In 2019, Tribune Publishing newspaper in the US found itself in a weird situation when its systems locked, and Saturday editions of major newspapers were stalled. The attack didn’t stop at Tribune’s, The New York Times and The Wall Street Journal also shared the same fate. Initially, it looked like a routine production issue in San Diego and Florida, security teams quickly identified the culprit was Ryuk ransomware.
The incident was a grim reminder that ransomware wasn’t just a technical problem. It could ripple through industries, delay information reaching millions, and interrupt the everyday rhythms. In this blog, we’ll dive deeper to understand Ryuk ransomware, how it works, and its impact and ways to avoid it.
What is Ryuk Ransomware?
Ryuk ransomware, first detected in 2018, is a destructive malware strain created by the Russian cybercriminal group Wizard Spider. It’s a special kind of ransomware that targets large Microsoft Windows cybersystems by encrypting data on the victim systems. By making data inaccessible for organizations, it demands ransom in Bitcoin. Ryuk is primarily used by Russian and Ukrainian cybercriminal groups. They target large organizations and not individuals.
The modus operandi of Ryuk is simple: it starts by infiltrating targets through initial access vectors like phishing emails or vulnerabilities, using intermediate malware such as Emotet or TrickBot.
What makes it lethal is that once they enter the network, Ryuk uses sophisticated tactics of lateral movement, privilege escalation, and deletion of system backups and shadow copies to amplify the impact. The ransomware encrypts files using a combination of RSA-4096 and AES-256 encryption, which makes recovery of data almost impossible.
Unlike opportunistic strains like WannaCry or CryptoLocker, Ryuk can be deployed manually and can be easily tailored to the victim’s environment. It can evade detection with ease. These capabilities make it extremely lethal and organizations struggle to defend against its tactics.
How Ryuk Works and Infects
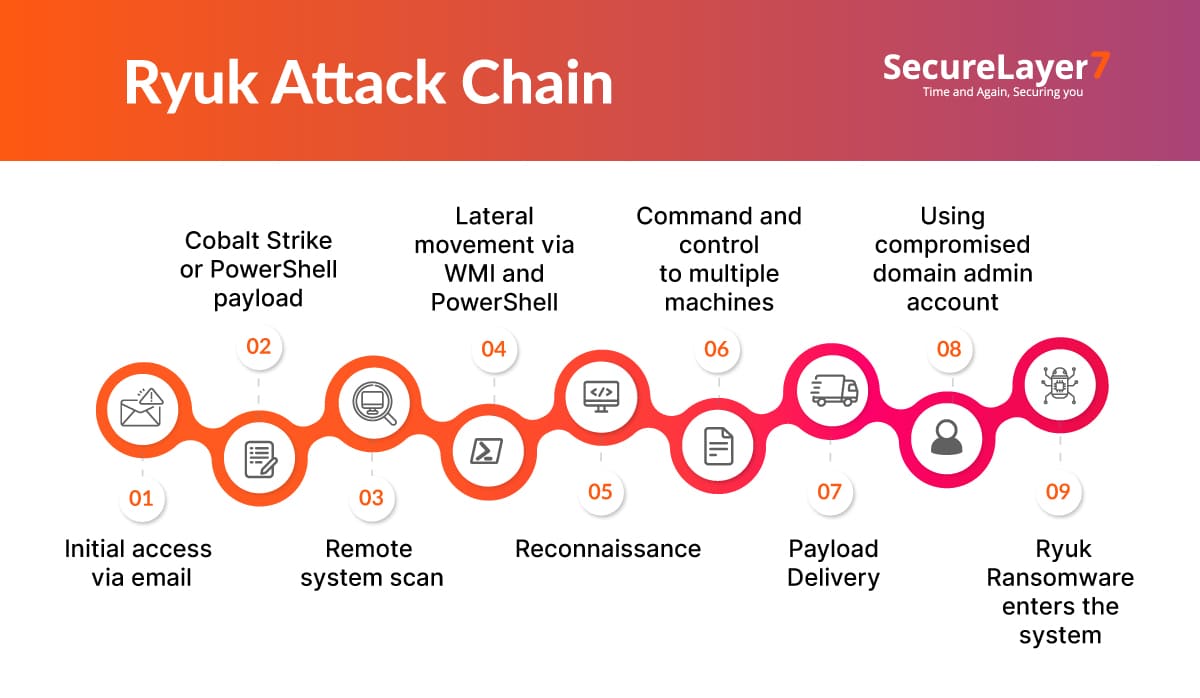
Ryuk uses a well polished multi-stage strategy that gives attackers time to understand a network before they launch the final blow. Unlike fast-moving ransomware families, Ryuk prefers patience and control. These are the qualities that make it extremely difficult to detect early.
