Businesses depend on uninterrupted online services to operate smoothly and serve customers. This reliance makes them vulnerable to cyberattacks designed to disrupt availability – especially DoS (Denial of Service) and DDoS (Distributed Denial of Service) attacks. These attacks don’t steal data, they can cripple websites, APIs, and applications by overwhelming them with excessive traffic, causing costly downtime and service failures.
As attackers grow more sophisticated and DDoS attacks reach terabit-scale volumes, understanding how these threats work is essential for IT teams, cybersecurity professionals, and business leaders. With even a few minutes of downtime causing financial loss and reputational damage, learning to identify, prevent.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
A Denial-of-Service (DoS) attack occurs when a single source floods a system or network with an excessive number of requests, consuming resources such as bandwidth, memory, or processing power until legitimate users can no longer access the service.
A Distributed Denial-of-Service (DDoS) attack takes this concept to a much larger scale. It leverages multiple compromised devices – often part of a botnet made up of infected computers, IoT devices, or servers – to launch a coordinated attack from numerous points across the internet. Many such botnets originate from insecure connected devices, as explained in Introduction to Offensive IoT Exploitation.
How Both Disrupt Online Services but Differ in Scale and Execution
While both DoS and DDoS attacks seek to disrupt availability, their execution strategies set them apart:
- DoS attacks are simpler, typically launched by a single attacker or system targeting one endpoint. Because of their single-source nature, they are easier to identify and block.
- DDoS attacks, on the other hand, use hundreds or thousands of devices to send massive volumes of traffic from multiple locations.
Why Knowing Their Distinctions Matters for Cybersecurity Readiness
Understanding the differences between DoS and DDoS attacks is critical for building effective defense strategies. A single-source DoS attack might be mitigated with simple rate-limiting or firewall rules, but combating a large-scale DDoS assault requires advanced traffic analysis, distributed filtering, and automated response systems.
Organizations that fail to distinguish between these attack types risk underestimating their exposure or deploying inadequate protection. By staying informed, implementing real-time monitoring tools, and adopting Zero Trust and layered security frameworks, businesses can ensure greater resilience, maintain uptime, and safeguard their reputation against these ever-evolving threats.
What is a DoS Attack?
A DoS (Denial of Service) attack is a cyberattack where a single system floods a website, server, or network with excessive traffic or repeated requests, exhausting its resources and making it unable to serve legitimate users. This results in slow performance, partial outages, or complete service downtime.
DoS attacks are easy to launch using automated tools, and while smaller in scale than DDoS attacks, they can still disrupt business operations, delay customer transactions, and reduce service reliability – especially for smaller or poorly secured systems. For a detailed understanding of how attackers exploit, refer to: Denial of Service (DoS) Attack: Types, Impact, and Prevention
Define DoS (Denial of Service) Attack
A Denial of Service (DoS) attack is a malicious attempt to make a network, server, or application unavailable to legitimate users. It works by overwhelming the target system with a massive volume of unnecessary requests or traffic, preventing it from processing normal user activity. In simple terms, a DoS attack disrupts the normal functioning of a website or service, making it inaccessible for a period of time.
DoS attacks exploit vulnerabilities in network protocols, software configurations, or resource limits. They often target high-traffic websites, online platforms, and businesses that rely heavily on digital operations – causing significant inconvenience and potential financial loss.
How a Single System Floods a Target with Excessive Traffic or Requests
Unlike Distributed Denial of Service (DDoS) attacks, which use multiple systems or bots, a DoS attack originates from a single computer or network connection. The attacker uses specialized scripts or tools to continuously send large amounts of traffic or repeated requests to the target server. As the server struggles to handle the abnormal load, it either slows down drastically or stops responding altogether.
Common techniques used in DoS attacks include:
- Ping floods: Sending continuous ping requests to overload the target.
- SYN floods: Exploiting TCP handshakes to exhaust server resources.
- Application layer attacks: Repeatedly requesting complex operations like database queries.
Common Impacts of DoS Attacks
The effects of a DoS attack can range from minor slowdowns to complete service shutdowns. Some of the most common impacts include:
- Temporary website or application outages, resulting in lost revenue or damaged reputation.
- Slowed performance, making web pages or apps unresponsive to legitimate users.
- Increased operational costs, as businesses invest in mitigation tools and recovery measures.
What is a DDoS Attack?
