused, default, or easily guessed passwords to access systems. For example, numerous healthcare and financial breaches in recent years originated from compromised administrative credentials obtained through credential stuffing.
Each of these vectors underscores the critical need for layered security, including technical controls, employee awareness, and continuous monitoring.
Difference Between Passive and Active Attack Vectors
Understanding the difference between passive and active attack vectors is a fundamental step in building a proactive defense. A passive attack vector is about observation rather than direct interference, much like a burglar surveilling a property from the street without ever stepping foot inside.
In this phase, the attacker simply collects information, they monitor your network traffic or analyze public data to find a security gap in your system.
On the other hand, an active attack vector is the complete opposite; it is the moment the “break-in” actually happens.
This involves direct engagement with your systems to exploit weaknesses, launch ransomware, or execute targeted phishing campaigns. But what makes these threats so dangerous, and how do you build a strategy to stop them both?
Real-World Examples of Attack Vector
Several well-documented breaches highlight the scale and sophistication of modern attack vectors. The SolarWinds supply chain attack compromised trusted software updates, giving attackers access to thousands of networks, including government agencies.
This incident revealed how attackers can exploit trust in vendor relationships. Similarly, the Colonial Pipeline ransomware incident demonstrated the devastating potential of operational technology vulnerabilities.
A single compromised VPN password enabled the attackers to encrypt key systems, leading to fuel shortages and financial loss.
In another instance, Capital One suffered a data breach when an attacker exploited a misconfigured cloud firewall. The event reinforced the importance of securing cloud infrastructure and monitoring access policies rigorously.
Each case states the same principle: security gaps often emerge not from lack of technology, but from oversight and inconsistent governance.
How Attackers Exploit Common Attack Vectors
Exploitation is a disciplined progression where each phase is designed to bypass specific layers of a traditional security stack. By following a predictable lifecycle, adversaries maximize their success rate while minimizing their visibility.
This process typically follows a predictable pattern, aligned with the MITRE ATT&CK framework. Below, we have outlined a step-by-step exploitation mechanism:
1. Reconnaissance
The methodology begins with the mapping of the digital attack surface. Attackers utilize automated scanners and OSINT (Open Source Intelligence) to identify high-value targets.
The Mechanism: Harvesting leaked credentials, identifying misconfigured cloud buckets, and fingerprinting edge devices to find unpatched vulnerabilities or “Shadow IT” that lacks oversight.
2. Initial Access
Once a weakness is identified, the focus shifts to the breach. This is the transition from external observer to internal participant.
The Mechanism: Bypassing entry controls through weaponized email attachments, credential stuffing (using previously leaked passwords), or exploiting “Zero-Day” vulnerabilities in public-facing applications.
3. Payload Execution
After the initial breach, the attacker must ensure they don’t lose access if a system reboots or a user logs off.
The Mechanism: Running malicious code to establish a “foothold.” Attackers often use Living off the Land (LotL) techniques—using legitimate system tools like PowerShell or WMI—to hide their activity within normal system traffic.
4. Privilege Escalation
Standard user access is rarely the end goal. The methodology requires “Administrative” or “Root” authority to gain full control over the environment.
The Mechanism: Exploiting kernel-level vulnerabilities, harvesting tokens from system memory, or finding insecurely stored service account passwords to elevate their permissions to “God Mode.”
5. Lateral Movement
With elevated privileges, the attacker begins a horizontal search of the network. The goal is to move from the initial entry point to the location of the “Crown Jewels.”
The Mechanism: Using internal network scanning and remote desktop protocols (RDP) to jump from workstation to server, searching for databases, intellectual property, or financial systems.
6. Exfiltration
The final stage is the execution of the primary mission. This is where the technical exploit transforms into a business-altering event.
The Mechanism: Compressing and tunneling sensitive data out of the network via covert channels.
This methodology is inherently linear. Each stage provides the “infrastructure” for the next. If an attacker cannot move laterally, they cannot reach the data; if they cannot escalate privileges, they cannot disable the logs that would eventually expose their presence. Understanding this chain reveals the heavy dependency adversaries have on each successful step.