Let’s understand this in a bit more detail. First of all, we will explain:
- Attack vectors used in creating Ryuk ransomware
- Encryption process that makes it extremely deadly
- Ryuk ransomware notes and messages
1. Common Infection Vectors
Ryuk ransomware attacks usually begin with phishing. Attackers craft emails, seemingly coming from trusted organizations, that resemble real business communication, such as fake invoices, account alerts, or urgent requests from supposed vendors. When an employee opens the attachment or enables macros, the virus enters the system. In most cases, the payload used is Emotet or TrickBot to avoid early detection.
Poorly secured Remote Desktop Protocol (RDP) is another common entry point for Ryuk ransomware operators. They use brute-force attempts, or already stolen credentials to infiltrate RDP services. They run freely without bypassing firewalls or bypassing endpoint defenses.
The usual attack path is Emotet, followed by TrickBot, and then goes into the Ryuk chain. It works like a well-oiled criminal assembly line:
- Emotet installs itself first, phones home, and prepares the host.
- TrickBot follows, gathering credentials, scanning network shares, and identifying machines worth targeting.
- Only after the attackers understand the environment, they deploy Ryuk manually.
2. Encryption Process and Network Impact
Now when Ryuk is finally deployed, it follows a methodical behavior. Before encrypting anything, it shuts down many services and processes including antivirus tools, database services, and backup applications.
Ryuk uses a dual-encryption system using AES-256 for file data and RSA-4096 hashing for locking the AES keys. Each file gets its own AES key, which is then encrypted using the attacker’s RSA public key.
The whole objective of Ryuk is to make the recovery process painful. For example, it deletes every Windows Volume Shadow Copy generated by third-party backup software. It even uses an obscure “vssadmin resize shadowstorage” command to forcefully remove backup files to escape deletion, destroying organizations the last line of defense.