A DDoS (Distributed Denial of Service) attack is a cyberattack where multiple compromised devices – usually part of a botnet – flood a target with excessive traffic to force it offline. Because the attack comes from many sources at once, the target’s bandwidth and resources are quickly overwhelmed.
DDoS attacks are far harder to detect and block than single-source DoS attacks. The distributed traffic appears to come from legitimate users, making filtering difficult and amplifying the attack’s impact.
Define DDoS (Distributed Denial of Service) Attack
A Distributed Denial of Service (DDoS) attack is an advanced form of a Denial of Service (DoS) attack where multiple compromised systems work together to overwhelm a single target – such as a website, application, or network resource. The goal remains the same: to disrupt normal traffic and make the targeted service unavailable to legitimate users.
Unlike a basic DoS attack that originates from a single source, a DDoS attack leverages a distributed network of infected devices – often computers, servers, or Internet of Things (IoT) devices to launch the assault simultaneously.
What Multiple Systems (Botnets) Are Coordinated to Target One Server or Service
DDoS attacks are typically carried out using botnets – large networks of compromised computers infected with malware and controlled remotely by cybercriminals. Each device, known as a bot or zombie, sends requests or data packets to the targeted server in unison.
Attackers often use Command-and-Control (C2) servers to manage these bots and alter their attack patterns dynamically, making it harder for defenders to predict or block them.
Common types of DDoS attacks include:
- Volume-based attacks: Flooding networks with high traffic (e.g., UDP floods, ICMP floods).
- Protocol attacks: Exploiting weaknesses in network protocols (e.g., SYN floods, fragmented packet attacks).
- Application-layer attacks: Targeting web servers or applications (e.g., HTTP floods) to drain resources.
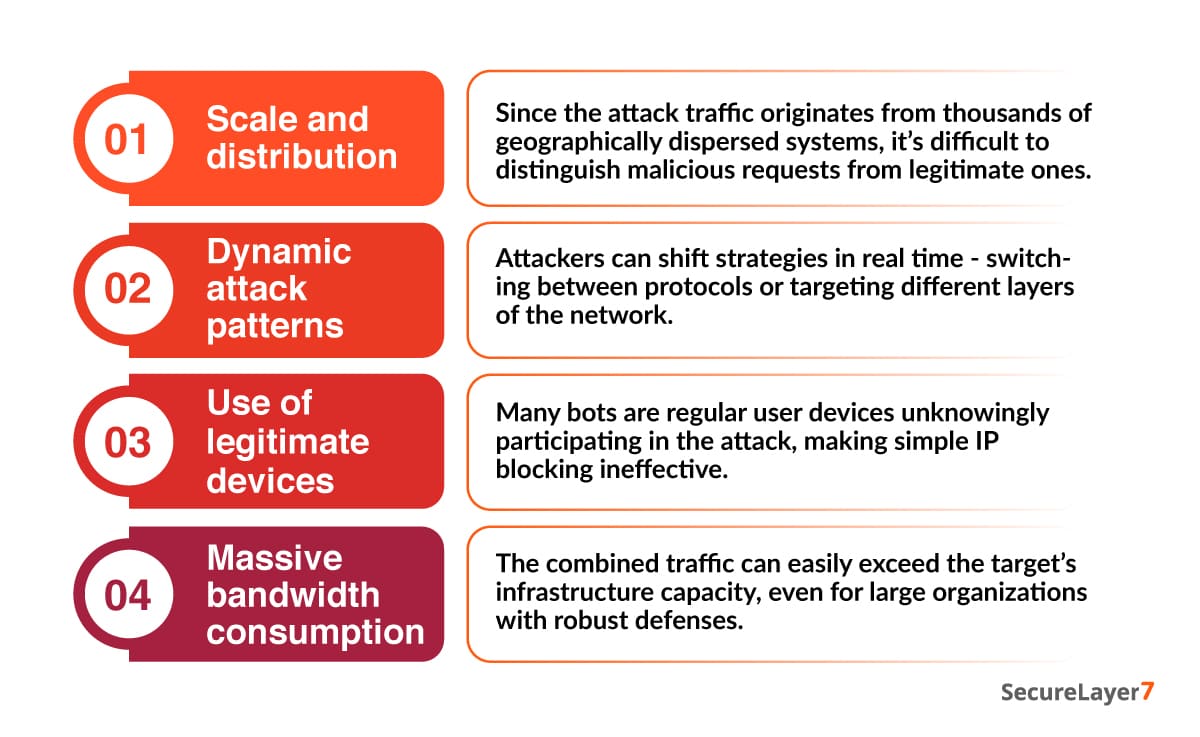
Why DDoS Attacks are More Complex and Harder to Mitigate
DDoS attacks are more complex and challenging to mitigate than single-source DoS attacks for several reasons:
Types of DoS Attacks
DoS attacks can be carried out in several ways; each targeting different layers of a system to overwhelm resources and disrupt normal operations. Understanding the main types of DoS attacks helps businesses recognize how attackers exploit bandwidth, protocols, and applications to cause outages.
