RegPwn (CVE-2026-24291) is a critical Windows Registry vulnerability that exposes enterprise systems to privilege escalation and potential system compromise. This flaw targets how Windows handles registry operations, allowing attackers to manipulate registry keys and gain unauthorized access to sensitive system components.
Exploitation of this vulnerability can lead to full system control, data theft, and lateral movement across enterprise networks. Understanding how CVE-2026-24291 works, its impact, and mitigation strategies is essential for organizations aiming to strengthen endpoint security and defend against advanced cyber threats.
What is RegPwn (CVE-2026-24291)?
RegPwn (CVE-2026-24291) is a critical vulnerability identified in early 2026 that affects a core component of the Windows operating system. It resides in the Windows Configuration Manager, the kernel-level subsystem responsible for managing and processing the Windows Registry.
Because the registry serves as the central store for system and user configurations, this flaw poses a high-risk threat to Windows environments. A weakness at this level can impact how the entire system operates, making it especially dangerous if exploited.
Vulnerability Type
The primary classification for RegPwn is Local Privilege Escalation (LPE).
- The Mechanism: An attacker starting with User or Guest privileges can trigger the memory corruption.
- The Result: The exploit allows the attacker to gain SYSTEM-level privileges the highest level of authority on a Windows machine. Once achieved, the attacker has total control over the OS, including the ability to view, change, or delete data and create new accounts with full administrative rights.
Affected Windows Components and Environments
The vulnerability is deeply embedded in ntoskrnl.exe (the Windows Kernel), making it widespread across the Microsoft ecosystem.
- Affected Operating Systems:
- Windows 11 (Versions 22H2, 23H2, and 24H2)
- Windows 10 (Version 22H2 and Enterprise LTSC)
- Windows Server 2022 and 2025
- Target Components: The Windows Configuration Manager and any service that frequently interacts with registry transactions, such as the Local Security Authority Subsystem Service (LSASS).
Technical Deep Dive of the RegPwn Vulnerability
The technical architecture of RegPwn (CVE-2026-24291) makes it a particularly potent threat in Windows environments. Unlike simple configuration errors, this vulnerability stems from a fundamental flaw in how the Windows kernel handles security-critical resources during high-privilege operations.
Root Cause Analysis: Improper Permission Handling
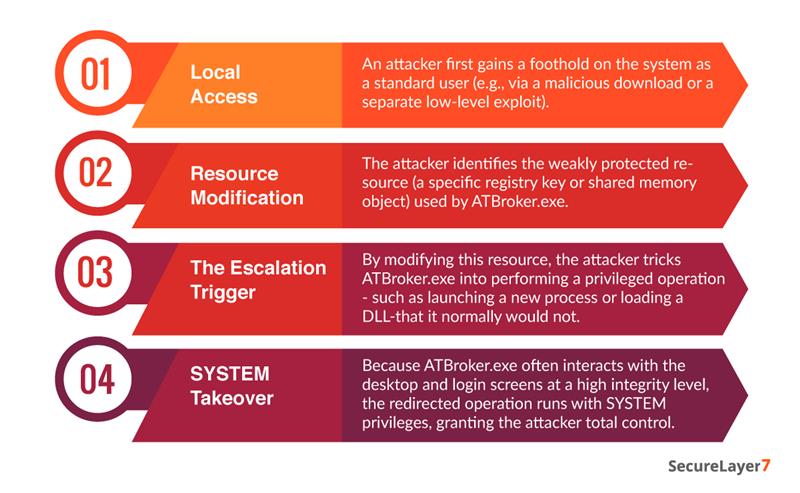
The root cause of RegPwn is an Incorrect Permission Assignment (CWE-732) within the Windows Accessibility Infrastructure, specifically involving the ATBroker.exe (Assistive Technology Broker) component.
- The Flaw: The system specifies permissions for a security-critical resource in a way that allows it to be modified by unauthorized, low-privileged actors.
- The Broker Vulnerability: ATBroker.exe acts as a bridge between the user and high-privilege accessibility tools. Because the permissions on the communication channel or shared resources it uses are too permissive, a standard user can inject instructions that the Broker then executes with elevated authority.
How Attackers Exploit Registry Operations
The vulnerability is officially categorized under Accessibility Infrastructure; it heavily involves Registry abuse to maintain state and trigger the escalation.
Vulnerable Components & System Calls
The vulnerability is centered around the interaction between user-mode applications and kernel-mode accessibility services.
- Primary Executable: ATBroker.exe
- System Mechanism: Improper use of Access Control Lists (ACLs) on objects that facilitate inter-process communication (IPC).
- Vulnerability Type: Elevation of Privilege (EoP). Unlike a Remote Code Execution (RCE) that happens over the internet, this requires the attacker to already be on the box.