But Ryuk doesn’t stop at the local machine level, It hunts for anything connected to the network: shared drives, mapped folders, administrative shares. This combination of stealth, network reach, and deliberate sabotage is why Ryuk is counted among the most destructive ransomware families. It doesn’t just lock files; it disrupts business continuity, strains incident response teams, and forces organizations into costly, time-consuming recovery efforts.
Historically, Ryuk itself was not self‑propagating. But, their newer versions have shown worm-like behavior and they automatically spread in the network using Remote Procedure Call (RPC). Ryuk constantly scans private IP ranges (10.x.x.x, 172.16.x.x, 192.168.x.x) looking for new hosts.
Whether it’s a Windows, Linux, NAS device, if a drive is accessible, Ryuk can encrypt it. This broad scanning helps attackers cripple not just one machine, but entire departments or facilities.
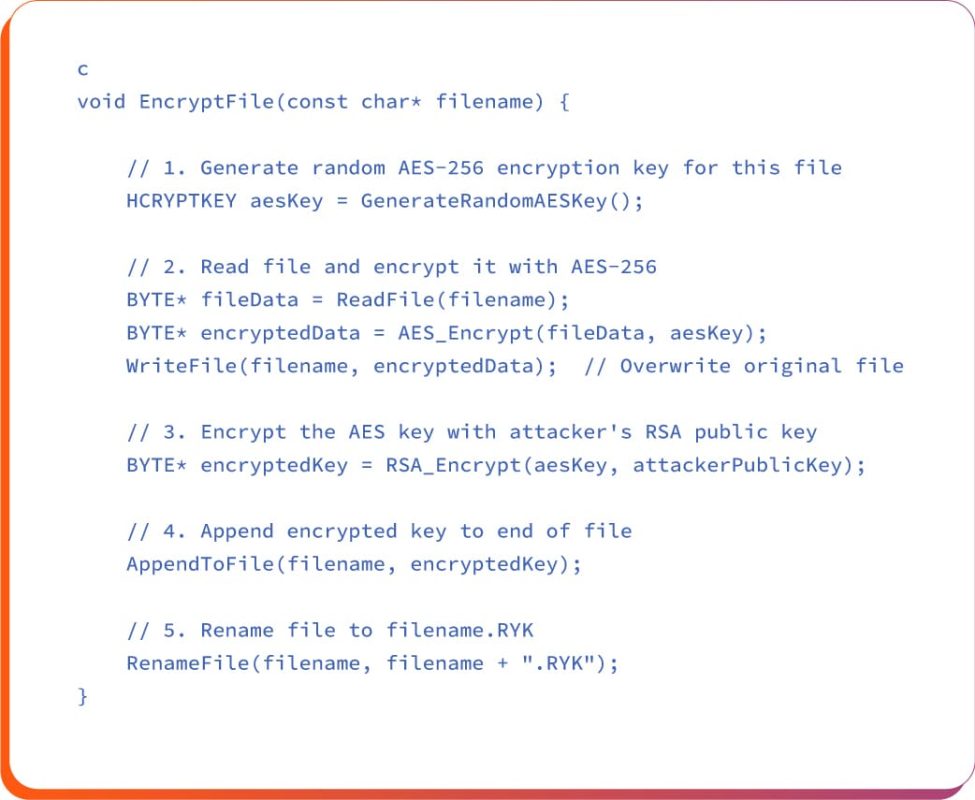
A close observation of the above code snippet reveals why you can’t recover it:
- Your file is locked with AES-256 (impossible to break).
- The key to unlock it is also locked with RSA-4096 (also impossible to break).
- Only the attacker has the master key to unlock your lock.
- Without paying the ransom, you have no way to get that master key.
3. Ryuk Ransom Note and Message
Once the encryption cycle gets over, victims receive a “RyukReadMe.txt” file inside every affected directory. The note includes contact instructions and payment demands. Ryuk avoids encrypting certain core system files, not out of mercy, but to make sure the machine stays functional enough for victims to read the note and pay the ransom.
Example of a ransom note format:
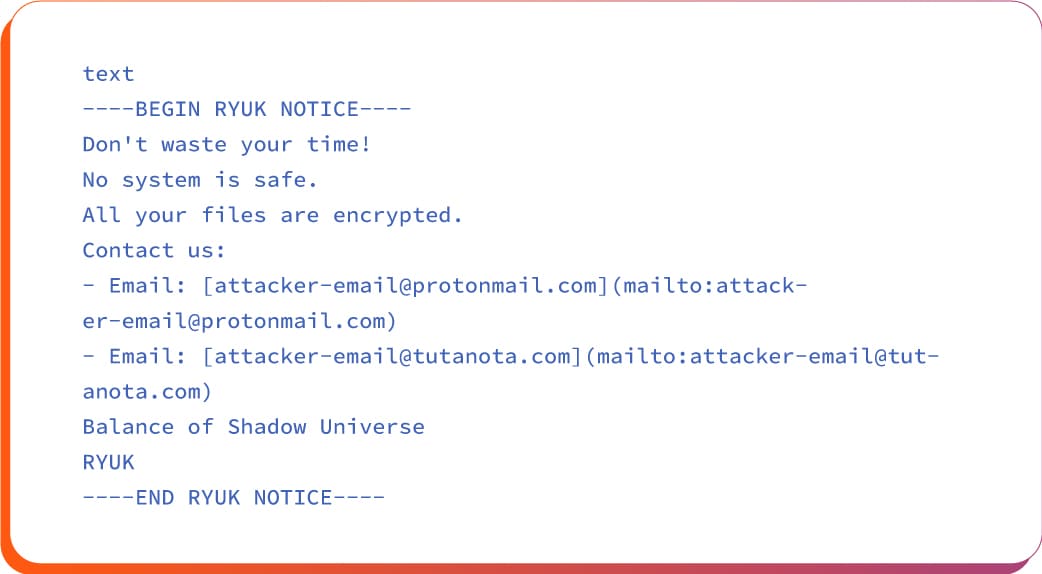
Current Ryuk variants deliberately omit ransom amounts and Bitcoin wallet addresses. They ask for victims to contact attackers via email to receive payment instructions.
That provides them more elbow room to negotiate amounts based on the victim’s perceived financial capacity.
Real-World Impact and Notable Victims
Here is a list of two major Ryuk ransomware attack incidents:
Example #1 East Asia Securities Broker (2023)
This broker suffered a Ryuk ransomware attack initiated by a targeted phishing email that compromised employee credentials. The attackers encrypted critical trading platforms and client databases, causing a complete halt in trading operations and client services. Financial losses exceeded $5 million, alongside reputational damage and client trust erosion.