The three primary categories – volumetric, protocol-based, and application-layer attacks – each use distinct techniques to overload systems and deny legitimate access.
Volumetric Attacks
Volumetric attacks aim to overwhelm the target by flooding its network bandwidth with an enormous volume of traffic. The attacker sends massive amounts of data packets, consuming all available bandwidth and preventing legitimate user requests from getting through.
Common examples include:
- UDP Flood: Attackers send a high volume of UDP packets to random ports, forcing the server to repeatedly check for non-existent applications.
- ICMP Flood (Ping Flood): Continuous ICMP Echo Request (ping) packets overload the network, exhausting both bandwidth and server processing power.
Protocol Attacks
Protocol attacks (also known as state-exhaustion attacks) target weaknesses in network protocols or server configuration. There is to exhaust resources such as firewall tables, load balancers, or session states by exploiting protocol-level vulnerabilities.
Examples include:
- SYN Flood: The attacker exploits the TCP handshake by sending repeated SYN requests without completing the connection, causing the server to waste resources waiting for responses.
- Ping of Death: Oversized or malformed ICMP packets cause system crashes or reboots due to buffer overflow vulnerabilities.
Application-Layer Attacks
Application-layer attacks focus on the topmost layer of the OSI model – the part that interacts directly with users. Instead of flooding bandwidth, they target specific applications, APIs, or web servers, often mimicking legitimate user behavior to stay undetected.
Popular examples include:
- HTTP Request Flood: Attackers repeatedly send HTTP GET or POST requests to overload the web server or database behind it.
- Slowloris: A stealthy attack where the attacker opens many partial connections and keeps them alive as long as possible, preventing the server from opening new legitimate connections.
Types of DDoS Attacks
DDoS attacks come in several forms, each leveraging distributed systems or botnets to overwhelm a target’s network, protocols, or applications. Understanding these attack types helps identify how attackers generate massive, coordinated traffic surges that disrupt services.
The main categories – volumetric, protocol-based, and application-layer DDoS attacks – use different techniques and target different layers of a system.
For deeper insights into application-layer attack techniques check: Application Layer DDoS Attack and How to Defend Against It
Volumetric DDoS Attacks
Volumetric DDoS attacks aim to overwhelm the target’s network bandwidth by flooding it with massive amounts of traffic from thousands of distributed bots.
Key traits:
- Traffic comes from multiple geographic locations, making simple IP blocking ineffective.
- Attackers often use amplification techniques to multiply traffic by exploiting open DNS, NTP, SSDP, or memcached servers.
Examples include:
- DNS Reflection: Attackers spoof the victim’s IP and trigger DNS servers to send large response packets to the target.
- NTP Amplification: Vulnerable NTP servers send significantly larger responses than the original request, amplifying the attack volume.
Protocol-Based DDoS Attacks
Protocol-based DDoS attacks exploit vulnerabilities in network protocols such as TCP, UDP, or ICMP at a massive distributed scale.
How they operate:
- Attackers use botnets to send malformed or incomplete packets.
- The volume and distribution of traffic force the target’s systems to allocate memory and processing power until they fail.
Examples include:
- SYN Flood (Distributed): Thousands of bots send half-open TCP handshakes simultaneously, overwhelming the server’s backlog queue.
- UDP Fragmentation Attacks: Fragmented packets require excessive processing before reassembly, straining the network stack.
Application-Layer DDoS Attacks
Application-layer DDoS attacks target the human-facing part of a service – web applications, APIs, login portals, checkout pages, and search functions. What makes them dangerous is that they use botnets to mimic legitimate user behavior, making detection extremely difficult.
How botnets attack application layers:
- Bots repeatedly send HTTP requests, API calls, or login attempts.