Preconditions Required for Exploitation
For an attacker to successfully “pwn” a system using CVE-2026-24291, several conditions must be met:
- Authenticated Local Access: The attacker must have a valid set of credentials (even if they are low-privileged) and be able to execute code locally on the target machine.
- Presence of ATBroker: The Windows Accessibility features must be in a state where the ATBroker process can be invoked or is already running.
- Unpatched System: The system must be running a version of Windows 10, 11, or Server (2012-2025) that has not yet applied the March 10, 2026 security updates.
- Low Attack Complexity: Interestingly, this exploit is rated as Low Complexity, meaning it does not require advanced timing (like a race condition) or specific hardware configurations; a simple script is often enough to trigger the escalation.
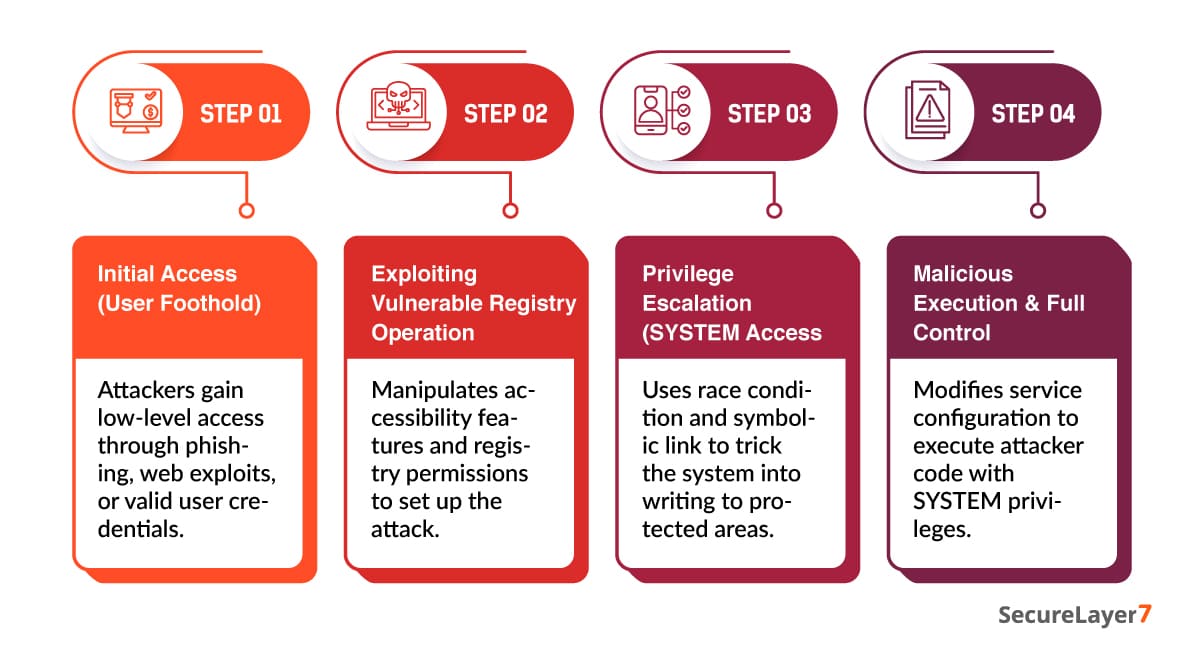
Attack Mechanics of RegPwn Exploitation
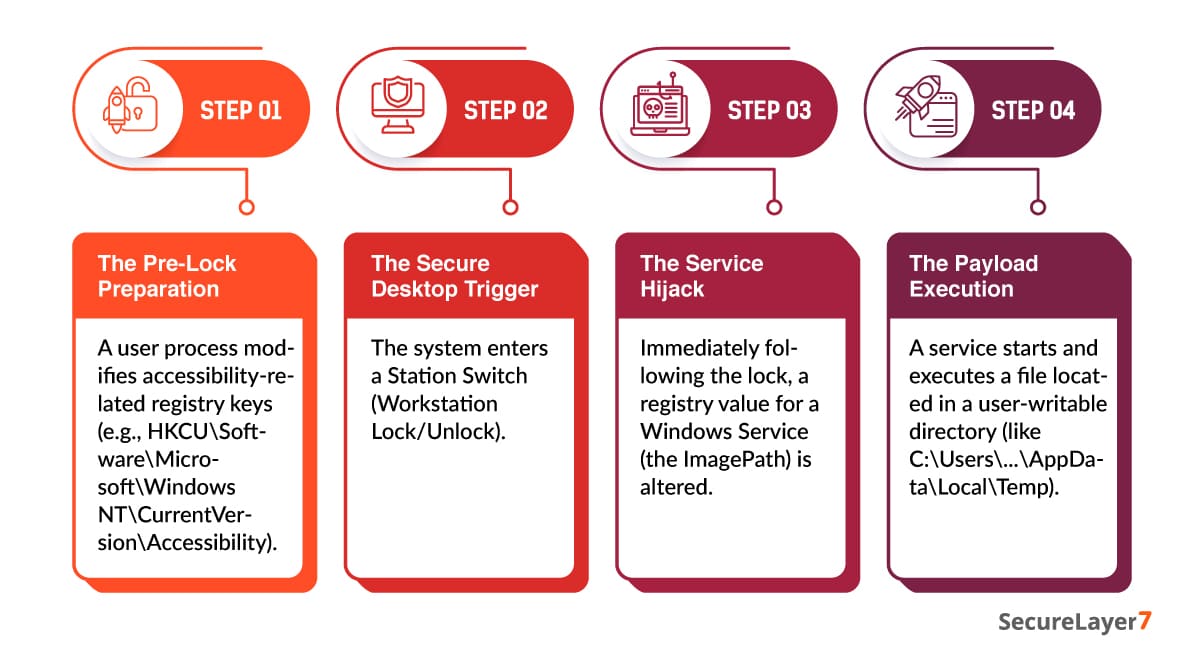
Understanding the exploitation of RegPwn (CVE-2026-24291) requires a look at how Windows handles its Secure Desktop and accessibility features. Unlike many exploits that rely on complex memory corruption, RegPwn is a logic-based privilege escalation that abuses the trust between a user-controlled environment and a system-controlled one.
Impact of CVE-2026-24291
The impact of CVE-2026-24291 (RegPwn) is classified as Critical because it strikes at the fundamental trust model of the Windows Operating System. When an attacker successfully exploits this vulnerability, they move from being a restricted guest on a machine to having the same authority as the OS itself.
Privilege Escalation to SYSTEM Level
CVE-2026-24291 (RegPwn) is considered critical because it breaks a core trust boundary in the Windows operating system. Once exploited, an attacker can move from a low-privileged account to SYSTEM-level access, gaining full control over the machine.
With this level of access, attackers can bypass security controls, disable Endpoint Detection and Response (EDR) tools, and stop security logging – making their activity hard to detect. They can also extract sensitive credentials from processes like lsass.exe, which can be used to move deeper into the network and compromise additional systems.
Unauthorized Registry Manipulation