The attack could have been prevented with robust employee cybersecurity training, implementation of multi-factor authentication on key accounts, strict email filtering to block phishing attempts, and regular system monitoring for suspicious activity.
Example#2: United Health Services (2020)
Ryuk ransomware attacked UHS through exploited Remote Desktop Protocol (RDP) vulnerabilities, spreading rapidly to over 250 hospitals in the US. This attack disrupted essential patient care, surgeries, and billing processes, forcing prolonged downtime and emergency operations mode across healthcare facilities.
It could have been avoided by implementing secure RDP with strong passwords and VPN access, network segmentation to limit lateral movement, timely patching of vulnerabilities, maintaining offline backups, and comprehensive incident response planning to reduce impact swiftly.
How to Detect Ryuk Attack
Identifying the presence of Ryuk ransomware infection is not easy as the group is very smart and its success depends on how it evades detection in the early stage. However, there are several signals like precursor malware activity (Emotet or TrickBot), suspicious Registry modifications, unusual process behavior, which deserves scrutiny.
Ryuk maintains persistence by altering the Windows Registry in ways that appear very normal. It creates run keys with deceptive names like “svchos” that are almost identical to the svchost.exe.
Now, since Ryuk is already in the system, its payload processes such as “rdpclip.exe” (Remote Desktop Clipboard) and “vmtoolsd.exe” (VMware Tools). This process-injection approach is a key trait of Ryuk’s ransomware. It hides inside legitimate processes to stay under the radar.
In addition, Ryuk also uses several methods to move laterally by pushing Group Policy shutdown scripts, storing its binaries in the Public user directory: (C:\Users\Public), and sending Wake-on-LAN “magic packets”.
These tactics allow the ransomware to spread quietly and prepare the environment for widespread damage. There are other tell-tale signals such as:
- Volumes of abnormal network activity, such as lateral movement via PsExec or WMI,
- Failed RDP login attempts followed by successful login,
- Files being encrypted with the “.ryuk”, “.crypt”, or “.R4A” extension.
Early detection hinges on monitoring for TrickBot/Emotet, unauthorized Registry changes, and sudden spikes in SMB/C$ share encryption attempts.
How to Prevent Ryuk Ransomware Attack
Ryuk ransomware attacks can be prevented by implementing some practices related to technology, strategy, and internal measures:
1. Patch Management & System Hardening
- Apply security patches immediately to OS, software, and firmware on all systems as Ryuk operators actively exploit known CVEs in unpatched systems.
- Enable auto-update settings on all critical systems and software to minimize attack surface.
- Conduct regular configuration audits across all OS versions (Windows XP, Vista, Windows 7–11) to close local privilege-escalation paths.
- Disable or restrict the Local Administrator Account to prevent credential misuse during lateral movement.
2. Access Control & Network Segmentation
- Implement zero-trust architecture with least-privilege access policies.
- Segment networks by isolating sensitive data servers from email environments and public-facing systems; segment by function/department to contain spread.
- Disable unused RDP ports and enforce strong RDP authentication; monitor RDP logs for failed login attempts followed by successful ones.
- Restrict lateral movement by controlling SMB/C$ share access; remove excessive file/folder permissions for non-administrative users.
- Implement MFA on all user accounts, VPN access, and administrative portals, especially for RDP and email systems.
- Enforce strong password policies (12+ characters, mixed case, numbers, symbols) and rotate credentials every 60–90 days.
3. Backup & Recovery Strategy
- Always maintain immutable, offline backups (air-gapped or immutable cloud storage) that cannot be accessed or deleted by malware; test restore procedures monthly.
- Store backup credentials separately from production systems; use different administrative accounts for backup operations.
- Enable versioning and retention policies on backup systems; Ryuk deletes shadow copies, so ensure backups exist outside Volume Shadow Service.
- Implement 3-2-1 backup rule: 3 copies, 2 media types, 1 offsite location.
4. Endpoint & Network Security
- Deploy advanced EDR solutions with behavioral analysis to detect ransomware-like activities (file encryption, shadow copy deletion, service termination) in real time.
- Install anti-malware/anti-ransomware solutions with rollback capability (SentinelOne, CrowdStrike, Microsoft Defender with advanced threat protection) to restore encrypted files post-infection.