- Attackers target resource-heavy operations such as database queries or authentication workflows.
- Traffic appears normal, so traditional firewalls often fail to detect the anomaly.
Examples include:
- HTTP GET/POST Floods across distributed IPs.
- Botnet-driven Slowloris attacks, tying up server connections.
Use of Botnets and Amplification Methods
The power of DDoS attacks comes from botnets – networks of malware-infected devices like computers, servers, IoT gadgets, and even smart home appliances. Attackers also rely on amplification methods to increase their attack strength.
By sending small spoofed requests to vulnerable servers (DNS, NTP, SSDP), they force those servers to send large responses to the victim, amplifying the volume by 10x, 20x, or even 100x.
Common amplification techniques:
- DNS Reflection
- NTP Amplification
- SSDP Amplification
- Memcached Amplification
Examples of DoS Attacks
DoS attacks exploit different weaknesses in systems to overload resources and disrupt service availability. Understanding real-world examples helps illustrate how attackers use malformed packets, protocol flaws, or repeated connection requests to crash servers or slow down applications.
Following are some well-known DoS attack methods that highlight how these disruptions occur.
Ping of Death: Sending Malformed Packets to Crash Systems
The Ping of Death is a classic DoS attack where the attacker sends malformed or oversized ICMP packets to the target system. These packets exceed the maximum allowed size, causing buffer overflows during processing.
How it works:
- Attackers send ICMP packets larger than 65,535 bytes.
- When the system attempts to reassemble these packets, it crashes or reboots due to memory corruption.
Teardrop Attack: Overlapping Fragmented Packets Causing Reassembly Failures
The Teardrop attack exploits flaws in how systems handle fragmented IP packets. Fragmented packets include offset values that help systems reassemble them in the correct order. In a Teardrop attack, the attacker sends overlapping or inconsistent fragment offsets.
How it works:
- The target system receives fragmented packets that don’t align correctly.
- When attempting to reassemble them, the operating system becomes confused, leading to crashes or reboots.
SYN Flood Attack: Overwhelming TCP Connections from One Source
A SYN Flood attack takes advantage of the TCP three-way handshake used to establish connections. In this attack, the attacker sends a rapid stream of SYN requests from a single system but never completes the handshake.
How it works:
- The attacker sends repeated SYN packets to the server.
- The server allocates resources for each half-open connection.
- As the backlog queue fills up, the server becomes unable to accept new legitimate connections.
Examples of DDoS Attacks
DDoS attacks have caused some of the most disruptive outages in recent years, often affecting major platforms and global services. Incidents highlight how botnets, amplification methods, and massive distributed traffic can overwhelm even the most robust infrastructures.
Following are notable real-world examples that demonstrate the scale and impact of modern DDoS attacks.
GitHub DDoS (2018): 1.3 Tbps Memcached-Based Volumetric Attack.
In 2018, GitHub faced one of the largest DDoS attacks recorded at the time, peaking at 1.3 Tbps. Rather than using a botnet, attackers exploited memcached servers to launch a powerful amplification attack.
How it happened:
- Attackers sent spoofed requests to vulnerable memcached servers.
- These servers responded with extremely large packets directed at GitHub.
- The response-to-request amplification ratio reached 50,000x, making even small requests devastating.
Dyn DNS Attack (2016): Brought Down Twitter, Netflix, and Amazon
In 2016, the DNS provider Dyn was hit by a massive DDoS attack that disrupted some of the world’s largest online platforms, including Twitter, Netflix, Amazon, Reddit, and PayPal.
How it happened:
- The attack was powered by the Mirai botnet, consisting of hundreds of thousands of compromised IoT devices like webcams and routers.
- These devices were commanded to flood Dyn’s DNS infrastructure with overwhelming traffic.
AWS Attack (2020): Massive 2.3 Tbps Reflection Attack via Botnets
In 2020, Amazon Web Services (AWS) reported mitigating a massive 2.3 Tbps DDoS attack – the largest publicly disclosed attack at the time.
How it happened:
- The attack used a Reflection and Amplification method, leveraging vulnerable CLDAP servers.
- Botnets across multiple regions sent spoofed requests that resulted in extremely large responses directed at AWS.