The vulnerability also allows unauthorized changes to the Windows registry, giving attackers control over critical system settings. By modifying registry keys tied to Group Policy or security configurations, they can disable firewalls, weaken protections, or bypass User Account Control (UAC). This effectively lowers the system’s defenses and makes further compromise easier.
Execution of Arbitrary Code
RegPwn can also enable arbitrary code execution, often through service hijacking. Attackers can replace legitimate service paths with malicious binaries, which then run with elevated privileges. Once executed, this can lead to complete system compromise.
Persistence Mechanisms
Beyond the initial compromise, RegPwn can also be used to maintain long-term access. Attackers can create hidden startup entries or use WMI-based scripts tied to the registry to persist even after a system reboot. This makes the vulnerability particularly dangerous in enterprise environments, where undetected access can last for extended periods.
Detection and Indicators of Compromise (IoCs)
Detecting RegPwn (CVE-2026-24291) requires a shift from signature-based detection (searching for specific malicious files) to behavioral monitoring. Because the exploit manipulates legitimate system processes to perform unauthorized registry writes, security teams must look for anomalies in the relationship between user processes and system hives.
Suspicious Registry Access Patterns
The primary indicator of a RegPwn attempt is the Bait-and-Switch manipulation of registry keys during a transition to the Secure Desktop.
- Registry Symbolic Link Creation: Monitor for the creation of registry keys that point to other keys (Symlinks) within the HKEY_CURRENT_USER hive, especially those created just before a workstation lock or UAC prompt.
- Unauthorized HKLM Writes: Any process initiated by a standard user that results in a modification to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services is a high-priority Red Flag.
- Oplock Activity: High frequencies of Opportunistic Locks (oplocks) placed on registry hive files (NTUSER.DAT) by non-administrative processes.
Unusual Privilege Escalation Attempts
RegPwn allows a Medium Integrity process to suddenly spawn a System Integrity process.
- Parent-Child Process Mismatches: Watch for services.exe or svchost.exe spawning a command shell (cmd.exe or powershell.exe) or an unknown binary immediately after a registry modification.
- ATBroker Anomalies: Monitor ATBroker.exe (Windows Assistive Technology Broker). If this process is triggered frequently or launches unexpected sub-processes, it may be the engine for the escalation.