- Use DLP tools to monitor and alert on suspicious data-access patterns.
- Deploy firewall rules to block outbound C2 traffic; monitor DNS queries for known Ryuk C2 domains.
5. User Security Training
- Conduct mandatory, quarterly cybersecurity awareness training focused on:
- Identify social-engineering attempts from threat actors posing as IT staff.
- Report suspicious emails/links without opening them.
- Maintain safe credential hygiene and handling of sensitive company data.
- Simulate phishing campaigns quarterly to identify and re-train high-risk users.
Incident Response & Recovery Best Practices
Handling the Ryuk ransomware attack is not easy, still the following measures will help deal with the situation:
1. Immediate Actions
- Isolate infected systems and any networked devices from the network (wired and wireless) to stop lateral spread.
- Disable VPN access for compromised user accounts to block remote lateral movement.
- Preserve evidence. Do not restart, shut down, or modify infected systems; preserve memory dumps, event logs, and ransom notes for forensic analysis.
- Activate incident response team: engage internal SOC or external incident-response provider (CrowdStrike, Mandiant, Coveware).
- Alert leadership and legal teams. Notify CISO, executive management, legal counsel, and insurance provider.
2. Early Investigation
- Preserve encrypted files and ransom notes as forensic evidence.
- Check Autoruns output for suspicious startup programs (registry keys like svchos).
- Analyze network logs (firewall, DNS, proxy) to identify lateral-movement paths and C2 communication patterns.
- Determine which systems/data are encrypted via file-system scans and backup integrity checks.
3. Containment & Eradication
- Identify the initial compromise vector. Trace entry point (phishing, RDP, supply chain) via event logs, email gateways, and EDR tools.
- Hunt for persistence mechanisms: search for Registry Run keys (HKCU\Software\Microsoft\Windows\CurrentVersion\Run, entries named svchos), scheduled tasks, and WMI event subscriptions.
- Quarantine malware. Isolate suspected Ryuk binaries (typically in **C:\Users\Public**) in a sandbox environment.
- Wipe and rebuild infected systems: perform clean OS reinstall from trusted media; do not restore from backups until systems are hardened.
- Reset all credentials used on compromised systems.
4. Recovery & Restoration
- Ensure all systems are patched, hardened, and threat-free before restoring data.
- Restore systems in groups and test each batch for stability and integrity.
- Run file-integrity checks and automated scans to ensure no remnants of infection.
- Create incident reports covering attack vectors, lateral-movement paths, dwell time, and scope of compromise.
5. Post-Incident Hardening
- Patch vulnerabilities exploited during initial compromise; disable weak protocols (SMBv1, legacy RDP).
- Conduct forensic investigation to detect and remove persistence mechanisms (WMI subscriptions, scheduled tasks, SSH keys).
- Deploy continuous monitoring on previously compromised systems and network segments for 90+ days.
6. Long-Term Resilience Measures
- Conduct quarterly tabletop exercises simulating Ryuk attacks.
- Maintain air-gapped backup copies updated monthly; test restoration annually.
- Subscribe to threat-intelligence feeds on Ryuk variants, C2 infrastructure, and emerging TTPs.
Ryuk attack mitigation in 3 steps
Ryuk attacks often blindsides organizations, leaving them with no option but to pay a large ransom. Still, there are a few immediate steps that can reduce damage and support cleanup once an attack is detected.
1. Malware unpacking: After spotting a Ryuk infection, alert your IT team so they can unpack the malware with tools like x64dbg inside a secure, isolated virtual environment.
2. Quarantine & patch: Once unpacked, quarantine the malware in a safe location. Then begin patching and cleaning every system it may have touched. Ryuk spreads laterally, so sanitizing each machine is essential to prevent reinfection.
3. Contact authorities: Agencies like the FBI actively track Ryuk due to its impact on national security and critical sectors. Even if your internal team is skilled, notifying law enforcement should be a required part of your incident response plan.
Closing thoughts
Ryuk remains one of the most dangerous ransomware families targeting large enterprises and the public sector. Without strong data protection and system-hardening practices, it can move quickly, sometimes with human guidance, sometimes automatically with newer variants.
So, security teams need to put a robust proactive defense mechanism, such as anti-phishing training to advanced anti-malware tools, to avoid such incidents. Schedule a call with us to know more how SecureLayer7 can help you deal with such ransomware attacks.