Why DDoS Attacks are More Disruptive Than DoS Attacks
The most critical difference between DoS and DDoS attacks lies in the distributed nature of DDoS threats. Instead of a single machine launching traffic, a DDoS attack uses thousands – or even millions – of compromised devices across the globe. This creates a massive, coordinated wave of malicious traffic that overwhelms networks, servers, and applications far faster than traditional defenses can react.
This scale enables large-scale service outages, cripples’ essential online services, disrupts global businesses, and can even knock down major internet infrastructure providers. The combination of overwhelming bandwidth volume, multi-vector attack patterns, and botnet-driven coordination makes DDoS attacks.
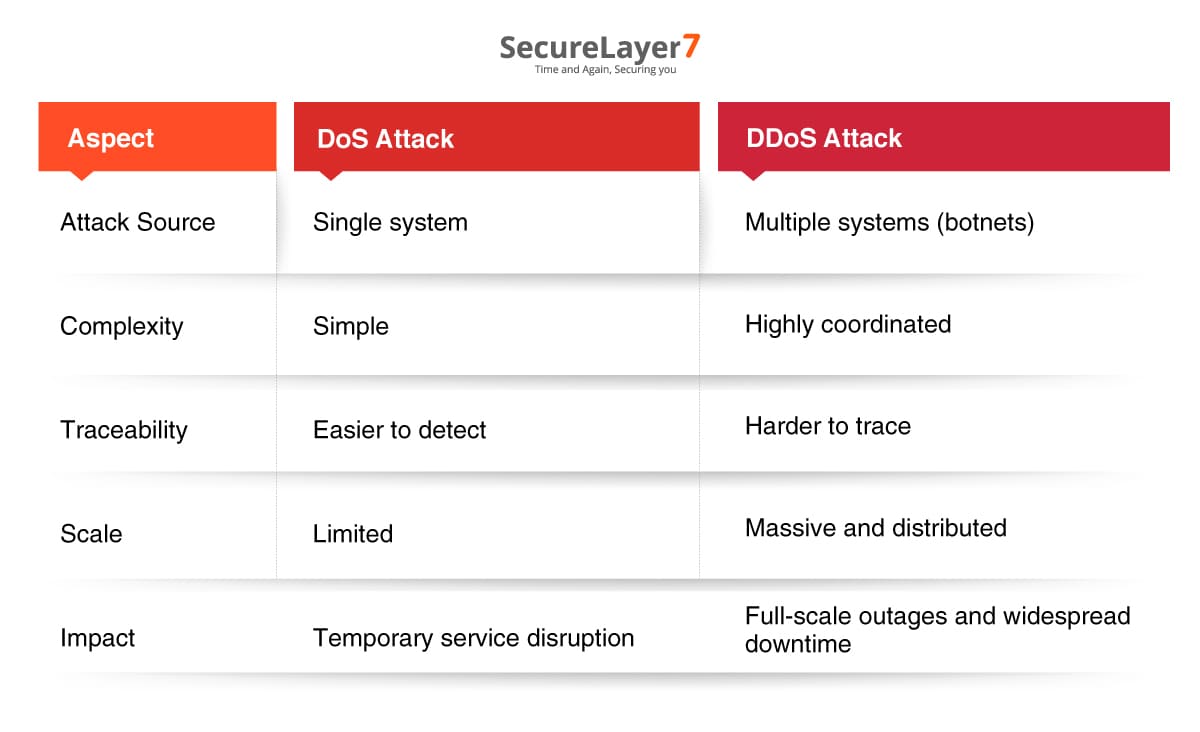
DoS vs DDoS: Core Differences
DoS and DDoS attacks aim to disrupt service availability, they differ significantly in scale, execution, complexity, and impact.
The table Following summarizes the key differences:
Distributed Nature of DDoS Changes its Scale, Detection, and Mitigation
The defining factor that separates DDoS from DoS attacks is distribution – the use of hundreds, thousands, or even millions of devices attacking simultaneously. This multi-origin attack model creates several major challenges:
1. Scale and Intensity
Because a DDoS attack leverages botnets or distributed sources, the total attack volume can reach hundreds of gigabits to multiple terabits per second, far exceeding the capacity of ordinary infrastructure.
Even large organizations with robust networks can be overwhelmed due to:
- Massive traffic spikes
- Concurrent multi-vector attacks
- Amplified packets from reflection attacks
2. Detection Difficulty
DoS attacks are easier to spot because their traffic originates from one IP or a small number of sources. Traditional security systems can quickly identify and block them.