Key Prevention Strategies For Common Attack Vectors
You need to think beyond “checking boxes” and try to build an integrated ecosystem. Implementing NIST (National Institute of Standards and Technology) or CIS (Center for Internet Security) can be a good starting point. But the execution requires a deep understanding of how these layers interact: Here is a breakdown of how to operationalize those key strategies:
1. Identity and Access Management (IAM)
Identity is the new perimeter. Protecting it requires more than just a password.
- Deploy adaptive MFA to move beyond basic SMS codes toward hardware tokens or biometrics, utilizing risk-based authentication to trigger additional verification whenever a login attempt appears suspicious.
- Implement privilege access management to enforce the principle of least privilege through just-in-time access, ensuring administrators only receive elevated permissions for the specific duration required to complete a task.
2. Vulnerability and Asset Management
You cannot protect what you cannot see.
- Establish a real-time inventory of all hardware, software, and cloud assets to eliminate the massive blind spot created by “Shadow IT” and unauthorized applications.
- Apply the common vulnerability Scoring System (CVSS) to prioritize patches for flaws actively being exploited in the wild, ensuring critical weaknesses are closed before less impactful ones.
3. Network Defense-in-Depth
Traditional security is obsolete because threats often come from inside the walls.
- Break the network into small, isolated nodes. If a single workstation is infected with ransomware, micro-segmentation prevents that malware from “hopping” to the database server.
- Implement Zero-Trust architecture. Operate under the assumption that the network is already compromised. Every request—whether from inside or outside the office—must be verified and encrypted.
4. Human Firewall and Culture
Technology alone cannot stop a user from clicking a malicious link.
- Instead of annual videos, run monthly, randomized phishing tests. Use this result to provide extra coaching to high-risk departments (like finance or HR).
- Ensure employees feel safe reporting a mistake. If someone clicks a link, they should feel empowered to tell IT immediately rather than hiding it out of fear.
5. Detection, Response, and Auditing
Prevention will eventually fail; your “Mean Time to Detect” (MTTD) determines the level of damage.
- Use Security Information and Event Management (SIEM) to aggregate logs and Endpoint Detection and Response (EDR) to monitor individual devices for behavioral anomalies (e.g., a laptop suddenly trying to scan the entire network).
- Ensure your backups are offline or “air-gapped.” In a modern attack, hackers will target your backups first to ensure you have no choice but to pay the ransom.
Future Trends in Attack Vectors
The future of cyber threats will be shaped by automation, AI-driven attacks, and the expanding digital ecosystem. While these AI-powered tactics represent a leap in adversary sophistication, their effectiveness is amplified by the inherent vulnerabilities found in modern environments. This is particularly evident as cloud infrastructure continues to introduce new risks.
Cloud infrastructure continues to introduce new risks. Misconfigured storage buckets, exposed APIs, and insecure third-party integrations remain prime targets. As hybrid work environments expand, unmanaged endpoints and remote collaboration tools will further enlarge the attack surface.
Organizations must prepare for these challenges by integrating AI-driven defense mechanisms, continuous configuration monitoring, and adaptive identity controls to stay ahead of adversaries who now operate at machine speed.
The Bottomline
Every cyberattack begins with an entry point. Understanding attack vectors allows organizations to see where those entry points exist and how they can be secured.
By studying real incidents, aligning defenses with frameworks like NIST and MITRE ATT&CK, and maintaining vigilance across both infrastructure and human behavior, enterprises can significantly reduce risk. Cybersecurity success depends not only on technology, but also on awareness, discipline, and the ability to anticipate how attackers think.
Ignoring attack vectors can affect the cybersecurity posture of your organization. Contact us now to learn more about how you can defend your organization.
Frequently Asked Questions (FAQs)
Phishing remains the most common because it targets human behavior rather than technical flaws, making it difficult to eliminate completely.
A vulnerability is a weakness in a system; an attack vector is the specific route used to exploit that weakness.
Yes. Automation allows attackers to scan and exploit thousands of targets simultaneously, regardless of company size.
The NIST Cybersecurity Framework, MITRE ATT&CK, and CIS Controls provide structured methods to identify, protect, detect, and respond to cyber threats.
Continuously. Every software update, vendor integration, or configuration change can create new entry points that must be assessed and secured.