- Rapid Integrity Jump: A single user session showing a sudden jump from Medium Mandatory Level to System Mandatory Level without a corresponding, logged administrative login.
Logs and Telemetry to Monitor
To catch RegPwn, you must configure your logging to capture granular registry and process events.
Windows Event Logs
- Event ID 4657: A registry value was modified. (Focus on the HKLM hive).
- Event ID 4688: A new process has been created. (Look for cmd.exe running as SYSTEM).
- Event ID 4673: A privileged service was called. (Monitor for calls to sensitive accessibility services).
Sysmon (System Monitor)
Sysmon provides the Ground Truth needed to link registry changes to specific processes:
- Event ID 1 (Process Creation): Look for suspicious command lines involving reg.exe or powershell -Command “Set-ItemProperty…”.
- Event ID 12, 13, 14 (Registry Events): These are critical. Monitor for any “Registry Key Create/Delete/Set” actions on paths like \REGISTRY\MACHINE\SYSTEM\CurrentControlSet\Services.
Behavioral Indicators in EDR Systems
Modern Endpoint Detection and Response (EDR) tools should be tuned to look for these specific chains of behavior:
Mitigation and Remediation: Take it from Microsoft or credible website
Effective mitigation of vulnerabilities like RegPwn (CVE-2026-24291) requires a combination of timely patching, access control, and continuous monitoring. Organizations must prioritize applying official security updates while also strengthening registry permissions to reduce the attack surface.
Following steps help minimize exploitation risks and ensure long-term system security.
Microsoft Security Patch Details and Update Guidance
Microsoft released an out-of-band security update on March 10, 2026, to address the improper permission handling in the Windows Configuration Manager and Accessibility Infrastructure.
- The Fix: The patch updates ntoskrnl.exe and ATBroker.exe to strictly validate the integrity of registry hives during Station Switches (e.g., locking the screen). It also enforces a hard link and symbolic link check to ensure system processes do not follow unauthorized redirections created by low-privileged users.
- Update Guidance: All versions of Windows 10, 11, and Windows Server 2022/2025 are affected. Security teams should prioritize Domain Controllers and VDI/Multi-user environments where privilege escalation is most dangerous.
Steps to Apply Patches and Verify Remediation
To remediate the vulnerability effectively, organizations should:
- Identify affected systems using vulnerability scanning tools.
- Apply the latest Windows security updates via Windows Update, WSUS, or enterprise patch management solutions.
- Restart systems where required to complete patch installation.
- Validate remediation by re-scanning systems and confirming that CVE-2026-24291 is no longer detected.
Temporary Mitigations
If immediate patching is not feasible, organizations should implement temporary controls to reduce risk. These include:
- Limiting user privileges and enforcing the principle of least privilege.
- Monitoring registry changes for suspicious activity.
- Disabling or restricting access to vulnerable components where possible.
- Using endpoint detection and response (EDR) tools to identify exploitation attempts.
Restricting Registry Permissions and Access Control
Strengthening registry security is critical in mitigating risks associated with this vulnerability. Organizations should:
- Audit registry permissions and remove unnecessary write access
- Enforce strict access control policies on sensitive registry keys
- Use Group Policy to manage and restrict registry modifications
- Regularly monitor and log registry activity for anomalies
Conclusion
RegPwn (CVE-2026-24291) highlights how Windows Registry vulnerabilities can lead to privilege escalation, persistence, and full system compromise. As attackers increasingly exploit OS-level weaknesses, timely patching, continuous monitoring, and strict access controls are critical to minimizing risk.
Adopting a layered security approach – combining vulnerability management, EDR, and secure configurations helps organizations stay resilient against emerging threats. With SecureLayer7, enterprises can proactively identify risks, strengthen defenses, and ensure robust protection against advanced cyberattacks.
Stay ahead of vulnerabilities – secure your enterprise with SecureLayer7.
Frequently Asked Questions (FAQs)
RegPwn (CVE-2026-24291) is a Windows Registry vulnerability that allows attackers to exploit improper access controls and manipulate registry operations to gain unauthorized access or elevated privileges.
It is primarily a privilege escalation vulnerability caused by improper access control in registry handling, enabling attackers to perform actions beyond their intended permissions.
RegPwn impacts core Windows components by allowing unauthorized modification of registry keys, which can alter system behavior, weaken security controls, and potentially lead to full system compromise.
Yes, attackers can exploit RegPwn to escalate privileges from a low-level user to SYSTEM-level access, gaining full control over the affected system.
Organizations can mitigate the risk by applying Microsoft security patches, enforcing strict registry access controls, monitoring system activity, and implementing security solutions such as EDR to detect and prevent exploitation.