DDoS attacks, generate traffic from:
- Distributed IPs
- Different geographic regions
- Randomized bots mimicking legitimate users
This makes it extremely difficult to distinguish between:
- Real user traffic
- Botnet-generated requests
- Malicious vs. normal spikes
3. Challenges in Mitigation
Mitigating a DoS attack often involves:
- Blocking the attacking IP
- Rate limiting
- Updating firewall rules
These measures are insufficient against DDoS attacks because:
- Blocking millions of distributed IPs is not practical
- Bots can rotate IPs dynamically
- Attackers can switch to multiple attack types mid-operation
- Traffic volumes may exceed local network capacity
4. Overall Impact
DoS attacks usually cause temporary slowdowns or short-term outages.
DDoS attacks, on the other hand, can cause:
- Prolonged downtime
- Infrastructure failures
- Service degradation across regions
- Financial loss and customer impact
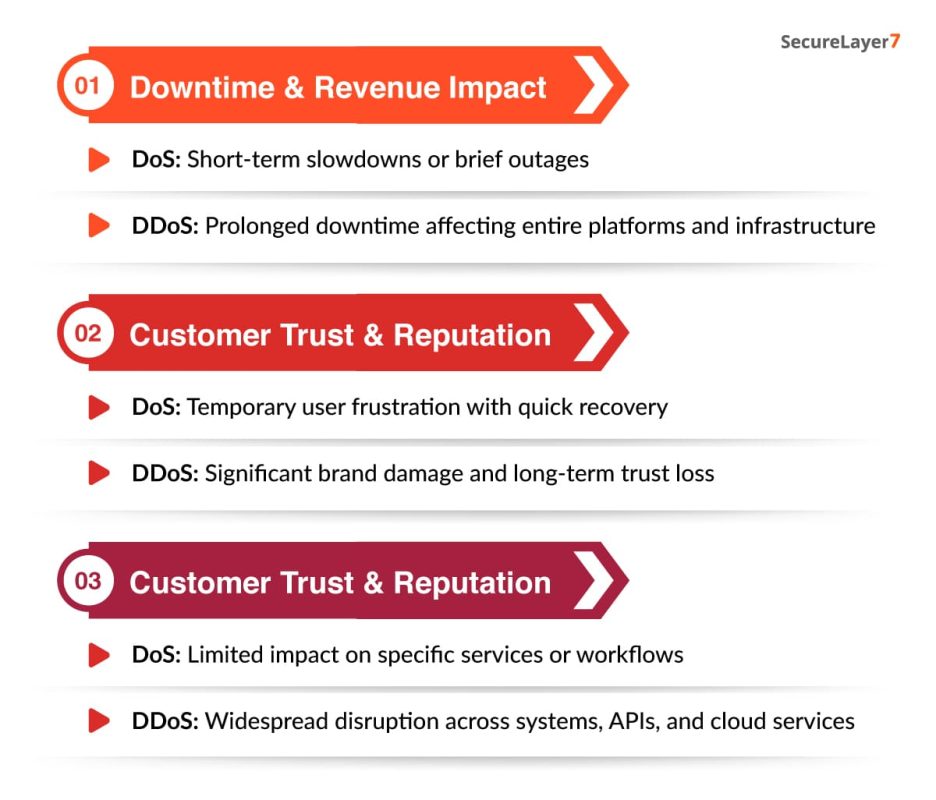
Impact of DoS vs DDoS Attacks
DoS and DDoS attacks can severely disrupt online services, but their impact differs significantly in scale and severity. While a DoS attack may cause localized slowdowns or short-term outages, a DDoS attack can trigger widespread downtime, financial loss, and major operational interruptions. Understanding the contrasting impacts helps businesses assess risk levels and strengthen their resilience against both forms of disruption.
Compare Real-World Business and Service Implications
DoS attacks typically lead to localized service slowdowns, brief outages, and minor disruptions that can interrupt workflows or delay customer transactions. They may frustrate users but are usually limited in scope and resolved quickly with basic mitigation.
DDoS attacks, on the other hand, create large-scale operational and financial impact. They can take entire platforms offline, interrupt global services, block customer access, halt critical business operations, and significantly damage brand trust.
DoS Attacks Still Matter
While DDoS attacks cause larger and more severe disruption, DoS attacks remain common, especially in smaller-scale exploitation scenarios. Threat actors (often individuals rather than organized groups) use DoS attacks to:
- Test for weaknesses
- Disrupt small businesses or personal websites
- Overwhelm outdated systems
- Launch nuisance-level attacks before escalating to more complex campaigns
Preventing DoS and DDoS Attacks
Protecting against DoS and DDoS attacks requires a proactive, layered security approach that focuses on early detection, traffic control, and resilient infrastructure. By combining tools like WAFs, DDoS protection services, rate limiting, and continuous monitoring, businesses can significantly reduce the risk of service disruption.
Key Defense Strategies
Mitigating DoS and DDoS attacks requires strong, multi-layered defenses that can detect threats early, filter malicious traffic, and keep services stable under pressure. By implementing essential measures like WAFs, DDoS protection platforms, rate limiting, continuous monitoring, and resilient infrastructure design, organizations can significantly reduce their exposure and maintain service availability even during attack attempts.
Web Application Firewalls (WAFs)
A Web Application Firewall acts as a protective barrier between your web applications and incoming traffic. It filters malicious requests, blocks suspicious behavior, and enforces security rules.
How WAFs help:
- Protect against HTTP floods and application-layer attacks
- Block known malicious IPs and bot patterns
- Reduce exposure to common vulnerabilities like SQL injection or XSS
DDoS Protection Services (e.g., Cloudflare, AWS Shield)
Specialized DDoS mitigation platforms are designed to absorb massive traffic surges and scrub malicious packets before they reach your servers.
Benefits include:
- Global edge networks to distribute and filter attack traffic
- Automatic detection of volumetric, protocol, and application-layer attacks
- Real-time mitigation to keep services online during attacks
Traffic Filtering and Rate Limiting
Rate limiting controls how many requests a client can send within a specific time frame. Traffic filtering blocks packets from suspicious or malformed sources. For implementation patterns and thresholds.
Why it works:
- Prevents brute-force request floods
- Limits repetitive connections from the same source
- Reduces the impact of low-level DoS attempts
Network Monitoring and Anomaly Detection
Continuous monitoring allows security teams to identify unusual traffic patterns early – before the system collapses under load.
Effective monitoring includes:
- Real-time analytics dashboards
- Alerts for sudden traffic spikes
- Behavioral analysis to identify bot-like activity
Load Balancing and Redundant Infrastructure
Distributing traffic across multiple servers or geographic regions makes it harder for attackers to overwhelm a single point of failure.
Advantages:
- Traffic is spread across multiple nodes
- Redundancy ensures service continuity even if one server is hit
- Cloud auto-scaling can spin up additional capacity during sudden surges
A Proactive, Not Reactive, Approach
The most successful DoS/DDoS defense strategies focus on prevention and preparedness rather than cleaning up after downtime occurs.
Businesses should:
- Continuously test systems for vulnerabilities
- Keep infrastructure updated
- Maintain strong traffic filtering rules
Conclusion
DoS and DDoS attacks differ in scale and complexity, but both can disrupt critical services, cause downtime, and impact business continuity. As DDoS attacks grow more sophisticated – with botnets, amplification methods, and multi-vector techniques – organizations must adopt layered defenses, continuous monitoring, and proactive security practices to stay resilient.
Strengthening your security posture before an attack occurs is essential. SecureLayer7 provides expert DDoS resilience planning, penetration testing, and comprehensive security assessments to help businesses identify vulnerabilities and reinforce their infrastructure. To stay protected in an evolving threat landscape.
Partner with SecureLayer7 and secure your digital environment with confidence.
Frequently Asked Questions (FAQs)
A DoS attack comes from a single source that floods a target with requests, while a DDoS attack uses multiple infected systems (botnets) to overwhelm the target, making it harder to block or trace.
A DDoS attack is more dangerous because it’s distributed across many systems, creating massive traffic volumes that can take entire networks offline.
Examples include Ping of Death, SYN Flood (DoS), and large-scale attacks like the GitHub DDoS (2018) or Dyn DNS attack (2016), which disrupted major online services.
Businesses can prevent such attacks by using Web Application Firewalls (WAFs), DDoS protection services like Cloudflare or AWS Shield, rate limiting, and continuous network monitoring.
No solution can guarantee complete prevention, but proactive measures such as real-time traffic filtering, cloud-based mitigation, and redundancy significantly reduce the risk and impact.



